Overwhelmed by the sheer number of VPNs available for your iPhone in the app store? You're not alone! We'll take a look at the best VPNs to keep your iPhone and iOS secure.
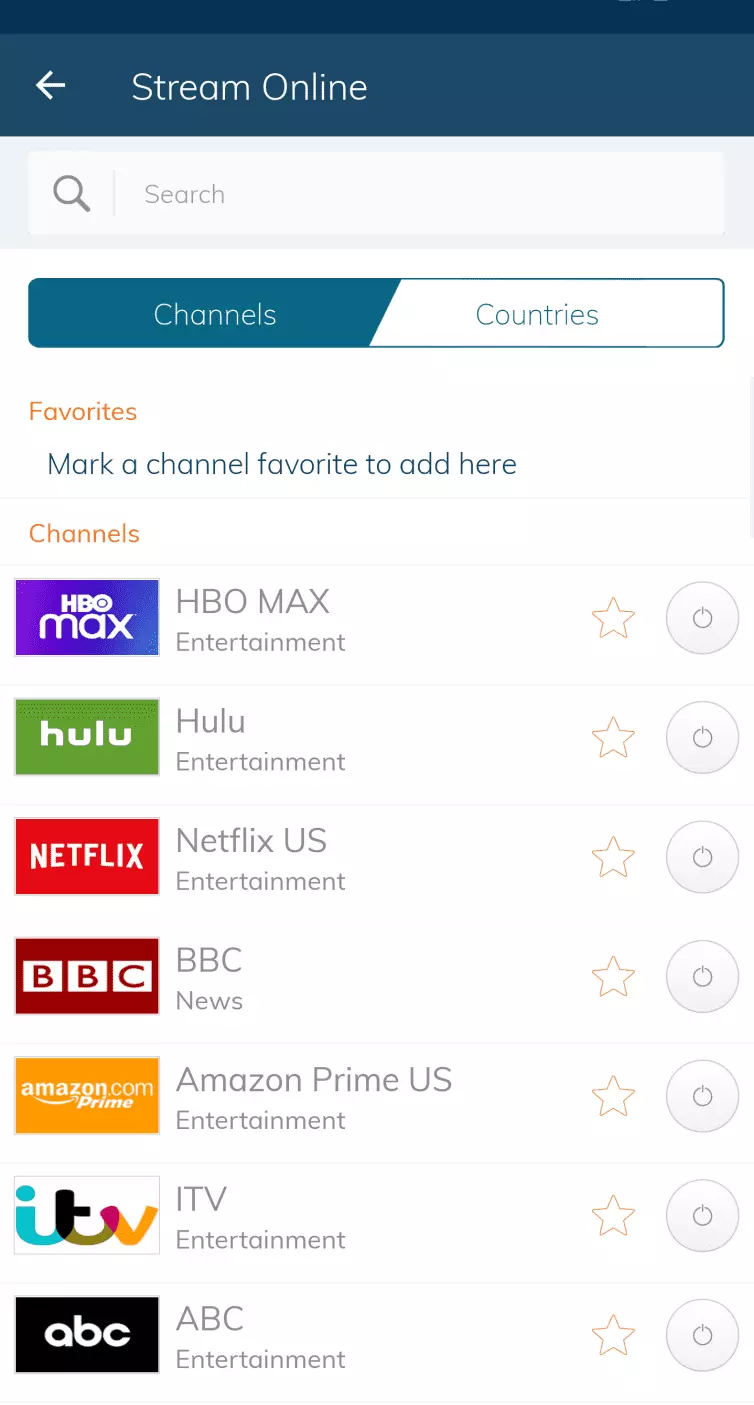
There are plenty of reasons to invest in a VPN for your iOS device – improved security, privacy, and streaming ability being just a few. The best VPNs have intuitive apps tailored to the iPhone and iPad, which make it easy to do things like access streaming services in other countries or bypass network blocks. Although Apple is often praised for preventing government snooping on iOS devices, a Virtual Private Network (VPN) remains the only way for iPad and iPhone users to gain real online privacy.
Here are our top reasons why you need an iOS VPN:
- Security – iPhones and iPads may not be prone to viruses, but your identifiable information (like your IP address and internet traffic) can still be read by third-party snoopers. A VPN puts a stop to this by assigning you a new IP address and encrypting data flowing between your device and the VPN server.
- Content – Streaming sites (like Netflix) often hide content behind geo-restrictions, which can put a premature end to your movie night plans. With a VPN, you'll be able to connect to a server in a location where the content you want to watch is readily available, and stream it with ease.
- Public wi-fi protection – Public wi-fi hotspots are notoriously unsecure, with hackers just waiting to steal your data or trick you into joining a bogus connection. Sometimes we have to rely on these hotspots, though, and a VPN makes it a much safer experience thanks to superb encryption which secures all of your internet traffic.
- Bypass blocks – Time-wasting sites, like social media platforms, are often blocked at workplaces and schools. A VPN can tunnel through the firewalls imposed by these institutions and grant you access – though you'll want to make sure that you do some work!
- Save money – Certain online shopfronts (and especially those selling tickets) can ramp up their prices whenever you hit refresh, pushing you to buy. A VPN puts a stop to this by concealing your IP address, so that the shopfront can't gather your details and target you.
At ProPrivacy, we've put dozens of iOS apps through their paces to figure out which services work best with iPhones and iPads. We take an objective, scientific approach to our research, comparing the providers' speed, security, and unblocking power, before whittling them down to a top ten – which you can check out a little later in the article.
To learn more about our recommended services, see the list below.
What is the best VPN for iPhone?
Below, we've shortlisted 10 of the best iOS VPNs on the market. All of our hand-picked recommendations come with robust encryption, speeds that can handle data-intensive tasks, and easy-to-use apps. And, of course, they're all compatible with iOS and iPhone!
- ExpressVPN - The best VPN for iOS. Offers lightning-fast speeds, slick apps, and a 30-day money-back guarantee.
- NordVPN - The best value iOS VPN. It's reliable, works with most streaming platforms, and its apps are easy to use!
- Surfshark - The best multi-device iOS VPN. Offers unlimited simultaneous connections, tons of features, and WireGuard encryption!
- Private Internet Access - The best secure iOS VPN. Super secure, zero-logs, and with a full suite of customizable tools.
- PrivateVPN - The best user-friendly iOS VPN. Works with lots of streaming sites and is consistently fast, offering servers worldwide.
EXPERIENCE EXPRESSVPN WITH A 30-DAY FREE TRIAL
Sign up on this page to enjoy a full-featured 30-day trial from ExpressVPN. Dive into the world of the #1 rated VPN for privacy, and especially if you're keen on trying the best VPN App for iOS
Transparent terms—contact the support team within 30 days for a hassle-free refund if you're not satisfied. Click here to start your ExpressVPN trial
Before any VPN makes it onto our list, however, we ensure that it offers the following key features:
- Battle-tested encryption
- A zero-logs policy
- Speedy servers across the globe
- Easy-to-use apps for iOS
- A money-back guarantee
| TEST WINNER ExpressVPN | NordVPN | Surfshark | Private Internet Access | PrivateVPN | |
|---|---|---|---|---|---|
| Website | ExpressVPN | NordVPN | Surfshark | Private Internet Access | PrivateVPN |
| Ranking for iPhone and iPad | 1 | 2 | 3 | 4 | 5 |
| Performance | 10 | 9 | 9 | 8 | 7 |
| Reliability | 9 | 8 | 8 | 8 | 7 |
| Free trial | |||||
| Total servers | 3000 | 6200 | 3200 | 3386 | 200 |
| Payment | PayPal Visa/MasterCard Amex Cryptocurrency | PayPal Visa/MasterCard Amex Cryptocurrency | PayPal Visa/MasterCard Amex Cryptocurrency | PayPal Visa/MasterCard Amex Cryptocurrency | PayPal Visa/MasterCard Amex Cryptocurrency |
| Unblocks: | Netflix iPlayer Disney+ Amazon Prime Hulu | Netflix iPlayer Disney+ Amazon Prime Hulu | Netflix iPlayer Disney+ Amazon Prime Hulu | Netflix iPlayer Disney+ Amazon Prime Hulu | Netflix iPlayer Disney+ Amazon Prime Hulu |
| Supported platforms | Windows macOS iOS Android | Windows macOS iOS Android | Windows macOS iOS Android | Windows macOS iOS Android | Windows macOS iOS Android |
The best VPNs for iPhone and iPad – In-depth analysis
We recommend these VPN services for iPhone and iPad users in 2024.
