Alternative Choices for You
|
|
From $6.67 |
ProPrivacy.com Score
9.6 out of 10
|
Visit Site Read review |
|
|
From $3.69 |
ProPrivacy.com Score
9.4 out of 10
|
Visit Site Read review |
|
|
From $2.19 |
ProPrivacy.com Score
8.6 out of 10
|
Visit Site Read review |
CryptoStorm’s Pricing and Plans
CryptoStorm’s pricing structure is somewhat unusual. The base cost is $6 USD per month, with minor savings for buying a longer subscription. Buying an annual subscription, for example, saves just $6 over paying on a monthly basis.
What buying a subscription does do, however, is increase the number of simultaneous connections you are permitted. For example, an annual subscription lets you connect up to four devices at the same time.
It is also possible to buy bundles of one-month subscriptions. These bundles, however, do not line up with the regular subscription options. For example, you can buy six month or annual subscriptions, but five-month or 11-month bundles.
This appears to be a deliberate attempt to obfuscate the fact that bundles cost around the same price as subscriptions, despite offering only a single connection (for example $52/12 = $4.33, while $48/11 = $4.36).
It is also possible to pay $1.86 for a week’s subscription, which is handy for trialing the service. This option is particularity welcome as CryptoStorm does not offer a free trial or money-back guarantee.
The existence of a free “Cryptofree” node is not well advertised and was news to me when I first ran the client. There are no data limits on this free server, but the service is very slow (see speed tests later on in this review).
Payment is made via CryptoStorm’s much-hyped token system (see below). Tokens can be purchased directly from the CryptoStorm website using PayPal or third party payment processor Stripe.
Stripe accepts payment using credit/debit card, including prepaid debit cards. It also accepts payment in Bitcoin. If payments are made via Stripe then CryptoStorm will have no record of who made the payments, although Stripe will.
Tokens can also be purchased from third-party resellers. Remember that no matter how anonymous the payment method used, CryptoStorm will still know your real IP address.
CryptoStorm’s VPN Features
CryptoStorm offers the following features:
- No logs
- Payment via temporary hashed tokens sold by third-party resellers (in theory)
- Up to four simultaneous connections (for one-year+ subscriptions)
- DNSCypt and DNSChain support
- Accepts Bitcoin and prepaid debit cards (via Stripe)
- Randomised port selection (Windows only)
- Servers in nine countries
- OpenVPN protocol
- P2P torrenting is permitted
Servers are mainly located in Europe, but there are also some in the US and Canada. for more information about torrenting, see our best VPN for torrent sites guide.
CryptoStorm Token payment
By far the most unique and hyped feature offered by CryptoStorm is the ability to pay using hashed tokens. In theory, these can be purchased through third-party resellers. This ensuring that, as far as CryproStorm is concerned, the payments are anonymous. As such, tokens are not associated with an account. Each token simply authorizes you to use the service for a certain amount of time.
The idea seems for these tokens to be traded, swapped, and sold by third-party resellers. In theory this is not a bad idea, although I do not see how it is any more anonymous than VPNs that accept payment using store cards or cash. In practice, however, the system seems to be something of a mess. You can buy tokens directly from a CryptoStorm website, and can do so anonymously using Bitcoin.
The Resellers link on the main webpage, however, triggers an HTTPS certificate warning. If you ignore the warning, you are taken to CryptoStorm forum page that purportedly lists resellers. But many of the links on this page are very old, and not a single reseller link I clicked on worked (indeed clicking on many such links also generated certificate warnings).
Some private sales of individual tokens do appear to be genuine, although I, certainly, would have little or no confidence buying a token through third parties on this page as these are simply private sales with no reputation and/or escrow or system similar in place.
DNSCrypt
The Windows Widget v3 features DNSCrypt support: “Now your DNS queries will be hidden from your ISP before you even connect to CS, so unless they're keeping track of all of our DNSCrypt/DeepDNS IPs (which is why you can choose a non-CS DNSCrypt server in v3), they won't even know you're connecting to CS.” The main advantage that I can see here is the ability to connect securely to non-CryptoStorm DNS servers. This should help to overcome the blocks on VPN providers that counties such as China implement.
DNSChain
DNSChain is a technology that aims to fix existing problems with the HTTPS certificate authentication system. It instead uses the Namecoin blockchain to authenticate certificates. I have an article about it here. It is a good idea, but to the best of my knowledge it remains very much at the developmental stage. This means that it is most certainly not ready for show time.
