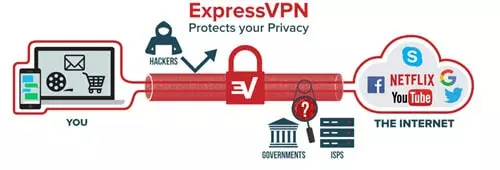
Virtual Private Networks (VPNs) provide a service that allows you to pretend to be in a different country. This allows you to overcome any local network restrictions that Internet Service Providers (ISPs), workplaces, and other network administrators put in place. In addition, VPNs allow you to overcome the censorship that many draconian governments impose. Finally, they also permit you to (privately and securely) bypass geo-restrictions (geographic website restrictions), so that you can access foreign services and website content.
Earlier this month, news emerged of a study which alleged that VPN providers (including PureVPN, HMA and ExpressVPN) had been unclear about some of their server locations. This led to some negative publicity about those VPNs, not only because of a perceived lack of transparency but also because of security issues that arise from the nondisclosure of actual server locations.
Since the news broke, ProPrivacy.com has been working with security experts and the VPNs involved in order to ascertain whether there has been any wrongdoing. Consumers want to know if they have been put at risk. They also want to know why VPNs have been doing this. Could there be a legitimate reason?
Virtual Locations: Why?
The original report claimed that VPNs hadn't been clear about server locations in order to look better than they actually are and get more customers. In reality, these motives are untrue for the majority of the providers in question. We communicated directly with ExpressVPN, which is the best of the VPNs referenced in the report. We asked why it had allegedly been advertising false server locations. The answer made it clear that it had only done so in order to provide a better service for consumers.
Firstly, ExpressVPN told us that only 3% of its servers (representing 1% of its overall traffic) are in a different location to the one advertised. In every single one of those cases, connecting to the server provided an IP address located in the endpoint location that the consumer wanted. This is achieved with what is referred to as “virtual server locations”. This is what ExpressVPN told us:
“ExpressVPN has rigorous standards for servers to ensure that users are able to connect securely, reliably, and at consistently fast speeds. In some countries, it can be difficult to find servers that meet these qualifications. Virtual server locations make it possible for users to connect to such countries, while still providing the connection quality they expect from ExpressVPN.
"For example, some of our users requested Bangladeshi IP addresses to access Bangladeshi content, yet we were unable to find reliable servers physically in Bangladesh. To meet these customers' needs and provide reasonable speed and reliability as well, we decided to offer a virtual solution for them. The alternative would be not providing this service at all, or providing speeds of less than 1 Mbps from a physically located server.”
Impossible Locations
ExpressVPN has assured us that it only ever implemented virtual server locations in response to requests from consumers. Those consumers had specifically asked for endpoint IP addresses in countries where the firm couldn't get good enough servers.
ExpressVPN was left with two options: either not to provide an IP address in those countries; or to use a server nearby to provide a virtual server location. The latter allowed its subscribers to get an IP address in the desired endpoint locality. ExpressVPN decided in favor of providing the service. It knew that doing so would allow people who needed to use geo-restricted services from those countries to do so.

False Allegations?
ExpressVPN believes that it is providing virtual server locations for the betterment of its service. The company told us that it doesn't hide the fact that it uses virtual server locations:
“We have a page on our website explaining what virtual server locations are, how they work, and which countries have virtual server locations. A brief description of virtual server locations and a link to the aforementioned page can be found on the page listing server locations as well.”
Unfortunately, the problem with ExpressVPN’s comment is that when you use its software, it doesn't disclose that you are using a virtual server location. For me, this does raise questions. Less techy consumers will simply assume that their data is being processed by servers in the country they chose.
Even techy users would need to have visited the ExpressVPN website and landed on the virtual servers page in order to find out information about those virtual servers. This is far from ideal.

Security Implications
The big question surrounding this practice is whether there are security risks involved for consumers. Are users at risk when they connect to a server location that isn't where they thought?
To give you a well-rounded answer to this, we decided to ask cybersecurity experts at some of the world’s leading firms that very question. Mark Nunikhoven, VP cloud research for Trend Micro, told us:
“A VPN is an encrypted connection from the user to the provider and then the provider makes the outbound connections to the rest of the internet. If the provider’s system is sitting in a specific country, that system can be seized, searched, and any number of other activities that are legal in that jurisdiction.
"Not knowing the location of your VPN service definitely has a privacy impact. Jurisdictions have very different privacy expectations and regulations. Expecting to have your privacy protected by one jurisdiction only to find out that your data is sitting in another jurisdiction can be disastrous.”
That sentiment was reinforced by Mike Sandhu, Director of Product Management at Norton by Symantec:
“It is possible that there may be security issues associated with this, but lying about the location of a server is also concerning because it impacts the credibility of the VPN provider. If left unchecked, VPN services can potentially view your data at point of offload and use it for a variety of purposes including profiling, advertising and even hacking.
"Ultimately, VPN users are being asked to put their faith in providers. They are trusting that the providers will route their traffic through a server in a country the user chooses with a secure connection. It’s a disservice to consumers if a provider is unable or unwilling to do this.”
However, ExpressVPN disagrees with this risk assessment. They told us:
"The same level of security applies to all ExpressVPN servers regardless of location. We have multiple technological measures in place to ensure that personally identifiable information aren't logged or even hit a disk, that servers aren't tampered with, and that we aren't vulnerable to man-in-the-middle attacks. Even in the case of server seizure by a government, ExpressVPN customers aren't put at risk".
Data Seizure
The main problem surrounding virtual server locations is that the authorities could seize usage data. That could lead to a VPN becoming a honeypot for the authorities of a particular country. This would be particularly concerning if, for example, data was being processed by a VPN server in the US (where a VPN provider could be served a warrant and gag order). In addition, it would be more problematic if the true VPN server location was in a country that is a part of the 5 Eyes surveillance agreement, or to a lesser degree the 14 Eyes agreement.
So, where are the real servers located, and is consumers' privacy at risk?
The ExpressVPN webpage on virtual server locations reveals that there are 29 server locations in total.