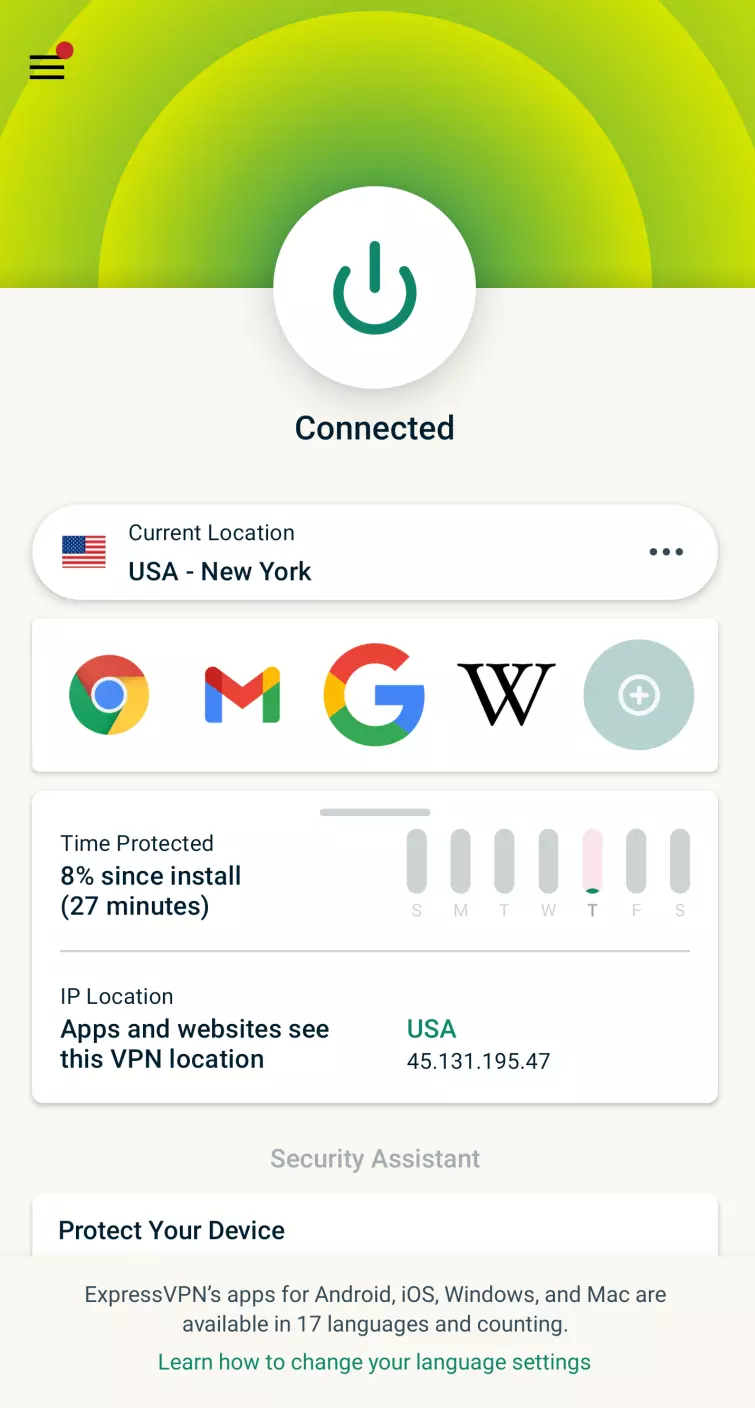
ExpressVPN is the best VPN for iOS. It's consistently fast, has great features, and reliably works with most services. With a 30-day money-back guarantee. ExpressVPN Demo There aren't many VPNs that are household names outside diehard privacy advocates, but ExpressVPN is almost certainly one of them – and it's easy to see why! The provider has spent the last decade leading the market by example, offering a feature-rich service that doesn't skimp on security. ExpressVPN consistently makes it into our hand-picked shortlists because it excels at pretty much anything you'd need it to do. What's more, ExpressVPN has a longstanding reputation for lightning-fast speeds, reliability, and intuitive security features. The iOS mobile app is easy to use, even for beginners, and provides all the necessary tools to keep your data secure from hackers, your ISP, and the government. ExpressVPN is compatible with iOS 14, 13, and 12, and can be used on iPhone 12, 11, SE, and XS, amongst others. The ExpressVPN iOS app not only looks incredible, but it ensures that your iPhone is protected whenever you connect to private or public Wi-Fi, or switch to mobile data. VPNs are often celebrated as a means of unblocking geo-restricted content, and it's an important part of their toolkit, but if the VPN can't protect your privacy or provide adequate encryption, it's not worth the risk. Fortunately, ExpressVPN excels when it comes to security. The service opts for super secure AES 256-bit encryption, which ensures that your traffic can't be snooped on by any third parties – internet service providers (ISPs) and potential bad actors included. Additionally, ExpressVPN abides by a strict no-logs policy that's been verified by independent auditors. This means that the VPN doesn't keep hold of any activity or connection logs. With servers in 105 countries
worldwide, you can rest assured that no content is out of your reach – ExpressVPN can successfully unblock services and sites from all over the world. ExpressVPN is one of the most reliable services out there when it comes to accessing geo-restricted content on Netflix or BBC iPlayer (as well as a ton of other services), and streaming aficionados should definitely give it a try. I also can't overstate how quick ExpressVPN is. When I'm using the service, I often forget that I'm connected to a VPN at all – and it's no different when you're streaming. Expect high-quality pictures, an end to annoying buffering, and no more stuttering. And, if you're really looking for a quick (but secure) connection, try ExpressVPN's proprietary VPN protocol, Lightway, which has been designed to be quick and lightweight. You might think that this all sounds too good to be true. It's not, but you should expect to pay a little more for your ExpressVPN subscription than you would for another provider. It's not the cheapest service out there, but you certainly feel like you're paying for a quality product that's packed with utility. ExpressVPN is compatible with most devices and operating systems, offers up to 8
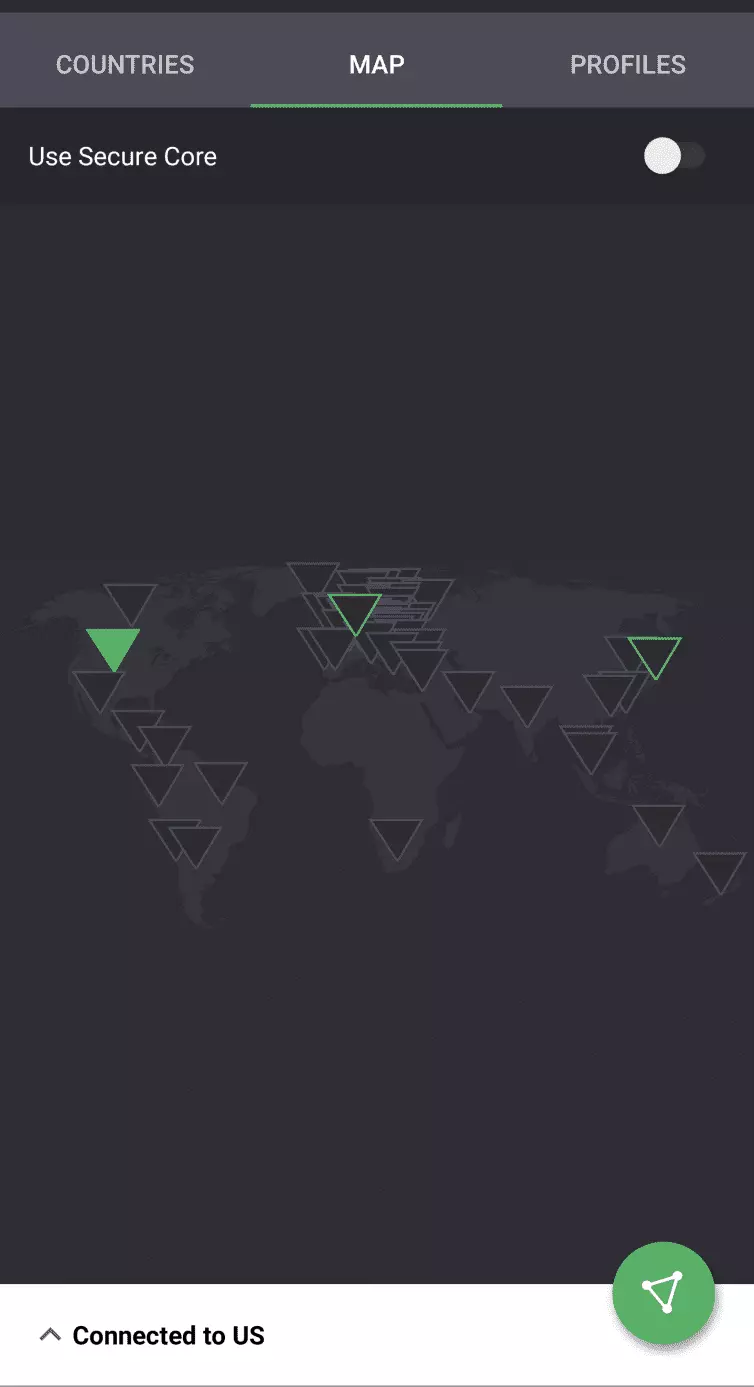
simultaneous connections, and is incredibly easy to use, even if you've got no prior VPN experience. I'd definitely recommend trying the service for yourself with its 30-day money-back guarantee! NordVPN is the best value iOS VPN. Users can effortlessly protect their digital privacy with a sleek iOS app, and enjoy a 30-day money-back guarantee. Nord Demo If you're looking for a VPN that's inexpensive but fully-featured (and let's be honest – who isn't?), then NordVPN could be your match made in heaven. NordVPN is compatible with various iPhone models, all the way from the 5S to the 12 Mini, and is supported by devices running iOS 11.0 or later. If you've ever used NordVPN's desktop clients, you'll find that the iOS interface is quite similar and just as easy to navigate. In addition to ensuring that your internet connection is private and your traffic is encrypted (via the IKEv2/IPsec protocol), the NordVPN iOS app also boasts a quick connect feature and specialty servers for P2P and Onion Over VPN. All in all, we're impressed! It might actually be easier to list the streaming services that NordVPN can't access. You'll have no trouble browsing Netflix, Amazon Prime, BBC iPlayer, Hulu, HBO, and more, and all without those pesky geo-restrictions that spoil the fun. NordVPN is a reliable service that offers consistent access to content from around the world, and a built-in Smart DNS feature certainly sweetens the pot, too. I often recommend NordVPN to people who are unfamiliar with VPNs… but want to give them a go! NordVPN is exceptionally easy to use on an iPhone, which is mostly thanks to the large world map that displays the myriad server locations via pins. It's similar to the Google Maps interface, so you can just click a pin in the country you want to connect to and voilà! It's that simple, and it's a great, hyper-visual system that we're surprised hasn't been replicated more frequently by other providers. Nord also lets you install the software on up to 10
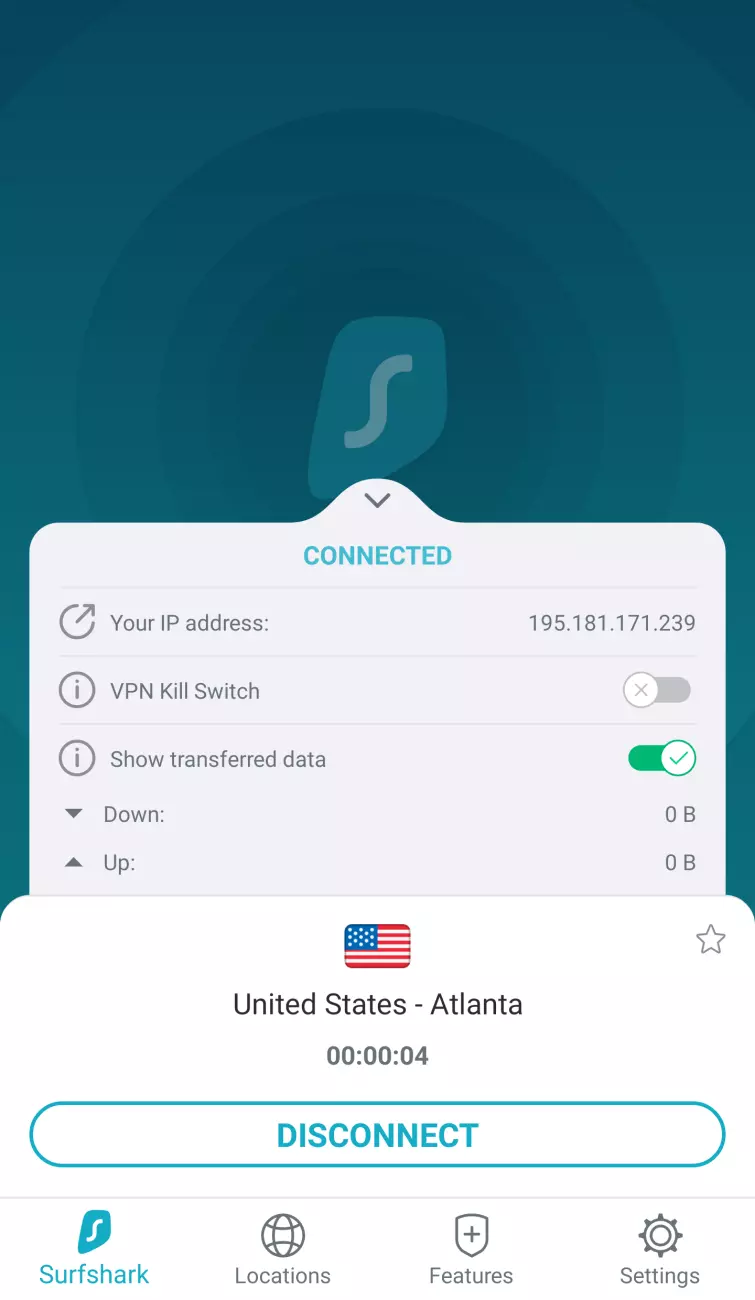
devices simultaneously, which makes it perfect for families (or folks with a lot of devices to protect) and exceptional value for money. Finally, you can take NordVPN for a test drive yourself with its 30-day money-back guarantee. NordVPN is lightning-fast, which makes it a perfect fit for anyone looking to do some HD streaming, gaming, or VoIP calls. The service frequently ranks near the top of our in-house speed tests, too. I'm also consistently impressed by how robust and sturdy NordVPN's security measures are. The VPN's iOS app uses IKEv2 in combination with AES 256-bit encryption, which is a winning combination in my book, but also offers a built-in kill-switch. Not all iOS VPN apps do this, so it's worth making a note of! NordVPN also makes its home in Panama. This is great news for privacy fanatics, seeing as the country has no mandated data-retention laws and is far beyond the reach of the NSA. What's more, NordVPN's no-logs claim is frequently reviewed by an independent third-party auditor. Surfshark is the best multi-device VPN for iOS. Coming in at a competitive price, this VPN is secure, fast, and works with major streaming services. Offers a 30-day money-back guarantee. Surfshark Demo Surfshark provides an inexpensive and reliable service, making it the ideal option for anyone on a budget who wants true value for money. What's more, the Surfshark iOS mobile app can be downloaded from the App Store in a few clicks. And we’re not kidding when we say it’s seriously impressive. It features a kill-switch, support for devices running iOS 10.3 and up, and even allows users to pick and choose which protocol they’d like to use. The app supports IKEv2, as well as OpenVPN and WireGuard, which is a huge bonus in our books. We find that whenever we use Surfshark for iPhone, we're always impressed by the overall quality of the app and all its features. Surfshark users can choose from thousands of servers in 100 countries