CryptoStorm Privacy
CryptoStorm bills itself as a privacy champion, but no information whatsoever about the company is available on its website. A CryptoStorm staff member defended the company’s pseudo-anonymity in this old reddit post, but, personally, I prefer trusting companies run by individuals who are willing to take personal responsibility for the services they run. I do, however, understand that some may appreciate the cloak and dagger approach.
Jurisdiction
This does mean, however, that it is impossible to say for sure under which jurisdiction CryptoStorm operates For what it’s worth, Douglas Spink is a US citizen, and Baneki Privacy Computing Inc. is registered in Canada (see addendum).
We generally recommend avoiding Canadian VPNs on privacy grounds, as Canada is an enthusiastic member of the NSA-led Five Eyes spying alliance. This review (which also talks to a CryptoStorm spokesperson) states that CryptoStorm is based in Iceland.
I can, however, find no other confirmation of this. Iceland is good for privacy, but if CryptoStorm is indeed based in there, then it is interesting to note that it runs no servers from that location. Update: CryptoStorm has told me that: "Which country are you based in from a legal perspective? Iceland, actually we don't care." Hmm. I must say that I am not very convinced. It is also worth noting briefly here that the Spink connection has led to speculation that CryptoStorm is a honeypot.
Cryptostorm: Logs
CryptoStorm claims to keep no logs at all, although it does clearly monitor server activity in realtime: “You can set the main and status logs to /dev/null to truly disable logging, but that will mean the provider won't have access to useful stats such as how many users are currently connected to an instance (and thus, to each physical server).
Most of them (including us) need that information to keep track of how busy a particular server is, so that we know when a particular cluster needs an additional node.!” Somewhat more worryingly:
“Since we don't like the idea of real IPs showing up anywhere in the status logs, we modified the OpenVPN source so that the number of connected users can still be viewed (along with bytes received/sent, connected since, etc.) , but the IP address is no longer part of that data. We created a UNIX .diff patch for anyone else that wants to do the same with OpenVPN, available here (apply with `patch -p1 < noip.diff`).”
Is it really a good idea to modify the tried, tested, and now fully audited OpenVPN code with an untested and unaudited patch? I would much prefer all logs were simply sent to /dev/null, as providers such as AirVPN does.
Is CryptoStorm secure?
VryptoStorn uses the following OpenVPN settings:
Control channel: an AES-256 cipher. RSA and SHA parameters are undefined (tls-cipher TLS-DHE-RSA-WITH-AES-256-CBC-SHA), so I will assume the default OpenVPN RSA-2048 handshake encryption and HMAC SHA-1 hash authentication. Perfect forward secrecy (PFS) is provided courtesy of a Diffie-Hellman exchange (DHE).
Data channel: an AES-256-CBC cipher with HMAC SHA-512 hash authentication. These settings are fine, although are only as secure as the default OpenVPN settings used for the control channel (which are, it should be said, secure).
As is standard practice, all IPs are shared for increased privacy. Want to know more? Please check out my VPN encryption guide and 5 most secure VPNs for 2017. CryptoStorm says that it uses bare metal servers patched with grsecurity for additional security. Other than the fact that there exist some legal issues regarding the grsecurity GPLv2 license, this sounds good.
Cryptostorm Website
Tastes vary, but for me personally, the CryptoStorm website is one of the ugliest and most unprofessional looking websites I have seen since the 1990s. 
Of greater concern is the heavy use of impressive-sounding buzzwords that appear to have little in the way of substance. This terse yet somehow at the same time wordy and jargon-heavy language also dominates the forum pages, which are the heart of the CryptoStorm website. Worryingly, many of the links on the home page lead to HTTPS certificate.
Such basic errors do little to inspire confidence in the technical capabilities of the service. Now... I am a tech-head, but I have trouble following much of what is said on the website and forums. If anything, I find the language confusing and that it obfuscates what is being said.
This situation is not helped by the fact that the forum search tool consistently failed to return the results I asked for. That said, CryptoStorm does appear to have a loyal fan base which actively participates in forum discussions. CryprtoStorm’s posting style must, therefore, appeal to some.
CryptoStorm Support
Other than via the forum pages, support comes via a (browser-based) IRC chat channel. You can also post questions to the CryptoStorm Twitter channel.