List of ExpressVPN virtual server locations
- Andorra (via the Netherlands)
- Armenia (via the Netherlands)
- Bangladesh (via Singapore)
- Belarus (via the Netherlands)
- Bhutan (via Singapore)
- Bosnia and Herzegovina (via the Netherlands)
- Brunei (via Singapore)
- Ecuador (via Colombia)
- Guatemala (via Colombia)
- India (via the UK)
- Indonesia (via Singapore)
- Isle of Man (via the Netherlands)
- Jersey (via the Netherlands)
- Laos (via Singapore)
- Liechtenstein (via the Netherlands)
- Macau (via Singapore)
- Macedonia (via the Netherlands)
- Malta (via the Netherlands)
- Monaco (via the Netherlands)
- Montenegro (via the Netherlands)
- Myanmar (via Singapore)
- Nepal (via Singapore)
- Pakistan (via Singapore)
- Peru (via Colombia)
- Philippines (via Singapore)
- Sri Lanka (via Singapore)
- Turkey (via the Netherlands)
- Uruguay (via Argentina)
- Venezuela (via Colombia)
Doing the Sums
Considering that ExpressVPN provides servers in 94 countries, that would seem to be a lot more than 3%. So, what gives? Well, it is true that only 3% of the total number of ExpressVPN’s servers are virtual servers. However, it's also true that 30.85% of the countries that it provides IP addresses for are, in reality, using virtual servers.
To me, this feels like ExpressVPN is using a loophole technicality to underplay the situation. It troubles me in terms of transparency. I am the first to agree that ExpressVPN is a top-end service. It's clear from the user feedback we get about the service that it runs a tight ship. In addition, ExpressVPN does have the infrastructure in place to adequately cope with large numbers of new subscribers (not all VPNs can accommodate the large of number of consumers that ExpressVPN copes with - in fact, very few can).
ExpressVPN also has excellent, fully featured software. It has a good privacy policy and, although it keeps minimal connection logs, those are aggregated and can't be pinned to any one specific user. In addition, I don’t doubt that, on the whole, ExpressVPN was attempting to meet the needs of consumers (and their desire for IP addresses in specific locations).

A Closer Look
However, the cybersecurity experts at Trend Micro and Symantec are right. Not knowing that you are using a virtual server is a security issue. It exposes data to different jurisdictions than the ones you believe are processing your data.
Thankfully, eight of the virtual server locations listed process data in the Netherlands. That country is very secure in terms of data privacy.
Singapore, although generally authoritarian and harsh on copyright protection, doesn't have mandatory data retention laws. It's also generally considered secure in terms of data privacy, but it isn't ideal.
The Venezuela, Equador, and Guatemala servers are actually in Colombia. With the current political situation in Venezuela, I'll stick my neck out and say that data being stored in Colombia is an advantage. I say this in spite of the fact that Colombia is a terrible place for digital privacy. One presumes that the server is located there to provide users with fast enough connection speeds. Otherwise, Colombia would be an awful choice. For users wanting to connect to Guatemala and Equador, this isn't great news.
Argentina, where the Uruguay server is located, is also a bad place for a VPN server. Argentina passed mandatory data retention laws in 2013. Uruguay has much better data privacy laws. As such, this can definitely be seen as a security concern.
The Indian IP address that is being processed by UK servers doesn’t ring too many alarm bells. However, the UK has GCHQ, is an active partner of the NSA, and is a member of the 5 Eyes surveillance agreement. With that in mind, it's not ideal however ExpressVPN told us that they also have India server locations physically in India as well, and that the India (via UK) option is clearly labeled as such in their apps. It is therefore important for consumers using the Indian IP address to check this so that they can make an informed decision.
More Transparency Please!
Although ExpressVPN discloses its use of virtual servers, and isn't hiding that fact from its users, in my opinion they aren’t advertising it well enough either. Transparency is incredibly important, especially when it concerns consumers' digital privacy.
For this reason, we urge ExpressVPN, HMA, PureVPN, and any other VPNs that are using virtual server locations to make it clear exactly which servers are virtual and where subscribers are actually connecting.
At the end of the day, this isn’t a scandal. As far as I can tell, this practice hasn't harmed any consumers as yet. However, there's no doubt that more transparency would be good for consumers, good for the VPNs' reputations, and good for the VPN industry as a whole.
Opinions are the writer's own.
Image credits: christitzeimaging.com/Shutterstock.com,
Creative Stall/Shutterstock.com, igorstevanovic/Shutterstock.com