worldwide, and they're all remarkably fast! You'll be able to stream, game, and join VoIP calls with a minimum of fuss. Plus, torrenting is permitted on all Surfshark servers. These servers have been configured with torrenting specifically in mind, and automatically route P2P traffic through to servers in Canada or the Netherlands. If you’re more of a streamer, Surfshark still has you covered, and can easily access a wealth of services. Take your pick from Netflix, Amazon Prime, Disney+, HBO, Hulu, and plenty more. Oh, and there’s no need to worry about buffering hiccups or delays, either, as Surfshark is consistently one of the quickest VPNs on the market. Surfshark makes its home in the British Virgin Islands, which is an encouraging factor if you’re prioritizing privacy. The British Virgin Islands don’t have mandatory data retention laws – another win for VPN users – but it’s important to remember that it does still remain under the jurisdiction of the UK. Fortunately, Surfshark takes its security very seriously. The provider more than qualifies as a no-logs VPN, and has had the claim verified by an independent auditor, and also uses diskless RAM-only server network. I’m impressed by this, as it means that Surfshark has better control over its network (less third-party involvement), and the locally-stored information can’t be physically swiped once a session ends. Another feature I’m happy to see offered by the VPN is two-factor authentication (2FA). You won’t get this with every VPN, but it’s a simple, effective way to ramp up user security. Likewise, it’s a nice surprise to see Surfshark’s iOS app come with its own kill-switch! So, if your VPN connection happens to drop, your device’s real IP address won’t leak. And now onto Surfshark’s biggest selling point – the unlimited simultaneous connections! This is incredibly generous, and it makes Surfshark the perfect pick for families, friend groups, and tech hoarders who want protection for all their devices. So, I’d wholeheartedly recommend taking Surfshark for a whirl, and you can do so without risking your money thanks to a 30-day money-back guarantee! Private Internet Access is the best secure iOS VPN. With a proven zero-logs policy and excellent encryption to protect all your Apple devices. Plus, a 30-day money-back guarantee. PIA Demo Private Internet Access (also known as PIA) is a seriously impressive service in terms of both security and usability. Anyone using iOS 11, or a newer version, will be able to download the PIA iOS app and boost their privacy, whether you're using your phone at home, on the go, or even on vacation. I should point out that being based in the United States isn't all that encouraging from a privacy standpoint, seeing as the NSA and CIA could easily come knocking with a gag order at any point, but PIA reassures users with a no-logs claim that has been proven in court and independently audited. There are simply no user logs to pass over to the US government even if they stomp their feet. PIA's server network has seen something of an exponential growth in recent months. There are whopping tens of thousands of servers to pick from across 84 countries
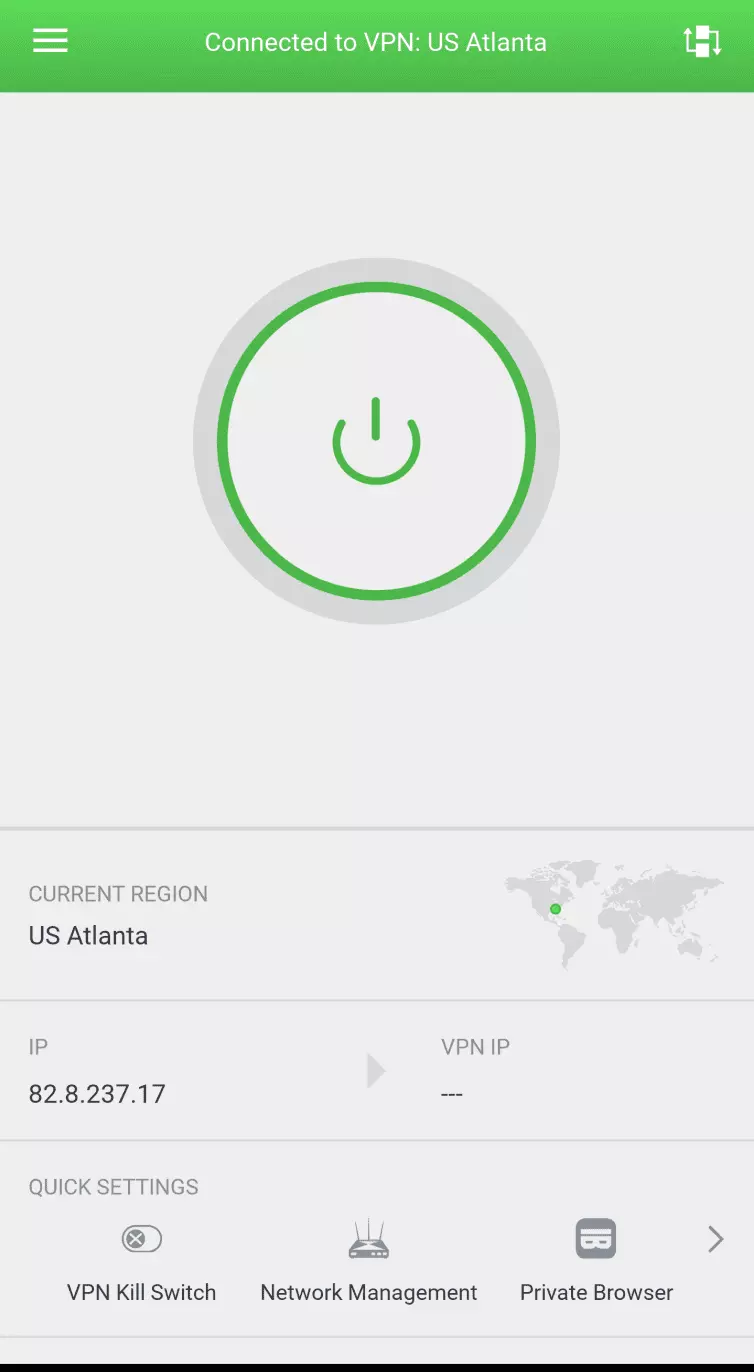
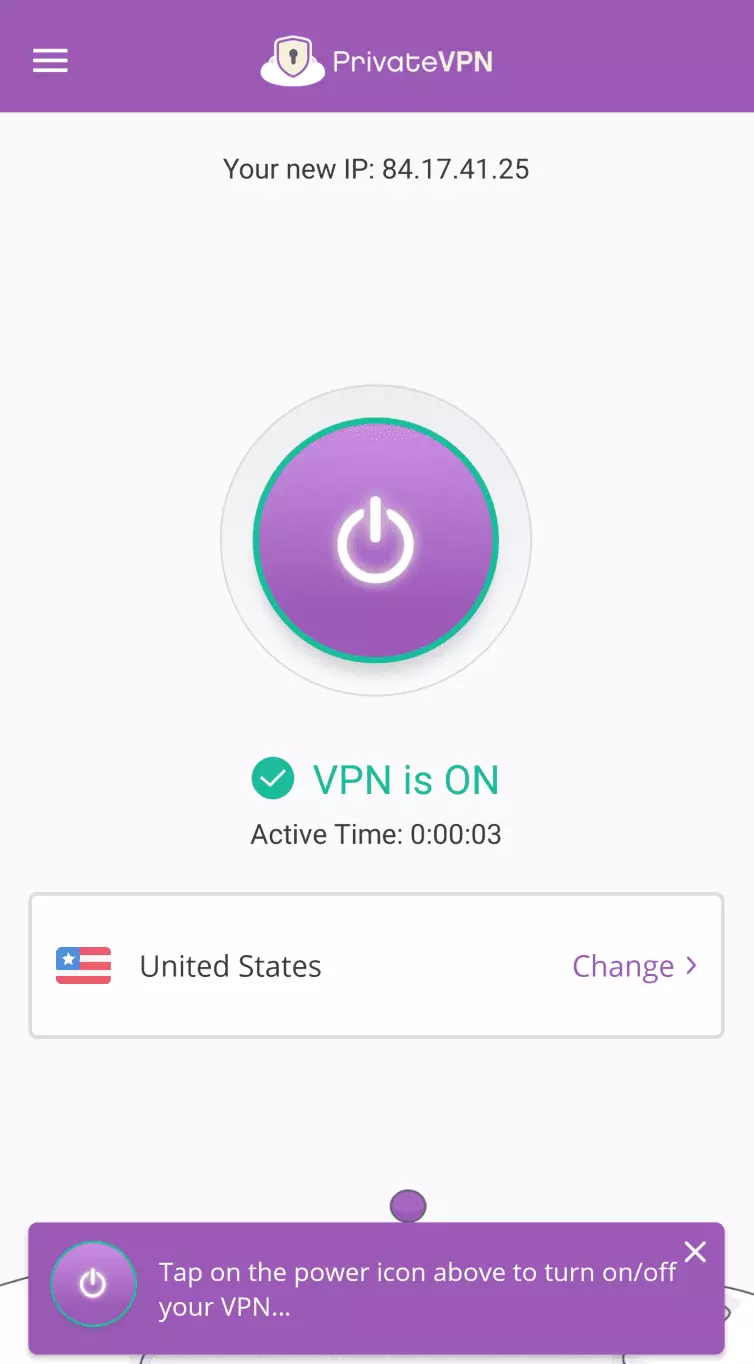
worldwide, so you're really getting your money's worth! This broad range of servers also makes PIA an ideal choice for anyone looking to stream geo-restricted content or bypass local censorship, and we're happy to confirm that the service is more than capable of unblocking Netflix and BBC iPlayer, amongst others. If you happen to have any trouble whilst accessing these sites, or at any point during your time with PIA, you can check in with the customer service team via live chat to get some answers. What's more, you can trial PIA on your own device and put it to the test yourself by taking advantage of the 30-day money-back guarantee. During my tests, I used PIA on my iPad and laptop computer and found both apps super easy to use. You can register for PIA, download the app, and get started in literal minutes, and there's no complicated installation process. So, whilst you can dig into the details of all those VPN settings if you want (more on this later), you also don't have to, which I think makes PIA a great choice for anyone new to the tech. It's also worth noting just how cheap a PIA subscription is when purchased yearly. You're getting some serious savings if you opt for the annual plan, and a premium-feeling product for a budget price. With PIA, you get loads of ways to configure the app so you can set the VPN up exactly as you wish. I had a quick dig under the hood and found that the PIA iOS app comes set to IKEv2 by default; a secure protocol with encryption I'm happy to trust (and I'd suggest picking IKEv2 over the other available protocol, L2TP/IPsec). It also impressed me to see that iOS users can switch to OpenVPN in the settings if they want to, with no need to install a third-party OpenVPN client. The speedy WireGuard protocol is also available. PIA has apps for all platforms, and it permits you to use the VPN on all your devices simultaneously, no limits. That means you can use it on your iPhone, iPad, MacBook, or Android, or Windows PCs – so it's perfect for families, or folks who want to protect all the devices in the house! PrivateVPN is the best user-friendly iOS VPN. The unblocking and streaming capabilities of this inexpensive VPN are unrivalled, and it includes a 30-day money-back guarantee. PrivateVPN Demo Calling a VPN service "PrivateVPN" is pretty bold, but we've always found that it lives up to the claim! The provider is well-liked by consumers and keen to make a name for itself, too. With PrivateVPN, you'll be getting impressive speeds and access to all the most in-demand streaming services, and all without waiting for that buffering circle to disappear. Personally, I thought the iOS app was brilliant, so PrivateVPN more than earns its spot in