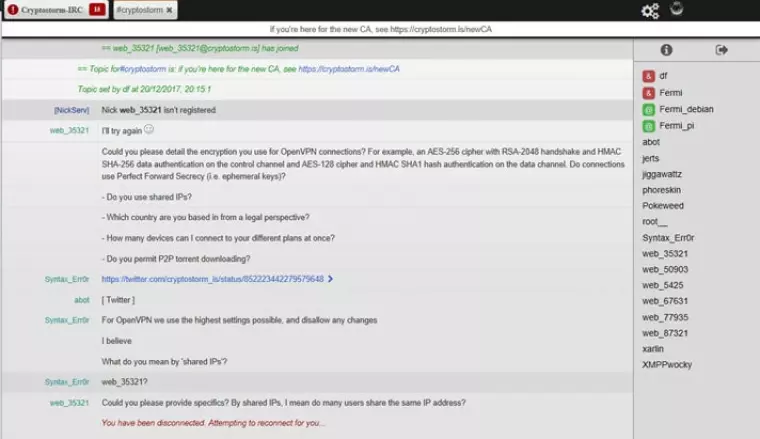
Despite the IRC channel being quite busy, I was unable to able to get satisfactory answers to my questions. Above is the only response I did get, after which I found myself repeatedly disconnected. Update: I did receive a Twitter response 5 days later, which answered my questions satisfactorily.
The Process
Once CryptoStorm has received payment, it will email you a token code (in theory you can also buy tokens from third-party resellers). The email address therefore needs to be valid, but a disposable email account will suffice.
CryptoStorm Windows “Widget” v3
The Widget can be downloaded from the website homepage. It is good to note that the Widget is open source, but although md5 and SHA hashes are available, a full PGP signature is not. This is not good form for open source software, as there is no guarantee it has not been tampered with.
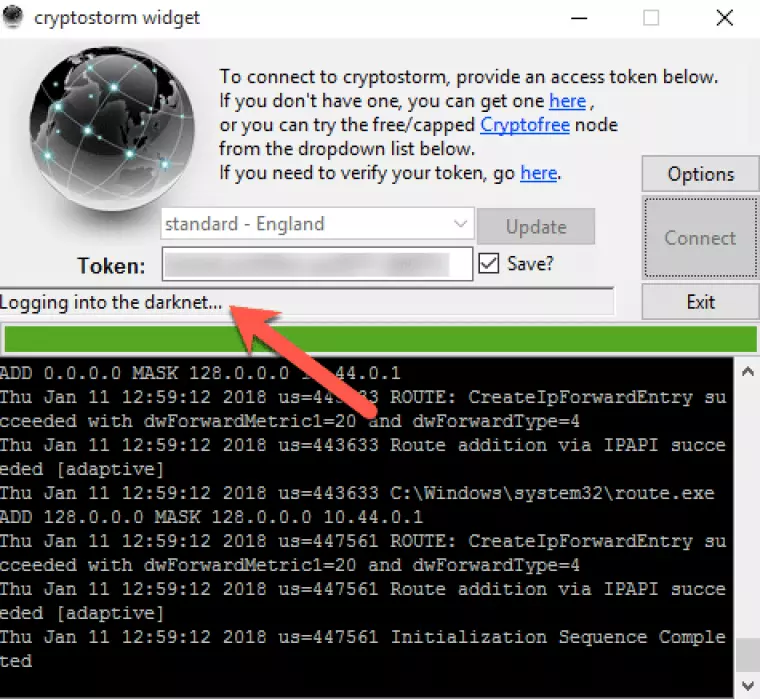
Um… how is logging on to a VPN server in any way, shape, or form “Logging into the darknet…"?!! This is symptomatic of the kind misleading jargon found at all levels of this service.
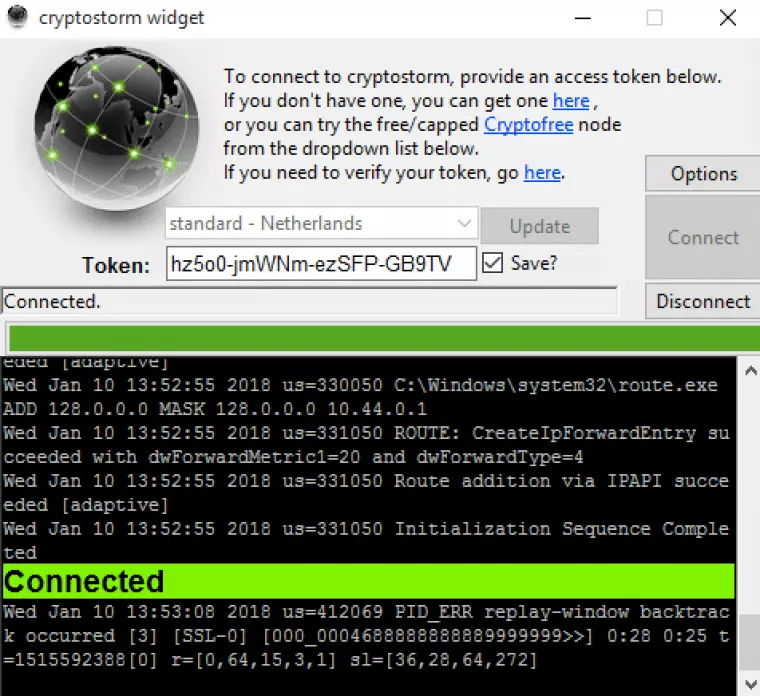
I have seen prettier software, but it gets the job done.
