For the second of our on-the-floor live Infosecurity Europe 2018 conference reports, we’ll just dip into a couple of talks we attended that had relevance for privacy and personal security.
Anatomy of VPN Hacks: Is 2FA Enough?
This talk was more concerned with security for corporate networks than the kind of commercial VPNs that ProPrivacy.com deals with. That said, it made some salient point about two factor authentication (2FA) that apply to most online security situations.
2FA is an invaluable tool that meaningfully improves the security of most systems. But it is not perfect. This is because:
- It's hard for users to operate.
- It cannot be used in many situations. For example, with most iOT devices, while on a flight, or when driving.
- It can be hacked. SMS based 2FA is particularly vulnerable as the SS7 international mobile network backbone is highly insecure. Indeed, O2 has confirmed online thefts using stolen 2FA SS7 codes.
Unfortunately, the solution offered by the talk - internal monitoring of connections to look for suspicious source geolocation, abnormal IP source for users, impossible travel, and suchlike, is not helpful in a commercial VPN context.
The Ultimate Guide to new ePrivacy Regulations: Cookie Consent, DNT, & Online Tracking Technology
This talk explained how the EU plans to the the ePrivacy Directive into the ePrivacy Regulations.
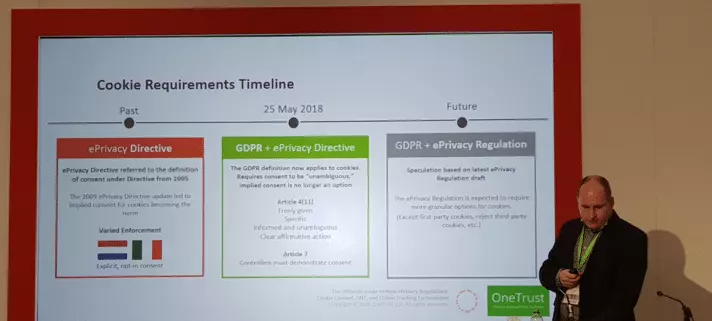
Combined with the GDPR, this is set to drastically change how websites will need to treat the subject of user consent for cookies and other web tracking technologies. Most importantly, implied consent or “consent by coercion” (“You must agree to use of cookies if you want to use this website”) simply will not fly.
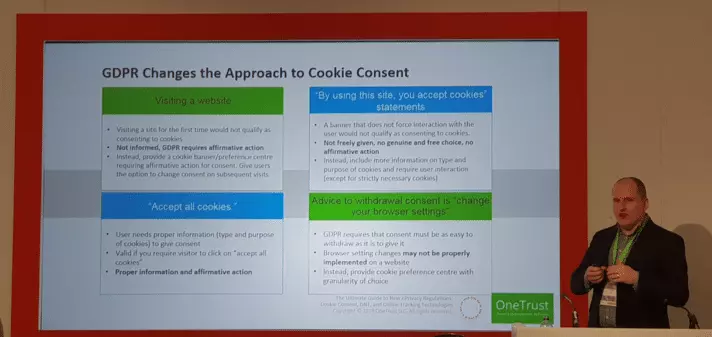
Consent for tracking must be granular, and it must be ongoing. This means we are likely to see more cookie and tracking management consoles that allow website users to access and adjust their tracking preferences.
It will be interesting to see if the new ePrivacy Regulations if we will finally reduce the need to rely on anti-tracking browser add-ons to protect your online privacy.
Conclusion
In addition to providing the ProPrivacy.com team an opportunity to connect with friends old and new in the cybersecurity industry, we learned some useful and occasionally fascinating stuff. Participating in the event has even inspired us... Watch this space!