our top ten. PrivateVPN provides a no-logs policy that's robust and reassuring – less so is the fact that the service is based in Sweden. The country does have data retention laws, but PrivateVPN actually reached out to us to explain that its decision to remain in the country is due partly to the fact that it has full access to its central data center, and that they own and control all the hardware – even the router! Obviously, that should allay the majority of fears. Keep in mind that because PrivateVPN is a no-logs provider, and doesn't keep hold of those details, there would be nothing to hand over to any authorities who came knocking, anyway. I was glad to see that PrivateVPN packs OpenVPN encryption right out of the box, so you're covered regardless of whether you're using your iPhone or iPad at home, at work, or in public. The encryption also comes in handy if you're going to be torrenting, because PrivateVPN allows P2P traffic (and torrenting is a dream with PrivateVPN thanks to its outstanding server speeds!). When I tested PrivateVPN, I found it incredibly easy to use – tech veterans and VPN newbies alike will have no trouble navigating the iOS app. It was also great for unblocking streams from around the world – including content from Netflix and BBC iPlayer. As such, I'd definitely recommend PrivateVPN for anyone who's constantly on the move, either on vacation or for work. PrivateVPN has hundreds of fast servers across 63 countries
– that's a modest amount, though you might think it's considerably fewer than other VPNs on this list. You'd be right, but remember that PrivateVPN is still a young company with fewer customers (albeit with an impressive set of features and really quick speeds!). You will, however, be able to pick servers optimized for streaming if you're settling in to a Netflix marathon. You might not need to reach out to PrivateVPN's customer service team, but if you do, you can rest assured that they'll do whatever they can to troubleshoot your issue. During testing, I found that the VPN's team wasn't available via live chat 24/7, so you'll want to contact them during European daylight hours to chat. You can send an email at any point in the day, though, and responses are generally quick and informative! PrivateVPN packs a big punch for a relatively small provider, and offers up to 10 simultaneous connections. An industry-standard 30-day money-back guarantee is available so you can put the provider through its paces without risking anything financially. VyprVPN is the best mid-range VPN for iOS. A sleek iOS app packed with features, proprietary servers, and a 30-day money-back guarantee. VYPR Demo VyprVPN is one of our favorite VPNs for iPhone, and we'd definitely recommend taking the service for a trial run yourself. VyprVPN operates all of its own hardware, which takes away a lot of concerns about speeds and reliability on the network. There's also an optional VyprDNS service, which is great news for those looking to unblock Netflix, YouTube, and similar services on their iOS device. The iPhone app is compatible with iOS 8 and higher, and comes with a number of handy features that make staying secure a breeze. For example, VyprVPN will automatically encrypt your data if you happen to connect to an unknown wi-fi network – which comes in especially handy if you're often on the move. If you're new to the world of VPNs and feel a little overwhelmed by the sheer selection of services out there, and the sometimes technical nature of their interfaces, then take a chance on VyprVPN. It's incredibly simple to use, and even connecting to a server is as simple as tapping on the map! VyprVPN doesn't bore you with the unnecessary details, either. Simply connect to a quick server (denoted by ping time) and away you go. If you do want to adjust the settings though, the user interface is easy enough to navigate that you're unlikely to run into issues when doing things like changing protocol. If you do run into trouble, or have a few questions you'd like answered, the VyprVPN customer service team is around 24/7 to assist, and you can reach out via email, an online form, or by live chat. VyprVPN has plenty of servers, which is obviously ideal for spoofing your location and gaining access to geo-restricted content. I think VyprVPN is one of the best services out there for unlocking films, series, and shows – VyprVPN can consistently unblock Netflix and other big-name services, and is more than quick enough to ensure your browsing isn't interrupted by buffering hiccups or lag. If you've got other devices you'd like to protect, you'll be able to do so, as VyprVPN allows up to 10 simultaneous device connections. VyprVPN doesn't cut corners when it comes to security, and it secures its apps with strong AES 256-bit encryption, which is the industry standard. iOS users will also be able to select from the IKEv2 and WireGuard protocols, and enjoy VyprVPN as well as third-party DNS. For folks after a more stealthy connection, you'll want to check out the provider's proprietary protocol – Chameleon. Chameleon is great for beating censorship imposed by oppressive governments, as it scrambles data in a way that cannot be detected by Deep Packet Inspection (DPI). CyberGhost is the best easy-to-use iOS VPN. Expect impressive speeds and user-friendly apps, and a 45-day money-back guarantee. CyberGhost Demo CyberGhost VPN is a VPN provider based in Romania that has a superb no-logs policy, outstanding security settings, and strong OpenVPN encryption. CyberGhost lets you access any online content without being tracked – both at home and on public wi-fi. What's more, I really can't fault the CyberGhost iPhone app – it's super easy to use and compatible with iOS 13 or later, and I've never encountered any problems whilst using it. Like most people, those of us with iPhones use them all the time (probably a bit too much, actually) – so the last thing we want is to have to deal with a complex user interface. I honestly believe CyberGhost has found a great formula here. Not only is the app incredibly straightforward, it's really simple to switch between protocols, it looks great, and has a number of specialized servers, too! CyberGhost is well worth checking out (thanks to a lengthy 45-day money-back guarantee), and you'll be able to try the service for yourself on various devices with up to 7 simultaneous connections per subscription. Apps are available for Windows, Mac, Android and, of course, iOS, too. I'm consistently impressed by CyberGhost's security setup. Users will benefit from robust AES 256-bit encryption and a no-logs policy that's been independently audited. CyberGhost is based in Romania, which is a great place for a VPN to make its home. Romania isn't part of the 14-Eyes alliance and has no ties to the NSA, which is obviously a huge plus. You'll also be able to pay for your CyberGhost subscription with Bitcoin, if you'd like, and choose between the IKEv2 and WireGuard protocols for your iOS device. And, if you're really security conscious, check out the NoSpy servers, which are only accessible to CyberGhost staff and dedicated to resource-intensive tasks. You'll never run out of content to stream with CyberGhost – it's got servers across 100 countries