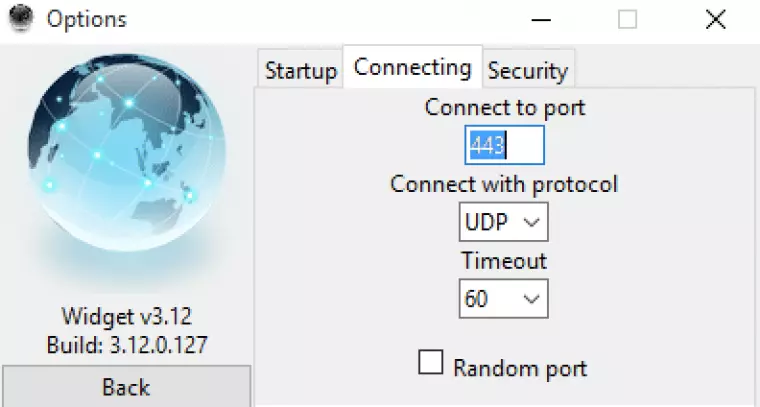
You can choose any port number (UDP or TCP) or randomise the port. The latter option may help overcome VPN censorship measures and obfuscate VPN use.

The Widget features DNS and WebRTC leak protection (IPv6 DNS is simply disabled). As we shall see below, however, IPv6 addresses are still leaked via WebRTC. I discuss DNSCrypt functionality above. There is no kill switch.
CryptoStorm Performance (Speed, DNS, WebRTC, and IPv6 Tests)
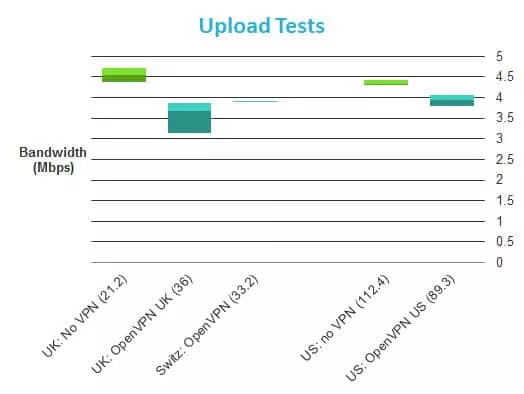
All tests were performed on my Virgin Media UK fiber connection, using the OpenVPN User Datagram Protocol (UDP). They were performed in a clean-install Virtual Machine using a wired Ethernet connection.
The graphs show the highest, lowest, and average speeds for each server and location. See our full speed test explanation for more details, but note that I have switched to Speedtest.net Beta (HTML5) as it currently produces more consistent results than testmy.net.
I have also added average ping results (latency) in brackets as this best reflects real-world page load times, and thus perceived speed. 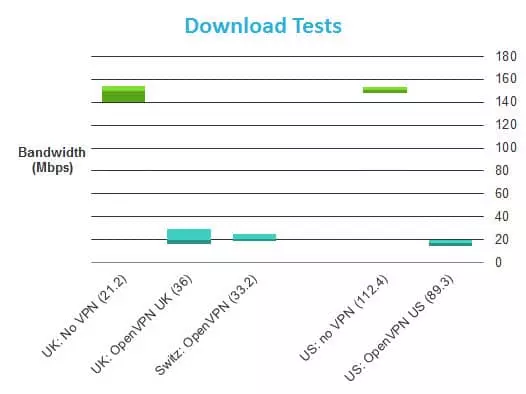
Needless to say, the download speed results are very unimpressive. “astonishing network speed so far ahead, it's scary” this is not.
