Today’s young people are the most tech-savvy generation of all time. Games for children that teach them primitive coding skills, allow them to grow up immersed in a level of technical knowledge incomparable to any generation that came before. The IT sector promises lucrative employment opportunities, causing parents to encourage their kids to gain cyber skills as early as possible. Of course, that cultural shift is also bringing some negative consequences with it.
Teenage hackers are on the rise, even earning their own moniker as "script kiddies”. These juvenile hackers often have only core programming abilities. However, they are comfortable and familiar enough with the tech that surrounds them to get stuck in and try things. Script kiddies are experimentalists at heart. They are today’s rebel without a cause, riding an exciting wave caused by TV shows like Mr. Robot, and real-life hacking groups like Anonymous. Hacking, in many ways, is today’s Rock and Roll.
This isn’t some far-fetched fantasy, either. The idea is backed up by research carried out at University College London. That study revealed that today’s young people are more likely to spend time hacking than to be indulging in more traditional naughties such as smoking, doing drugs, and having sex.
This somewhat geeky revolution is happening all around us, and it is causing some security experts to become rather concerned.
Hacking Tools
Script Kiddies use copy and pasted segments of code to carry out hacking that most parents could only dream about. Websites like Github, and devices like the Raspberry Pi, make hacking both affordable and accessible to even the poorest digital adventurers. Hacking tutorials on websites like Youtube are a breeding ground for skills, and the opportunities to hack are only growing.
"Hacking tools” are the name given to specialist software that makes the job of launching a cyber attack much easier. High profile hacking tools such as Eternal Blue are the quintessence of these kinds of software. That particular tool was stolen from the NSA - before being sold on the dark web - and being exploited to carry out last year’s infamous WannaCry attack.
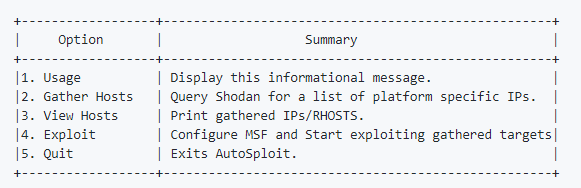
Now, a new hacking tool that automatically searches the internet for possible victims - and then helps to launch a cyber attack on them - is being criticized by security experts. The software in question is called AutoSploit. It is an open source program developed by an anonymous security researcher called Vector, and it is freely available to download on the website GitHub.

AutoSploit
As the name implies, AutoSploit brings a whole new level of simplicity to finding and exploiting a target. Usually, hackers have to make the effort to find a specific target, check whether that target is vulnerable to specific exploits; and then deliver a successful attack.
AutoSploit, on the other hand, automates the process by bringing together a number of different hacking tools into one. Most problematically, it harnesses the power of a searching tool called Shodan, and a potent hacking tool called Metasploit (often used by "white hat” hackers for penetration testing).
AutoSploit explains how the tool works as follows:
"Basically you start the tool, and enter a search query, something like ‘apache’. After that the tool uses the Shodan API to find boxes [computers] that are described as being ‘apache’ on Shodan.
"After that a list of Metasploit modules is loaded and sorted based on your search query; once the appropriate modules are selected it will start running them in sequence on the list of targets you acquired.”
Too Easy
The ease of use and availability of this hacking tool is leading security researchers to question the sense of making such a tool publicly available. Richard Bejtlich, a cybersecurity expert who has previously worked at FireEye and Mandiant has gone on the record to criticize the software:
"There is no legitimate reason to put mass exploitation of public systems within the reach of script kiddies. Just because you can do something doesn't make it wise to do so. This will end in tears.”
Bejtlich feels that combining easy hack capabilities with the Shodan search facility puts AutoSploit "over the edge.” In his opinion, it is only a matter of time before hackers, including script kiddies, are using this tool to reek havoc.
Security expert, Kevin Beaumont, agrees with this prognosis. He tweeted that the exploit will likely lead to a wave of ransomware attacks. Whichever way you look at it, the problem of script kiddies is here to stay, and tools like these are only going to exacerbate the problem.
Opinions are the writer's own.
Title image credit: Ollyy/Shutterstock.com
Image credits: Github logo