, and has no trouble unblocking a wealth of the world's most in-demand streaming services. This includes Netflix, Disney+, BBC iPlayer, and many more. I particularly like that CyberGhost even has dedicated servers for these services! For example, if you're an anime fan looking to catch new episodes as they air in Japan, or fancy checking out what's new on Hulu, you can connect to a specific dedicated server and enjoy smooth, HD streaming. Connecting to these servers on your iPhone is as simple as tapping, too, so there's no complicated setup involved. If torrenting is more your thing, you're in luck, as CyberGhost permits P2P activity, and even has several specialized servers dedicated to the task. CyberGhost's live chat team are on the ball. They respond quickly, can tackle techie questions, and provide support in English, German, French, and Romanian. It also doesn't matter if it's the middle of the night – live chat is available 24/7. If you'd rather troubleshoot issues yourself, or read up on what the service has to offer, then head over to CyberGhost's FAQ pages and setup guides. These are all well-written and informative, and cover everything from getting the VPN up and running to protocol usage, and more. IPVanish is the best polished iOS VPN. Offering sleek iOS apps and a zero-logs policy, plus a 30-day money-back guarantee. IPVanish Demo IPVanish easily claims a spot in our list thanks to sleek apps for iOS 11 and up. When testing IPVanish on an iPhone, we were really impressed at how fully featured it was, how fast the connection speeds were, and how truly simple it all was to use. Most of us at ProPrivacy use iOS devices, whether that's an iPhone or an iPad, and a lot of us have this service downloaded on our devices. This is simply because the iOS app has a silky smooth interface with all the features you need. You can really tell that the folks over at IPVanish put a lot of thought and effort into making the iPhone app into something that is a real pleasure to use, regardless of how familiar you are with VPN tech. Talk about spoiled for choice; IPVanish users can have their pick of servers scattered across 75+ locations, which makes location hopping a breeze. I'm also happy to confirm that the IPVanish is incredibly fast – due in no small part to the fact that the service recently upgraded its entire network from 10 GB network capacity cards to 25 GB cards. So, if you want to stream, game online, or hop into a video call, you'll have a smooth connection without hiccups or stutters. Of course, this vast selection of servers is also ideal for unlocking regional content that's usually hidden behind geo-restrictions. IPVanish can access Netflix US, as well as ABC and NBC, without an issue, but unfortunately doesn't have much success when it comes to BBC iPlayer. Fans of British TV classics will have to be disappointed. The IPVanish iOS app is pretty impressive, as it comes with an "Always On" feature that automatically detects when you're hooked up to the internet so it can connect to the VPN for you. Similarly, API Load Balancing will consider your ping and location to suggest the best server for you. I like that the IPVanish iOS app has given the weak PPTP protocol the boot. It proves the service's commitment to real user security. You'll be able to use IKEv2 encryption on your iPhone, although there is an option to switch to OpenVPN via OpenVPN Connect software. You'll just need to nab the .ovpn config files from the IPVanish member's area. For the fastest speeds, you can use WireGuard. If there's one drawback to the IPVanish service, it's that it makes its home in the United States… along with the NSA and the CIA. The United States is certainly not s a privacy safe haven, and firms there can be served gag orders that prevent them from informing the public about any requests for user data. If it's any consolation, IPVanish stays one step ahead of this possibility with a staunch no-logs policy that's been independently audited. This policy ensures that, in the event IPVanish is served a warrant, there's nothing to hand over to the authorities in the first place. What's more, the service uses AES 256-bit encryption and even packs Perfect Forward Secrecy. IPVanish is by no means insecure, but each user will have to decide for themselves whether sharing turf with the CIA is a deal-breaker. Ivacy is the best cheap iOS VPN. Works with lots of streaming platforms and super-secure, with a 30-day money-back guarantee. Ivacy Demo Ivacy is a provider that's only getting more and more popular, and that's in large part due to its excellent iOS app! The service might not be at the top of our list, but it's consistently praised by iPhone VPN users and we think it is a service well worth considering. An Ivacy subscription won't cost you an arm and a leg, for a start, and there are apps for all platforms – which is perfect if you plan to protect more than just your iPhone. I used Ivacy on an iPad, an Android tablet, and a Windows PC and found it to be reliable on all three. Ivacy's iOS app looks a lot like the Android app, and allows users to select between the IKEv2 and L2TP/IPsec protocols. Unfortunately, there's no kill switch or split tunneling available, but there is in-app support for dedicated IPs. I checked the iOS app for security purposes and was happy to find that it implements strong AES 256-bit encryption alongside the IKEv2 protocol. This is a reliable protocol that you can trust, and it comes set up securely when you download it, which makes it good for beginners who are wary of tinkering with advanced settings. Ivacy claims to be a no-logs provider, though some users may call that claim into question when they see that the service does keep hold of some data and reports. It's a very minimal level of