Canvas fingerprinting is a special form of browser fingerprinting developed and used primarily (over 95 percent) by web analytics firm AddThis, although other companies such Plenty of Fish and German digital marketer Ligatus are also guilty.
As with browser fingerprinting, it is a sneaky way to uniquely identity web users’ browsers, so that individuals can be tracked for advertising purposes as they visit different sites across the web.
It is a script that works by asking your browser to draw a hidden image, and uses tiny variations in how the image is drawn to generate a unique ID code, which can then be used to track you.
Because canvas fingerprinting requires both the HTML5 Canvas API and JavaScript to work, it can be effectively blocked by disabling JavaScript in your browser. In terms of security this is a great idea anyway, but since much of the functionality of the web relies on JavaScript to work, for many this will be a somewhat nuclear option that overly negatively impacts their browsing experience.
Similarly, the Firefox Add-on NoScript can be used to block JavaScript from known fingerprinters such as AddThis, but using it requires decision making and the knowledge/research on which to base these decisions (NoScript can block JavaScript by default, but this brings with it similar problems to simply disabling JavaScript.) We should stress, however, that for advanced users who don’t mind the hassle, NoScript is the best defence against a wide range of internet threats.
In theory you can install the AddThis opt-out cookie to opt out of targeted advertising by AddThis, but this means that you have to trust AddThis to keep their keep its word over not targeting you for ads, and does not anyway protect you from actually being fingerprinted.
A far better solution (and much less intrusive than blocking JavaScript or using NoScript) is the CanvasBlocker Firefox Add-on. This blocks canvas elements on a webpage, while also giving users control of exactly which elements are blocked.
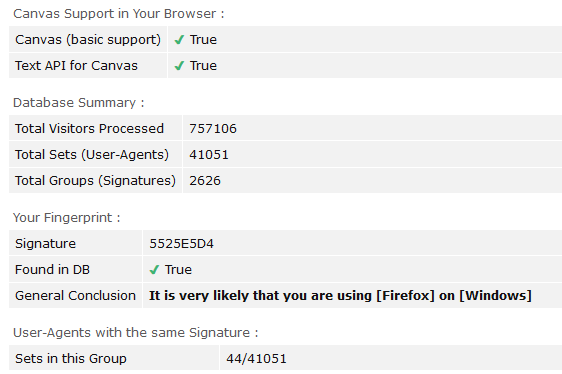
Canvas fingerprint before using CanvasBlocker
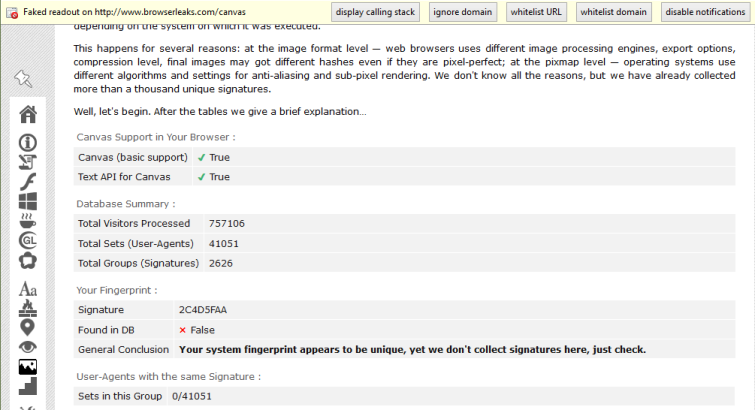
Canvas fingerprint using CanvasBlocker in default ‘fake readout’ mode (screenshot also shows available CanvasBlocker options)
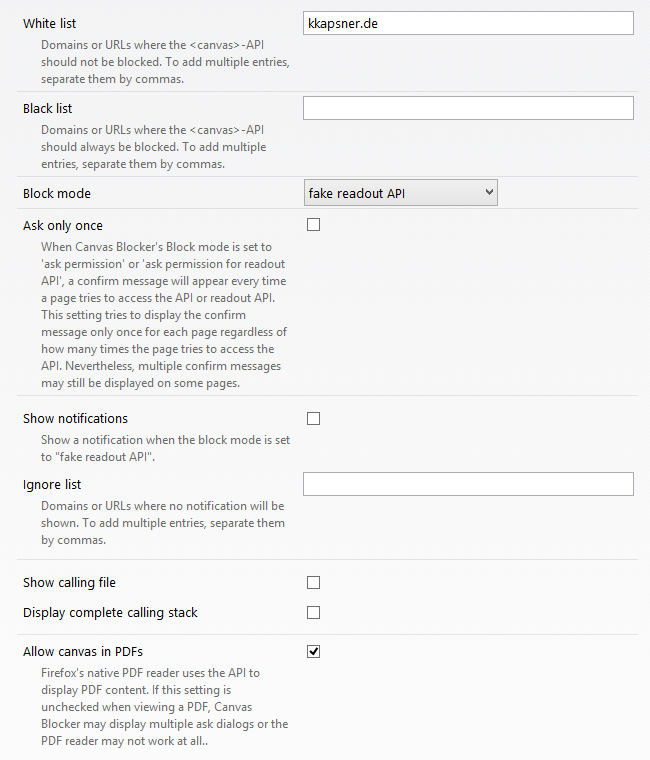
In addition to the default ‘fake readout’ mode, you can chose how CanvasBlocker deals with canvas requests by default (block readout, ask for readout, block everything, allow only on whitelist, ask for permission, block only black list, and allow everything)
An interesting option is to allow canvas in PDF’s, as Firefox’s native PDF reader uses canvas to display PDF content.
You can check whether CanvasBlocker (or any other canvas fingerprinting blocking method) is working, visit the HTML5 Canvas Fingerprinting test page on Browserleaks.com.
The CanvasBlocker Add-on for Firefox can be downloaded here, and Chrome users can download a similar extension called CanvasFingerprintBlock here.