Just out of interest, I also tested the “CryptoFree” server with the following results (averaged): Download 0.38 Mbps, Upload 0.89 Mbps, Ping: 654.2. These speeds are, to all practical intents, unusable. 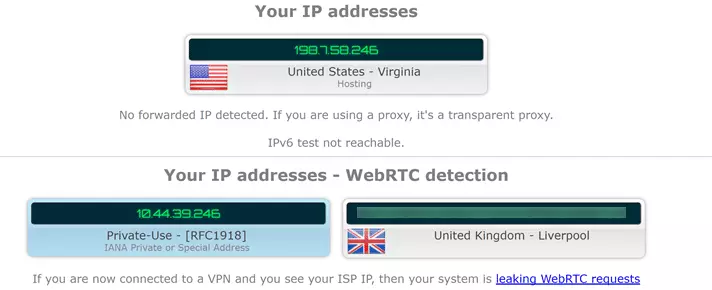
Simple IP leak tests using ipleak.net revealed a WebRTC IPv6 leak. This means that websites can see IPv6 users’ real IP address, which is a complete fail for a VPN. For more details on WebRTC leaks please see here. CryptoStorm did not work with either US Netfix or BBC iPlayer.
Other Platforms
The “Widget” is only available for Windows, but manual setup guides are available for Linux (various distros), Android, iOS and OSX (although the OSX link in the introductory email points to Linux instructions). When using third-party software you can make up the password, and the username is the SHA512 hash of the token code. I am not 100% percent sure what advantage this gives over just using the code itself, but there may be one. An SHA512 calculator is included on the website to make this step easy, although some may not appreciate the fact that this requires JavaScript to work.
Addendum: Douglas Spink
No discussion about CryptoStorm can be complete without mention of Douglas Spink. CryptoStorm is a reincarnation of VPN service CryptoCloud, a subsidiary (or possibly close working partner) of Baneki Privacy Computing Inc. Bloomberg continues to list Spink as Chief Technology Officer of Baneki, and it has been widely reported that he owns CryproStorm (something he himself has gone on record as saying). CryptoStorm, for its part, has over the years continued to deny that Spink has any current affiliation with the company. This makes the following statement issued just a year ago rather strange: “He did come back and get re-involved for a short time after his release, but then he got arrested again, and the rest of the team disassociated him and removed/prevented any access of his to anything.” It is worth noting that Spink has a very distinctive writing style that permeates the CryptoStorm website. Whether or not he is still involved, he was clearly the guiding hand in CryptoStorm’s creation.
So Who the Hell Is Spink?
- Spink was a successful American entrepreneur and adrenaline junkie who lost his millions and filed for bankruptcy in 2002.
- He is also an outspoken advocate for zoophilia.
- In 2005 he was convicted of smuggling 375 pounds of cocaine (valued at $34 million). Although sentenced to 17 years in prison, Spink was released after just 3 years afters “because of his extensive cooperation with investigators.”
- In 2010 he was arrested for running a bestiality farm in Canada. It appears this resulted in him being sent back to prison for another 3 years
- On his release in 2013 he “almost immediately ran afoul of the court by circumventing the judge’s orders that he stay away from the Internet, where Spink operates several bestiality websites and blogs.”
- In 2014 he was involved in a Port Stanley police investigation into a missing dog, and was found to “boarding horses at a nearby property under an assumed name.” Spink was arrested but later released.
- In August 2015 Spink was arrested in London and “held on an arrest warrant for skipping out of a 90-day sentence for animal cruelty in Washington State.” He was released by “mistake.”
- In November 2017 Spink returned to Port Stanley and was arrested after a standoff with the police following an altercation with the former neighbor who’s dog he was accused of stealing. As a result of this altercation, his former neighbor’s house burned down.
- In 2016 he was deported from Canada to face outstanding animal cruelty charges in the US.
Cryptostorm Review: Conclusion
Ignoring the Spink connection, CryptoStorm is a very run-of-the-mill VPN service with one good central idea – tokens. In theory, these allow a great deal of separation between your payment for the service and your real identity. But as CryptoStorm is simply not popular enough for there to be a thriving market of people buying and reselling these tokens “anonymously,” most of the benefits are purely theoretical. There is also a strong argument that paying by store card or even cash (Mullvad and ProtonVPN) is even more anonymous. It is also worth remembering that no matter how anonymous your payment method, your VPN provider will always know your real IP address anyway. CryptoStorm is to be commended for keeping no logs, but other than that, the service is slow and offers very slow support. Encryption is okay, but as with most other things advertised by CryptoStorm, is nowhere near as good as the hype suggests. Speaking of hype, however, CryptoStorm does appear to have an enthusiastic user base that clearly revels in the rambling jargon-heavy writing style that characterizes its website and forum pages (Spink?).
1 User Reviews
Leave a Review
Thanks for your review!
15 Comments
replied to bill gates
replied to radis jaune
replied to radis jaune
replied to Rip Trippers
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

niihm