logging, however, and all for the purpose of customer support – we at ProPrivacy don't think that users have cause to be concerned, and are happy to call Ivacy a no-logs provider as a result. Ivacy's base in Singapore is another plus point, seeing as the country is not required to keep tabs on what folks are doing online. Whilst you can pick up a one-month subscription from Ivacy, you'll actually save way more money in the long run if you go for a lengthier plan. Of course, if you do try the service and decide it's not for you, most Ivacy plans are covered by a 30-day money-back guarantee, so you still have freedom to change your mind. You can pay for your plan via PayPal or card, amongst other options, but those of you looking for some extra security and anonymity will be glad to learn that Bitcoin payments are also accepted. Just remember that Ivacy will always know your real IP address. Ivacy impresses us right away by offering 10 simultaneous connections. This is roughly double the amount that most VPNs provide, and should be more than enough for most users, whether you want to share your subscription or protect all your devices. Ivacy's server network is likewise impressive, spanning over 69 countries
and boasting speeds that are downright blistering! In fact, Ivacy is often at the top end of our speed tests. You'll have no trouble unblocking streaming services like Netflix, Amazon Prime, and BBC iPlayer with the service, and sluggish streams and low-quality image pictures will be a thing of the past. Ivacy is also more than quick enough to handle VoIP calls, online gaming, and P2P – there are even dedicated torrenting servers for those interested! ProtonVPN is the best privacy-oriented iOS VPN. With a zero-logs policy, open source code, and OpenVPN encryption. Includes a 30-day money-back guarantee. From the people who developed the popular secure email service, ProtonMail, ProtonVPN is a no-logs Swiss VPN service that has a strong focus on privacy. It also has an excellent 100% free tier that's more than good enough for a lot of VPN users. The iOS app uses the IKEv2 protocol by default, but also offers OpenVPN and WireGuard. An iOS widget is available, and the app provides full access to ProtonVPN's Secure Core (double hop) VPN servers. The iPhone app looks polished, navigating through it is seamless, and you can hop from server to server in a few taps. If we're honest, ProtonVPN isn't necessarily the fastest VPN out there, but it's certainly one of the more security-conscious. ProtonVPN's Secure Core servers are based in Switzerland, Iceland, and Sweden, and all protected by the most staunch privacy laws. iOS users can connect to these multi-hop servers, which ensure that your data is routed through numerous servers before it actually leaves the ProtonVPN network. ProtonVPN's Always-on feature means that, if you disconnect from your VPN server, it'll make sure you reconnect as quickly and smoothly as possible. I also like that iOS users can count on DNS and IPv6 leak protection. This ensures that your real IP address isn't accidentally exposed at any point. It's particularly cool to see ProtonVPN introduce NetShield for iOS users! NetShield can banish malware, trackers, and invasive ads from domains known to contain malware, and can even speed up your connection, too. This is the kind of feature I'd like more VPNs to start looking into for mobile apps, though currently only ProtonVPN's Plus and Visionary users will be able to check it out. Plus users actually get a number of extra features! ProtonVPN has a modest network of servers, dotted across 91 countries
, and you'll be able to access US Netflix by connecting to any of these. However, Plus users gain the ability to browse local versions of Netflix instead by connecting to special "Plus" servers. There are also dedicated P2P and TOR over VPN servers, amongst others, but again, you'll need to be subscribed to the Plus plan to enjoy these neat features. ProtonVPN doesn't hide the fact that it puts security first, and folks who are searching for a more feature-rich provider might decide to look elsewhere. However, ProtonVPN excels at boosting user security and privacy, thanks to AES 256-bit encryption and a no-logs claim that we're happy to verify. ProtonVPN's app code is all open-source, and the VPN makes its home in Switzerland, which is generally thought to be a stellar place for security, due to the country's strong data privacy laws and the fact that it isn't a member of the Five or Fourteen Eyes spying alliance. 1. ExpressVPN
Pricing
Pros
Cons
App Store score:
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks
Website

Super security
Instant unblocking power
A premium price
Pricing
Pros
Cons
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks
Website

Content galore

No experience necessary
Speed and security
Pricing
Pros
Cons
App Store score:
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks
Website

The streamer's dream
Privacy minded
Unlimited connections... seriously!
Pricing
Pros
Cons
App Store score:
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks
Website

Server selection
Beginner friendly
Make it your own
Pricing
Pros
Cons
App Store score:
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks
Website

Private by name and nature
Content on the go
Customer service excellence
6. VyprVPN
 www.vyprvpn.com
www.vyprvpn.com
Pricing
Pros
Cons
App Store score:
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks

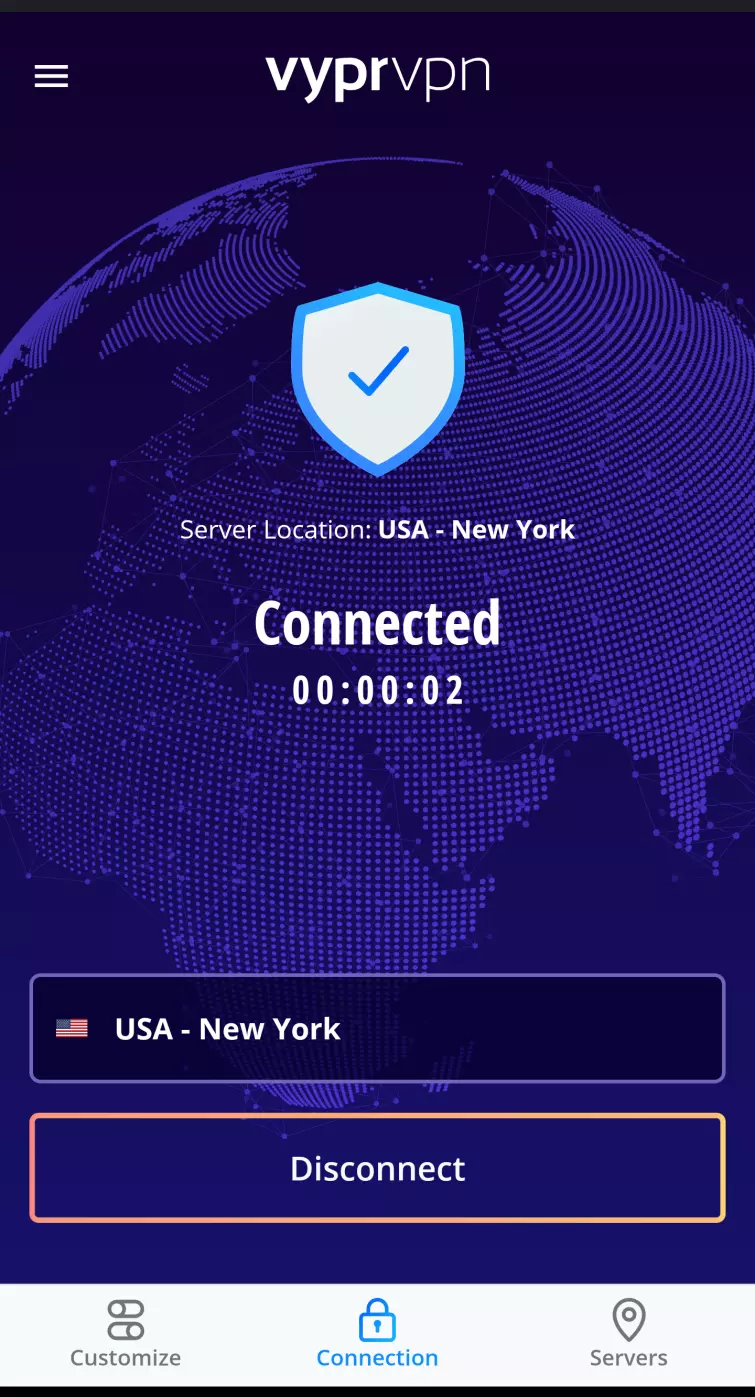
Smooth service
Packed with features
Security on the go
Pricing
Pros
Cons
App Store score:
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks
Website

Super security
Easy streaming
Real customer care
Pricing
Pros
Cons
App Store score:
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks
Website

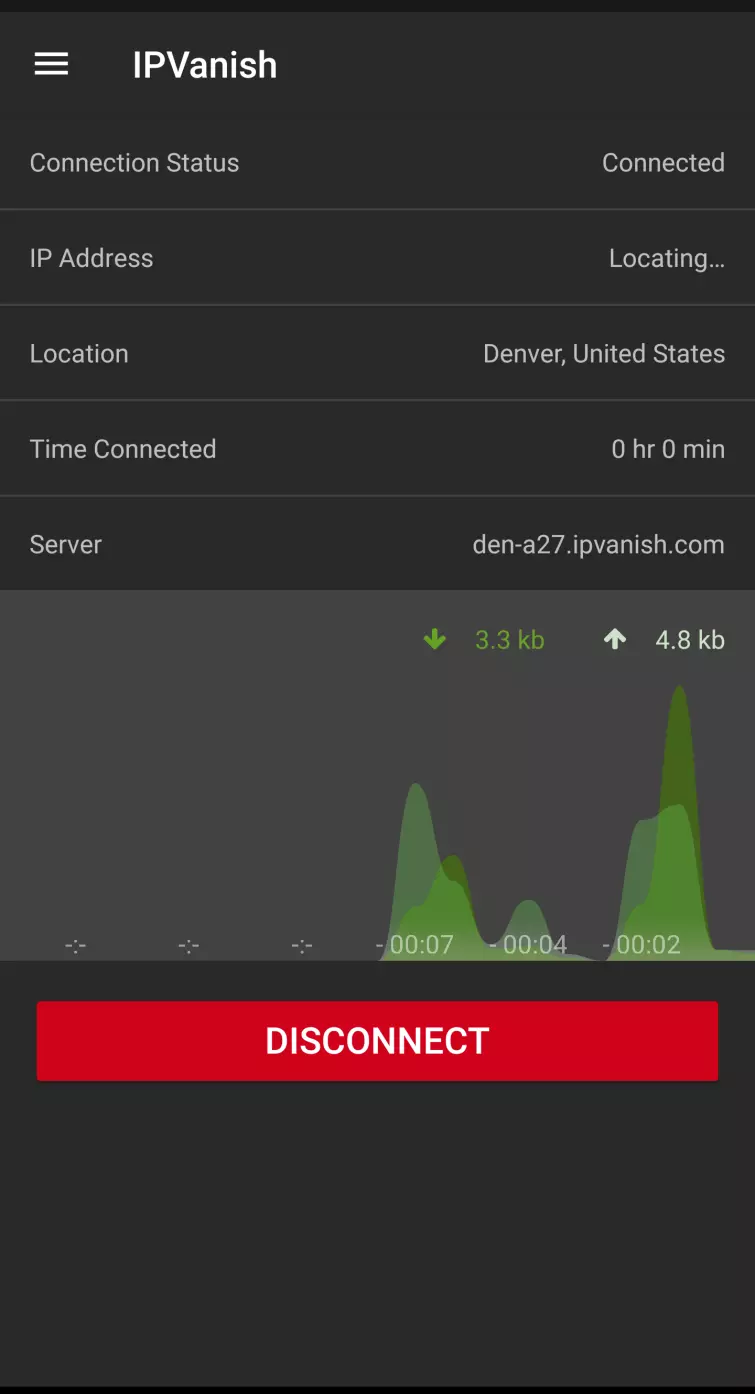
Superb servers
Take your encryption with you
Made in the USA
Pricing
Pros
Cons
App Store score:
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks
Website

Reliable security
Save money over time
An impressive toolkit
Pricing
Pros
Cons
App Store score:
Integrated kill switch?
Also available for:
Simultaneous connections
Unblocks
Security comes first
Awesome extras
A name you can trust
Methodology: how we select the best VPNs for iPhone
Our comprehensive testing methodology helps us find the perfect VPNs for securing your iPhone browsing, streaming your favorite content from abroad, and protecting your device on public wi-fi.
We have several criteria that help us with our selection process, and you can see some of what we looked for when selecting the best VPNs for iPhone below:
- We only consider VPN providers that use the best possible encryption standards, such as AES-256.
- Since you'll likely be using your VPN for streaming and browsing on your iPhone, we only consider providers that offer fast speeds.
- The VPN you select should have apps for all the devices you use, including your iPhone.
- We look for VPNs that are easy to set up and use on your iPhone.
- If you run into any issues using your VPN on your iPhone, it's essential to have customer support that can help – ideally 24/7.
- The more servers a VPN provider has, the more likely you are to find a server that's fast and close to your location.
- We only consider VPN providers that offer good value for money.
These are just some of the criteria we look at when selecting the best VPN for iPhone. If you're looking for a VPN to use on your iPhone, keep these factors in mind, and you can also check out our complete testing process to understand more.
Which is the fastest VPN for iPhone and iOS?
An important factor to consider when comparing VPNs is always going to be speed – especially if you want to game, torrent, or stream videos online. We run regular speed tests on our recommended iOS VPN apps, so you can check out just how quick they are yourself, and the most recent results are in the table below.
| ExpressVPN | NordVPN | Private Internet Access | |
|---|---|---|---|
| ProPrivacy.com SpeedTest (average) | 100 | 85.9 | 62.2 |
| Speed | 100 | 568.0 | 254.93 |
| Performance | 10 | 9 | 8 |
| Reliability | 9 | 8 | 8 |
How do we decide on the best VPNs if you're using iOS?
There are a lot of consumer-facing VPNs on the market in 2024 – and that can make picking out your perfect match a daunting task. Plus, all of these services claim to be the cream of the crop. The truth is that they all differ massively, and you can't trust you'll get the same level of security and privacy with every VPN.
Apple's iOS has traditionally been severely under-represented when it comes to VPN apps. Nowadays, though, all trustworthy providers have a dedicated app for Apple devices. Those that don't are unlikely to be worth your time anyway.
There are scores of unsavoury VPNs available. Some have lax privacy policies that allow them to collect your data and sell it on to third parties, while others will serve you disruptive ads, and may even lack basic encryption. These VPNs aren't fit for purpose, and I'd recommend avoiding them entirely.
We check for the following important factors when weighing up which VPNs deserve a spot in our top 10:
- A strong no-logs policy – This one is vital, seeing as a no-logs provider ensures that your identifiable data stays private.
- Security features – All VPNs should have your security in mind, and offer tools like a kill-switch and leak protection, and robust encryption.
- Connection speeds – To stream HD content and hop into VoIP calls, you'll need a fast VPN that can keep up with data-intensive tasks.
- Server locations – Stable servers in key locations across the globe are essential for regaining access to content (you've already paid for) when traveling overseas.
- Ease-of-use – A VPN with unintuitive apps, or one that's downright difficult to use, just isn't worth your money!
- Compatibility – You'll need a VPN that works with iPhone and iPad, as well as any other devices you plan to protect.
- Simultaneous connections – Another key factor. This allows you to protect all the devices in the home, or even share your account.
- Money-back guarantee – This allows you to test the service before fully committing, and without risking a single penny.
All of the VPNs in this guide were tested by the ProPrivacy team, and subject to a thorough review process – which you can read more about by clicking here. These are also the services we use in our day-to-day lives, so you can rest assured that our recommendations are based on first-hand experience as well as industry insight.
| No Value | ExpressVPN | NordVPN | Surfshark | Private Internet Access | PrivateVPN |
|---|---|---|---|---|---|
| Logs IP address | |||||
| ProPrivacy.com SpeedTest (average) | 100 Mbps | 85.9 Mbps | 41.0 Mbps | 62.2 Mbps | 55.5 Mbps |
| Server locations | 160 | 135 | 140 | 84 | 200 |
| OpenVPN | |||||
| Android | |||||
| iOS | |||||
| Windows | |||||
| macOS | |||||
| Linux | |||||
| Free trial length | 7 days | ||||
| Simultaneous connections | 8 | 10 | 1000 | N/A | 10 |
How does a VPN for iOS work?
VPN stands for Virtual Private Network. A VPN is an online service that encrypts your data and conceals your location. As a nifty byproduct, it also allows you to pretend to be in a different geographical location!

With a VPN, you'll have unlimited online freedom whilst using your iPhone or iPad. For instance, you'll be able to access websites that would otherwise be blocked by your ISP, restricted by the government, or locked away by your employer or school.
You can also access content that is supposed to be geo-restricted where you live. This comes in handy if you want a larger variety of shows and movies to browse while using Netflix, or if you'd like to access TV stations from overseas (such as the UK's BBC iPlayer).
Using a VPN to pretend to be in a different country is super fun, and useful! It can let you access internet banking while on holiday, or log into your cable TV subscription even though you are traveling abroad on business.
A VPN also keeps your data secure from hackers and government snoopers so that you can browse with peace of mind. This prevents coffee shops, hotels, and airports from knowing what you're getting up to online, and protects your privacy. A VPN can also prevent you from falling victim to fake wi-fi hotspots setup by opportunistic criminals.
This is only a brief overview of what a VPN is and can do. To learn more, be sure to check out our in-depth what is a VPN? guide.
What can you do with a VPN for iPad and iPhone?
By using a VPN, iPhone and iPad users can:
- Bypass censorship and access geo-restricted content.
- Stream and download movies securely. Find out how with our guide to safely downloading torrents on your iPhone.
- Stop your ISP tracking your web habits and collecting metadata on behalf of the government.
- Encrypt all your data to stop it from being hacked on public wi-fi.
- Access streaming sites currently blocked in your region. For example, you'll be able to access Netflix and countless other online services.
For more information, check out our guide to streaming US Netflix on your iPhone. Alternatively, head over to our VPN for Netflix guide for a list of the best services and information about accessing the service on other devices.
Still not convinced? We recommend checking out our Do I need an iPhone VPN? guide to find other ways that you could benefit from using a VPN while online.
Will an iPhone VPN work for streaming?
Yes. When you connect to a VPN on your iPhone, you will get a valid IP address in the location you select. As a result, you can use the VPN to access your favorite streaming services on vacation. You can also connect to a VPN server abroad to access foreign services.
For example, you could connect to a server in the US to watch US TV channels like ABC, NBC, and ESPN. Or connect to a server in the UK to watch BBC iPlayer, ITVX, and Channel 4.
The same is true of any other country. So, if you want to access TV in Germany, Australia, Italy, Spain, or anywhere else, simply connect to a VPN server in that location.
Can I use a VPN on iPhone to bypass blocks at work?
Some employers block certain websites and services. This includes blocking streaming sites such as YouTube and Netflix, gaming sites, social media sites, and anything else that they believe might distract employees.
The good news is that you can use a VPN to bypass these blocks. When you connect to a VPN server in your iPhone while connected to the work's wi-fi, you appear to be outside of that network. As a result, you can sidestep any blocks enforced by your employer.
Best of all, a VPN also provides encryption for your connection. This means that your employer will not be able to detect that you are bypassing the blocks placed on the wi-fi. As a result, you can access anything you want on your iPhone in complete privacy.
That said, remember that a VPN cannot stop your boss from walking up behind you while you are watching TV or accessing another restricted website. Thus, you should still try to follow the rules whenever possible and only access restricted sites during your downtime and on your own devices to avoid getting in trouble.
Compare the encryption protocols offered by the best VPNs for iOS
VPN services are first and foremost a privacy tool. VPNs allow users to access websites and services without being tracked. They also let users log onto public wi-fi securely, without fear of hackers getting their hands on their personal data.
VPNs protect users by encrypting their data, and there are several encryption protocols that each provider uses in their iOS apps. The encryption protocols offered by the apps in our list above are:
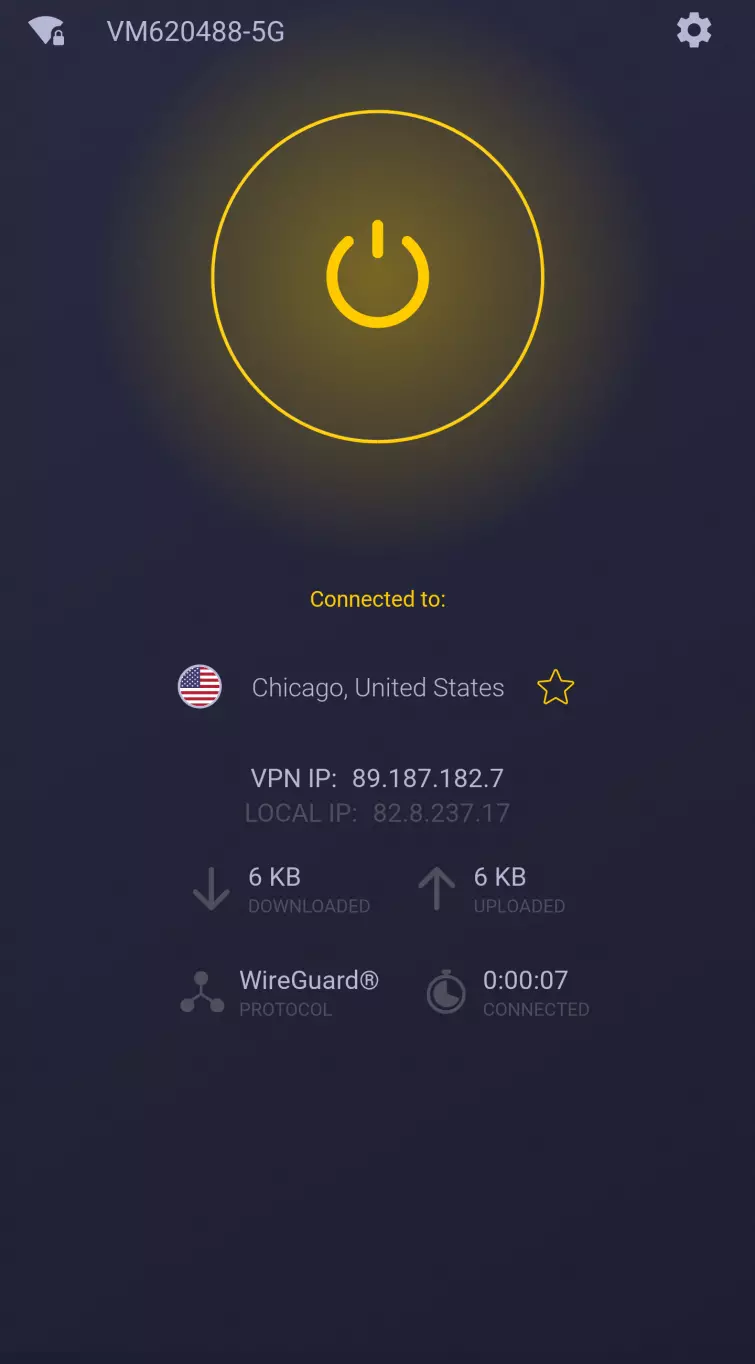
- WireGuard - The most recent protocol, and also the fastest. It's lightweight and the go-to option for many providers.
- OpenVPN - A popular and trusted protocol that's been in use for more than two decades.
- IKEv2 - A good alternative to OpenVPN that is often used on iOS VPN apps, and usually paired with IPsec.
In the table below, we compare what encryption protocols are used by the iOS VPN apps we recommend. These encryption standards are offered on both the iPhone and iPad apps.
| VPN Provider | OpenVPN | WireGuard | IKeV2 |
|---|---|---|---|
| ExpressVPN | Yes | No | Yes |
| NordVPN | Yes | Yes | Yes |
| CyberGhost | Yes | Yes | Yes |
| Private Internet Access | Yes | Yes | Yes |
| SurfShark | Yes | Yes | Yes |
| VyprVPN | Yes | Yes | Yes |
| IPVanish | Yes | Yes | Yes |
| PrivateVPN | Yes | Yes | Yes |
| IvacyVPN | No | No | Yes |
| ProtonVPN | Yes | Yes | Yes |
iOS 17 privacy enhancements
Apple's newly released mobile operating system for iPhone and iPad – iOS 17 – is jam-packed with superb security enhancements that'll work hand-in-hand with your VPN, further optimizing your privacy.
Improved Lockdown Mode
Lockdown Mode in iOS 17 selectively turns off features such as iMessage and HomeKit to prevent their exploitation by spyware. It also automatically removes geolocation data from shared photos, and blocks connections to 2G cellular networks and automatic connections to non-secure wi-fi networks.
More private browsing
iOS 17 completely blocks known trackers from loading on visited web pages. It also removes tracking added to URLs as you browse on your iPhone. You can use the feature solely in private browsing or change your settings to apply it to all browsing sessions.
Can you get a free VPN for iPhone?
There are a number of free iOS VPNs that you can trust, but it's important to be aware of their limitations. It's just as important to understand why it's better to stay away from many of the free VPN options for iPhone and iPad, seeing as the majority will put your privacy at risk.
Most of the free VPNs in the app store are slow and impose strict monthly data limitations – which makes anything outside of the most basic day-to-day browsing activities a laggy, frustrating struggle. Worse still, some services will actively collect your data to sell to third-parties. This is the exact opposite of what a VPN service should do, and should stand for.
There are some free VPNs you can trust, you can find a list of them on our free VPN page.
Still want a free iOS VPN? We recommend Windscribe (free option)
If you're looking to protect your wallet, then Windscribe is a great free VPN service. Not only does it offer the same solid security measures that you'd get on its paid plan, but it also gives users a 10GB data allowance each month. This might not go far if you're streaming HD content, but it's more than enough for your usual day-to-day browsing.

Want more choice? Visit our free VPNs for iOS guide for some other solid recommendations.
Top-tip: Get ExpressVPN for Free!
compatibility, not a full VPN service. This means that it is possible to configure a third-party VPN provider's configuration files to use on your iOS device if the provider doesn't offer a full-on iOS app. The VPN providers we list in this guide, however, all offer fully-functional iOS apps that complete the setup for you automatically so you don't have to configure the files manually on your iPhone.
Best VPN apps for iOS FAQs
Conclusion
Now that you have all the information you need about VPN apps on iOS, let's review our top picks:
- ExpressVPN - The best VPN for iOS. Offers lightning-fast speeds, slick apps, and a 30-day money-back guarantee.
- NordVPN - The best value iOS VPN. It's reliable, works with most streaming platforms, and its apps are easy to use!
- Surfshark - The best multi-device iOS VPN. Offers unlimited simultaneous connections, tons of features, and WireGuard encryption!
- Private Internet Access - The best secure iOS VPN. Super secure, zero-logs, and with a full suite of customizable tools.
- PrivateVPN - The best user-friendly iOS VPN. Works with lots of streaming sites and is consistently fast, offering servers worldwide.









