Price
24 months + 2 months FREE
$99.95 billed every 24 months, includes 2 FREE months12 months
$79.95 billed every 12 months1 month
Free
10 GB data transfer,Users can opt for the limited free plan, or subscribe for the one-month, yearly, or two-year plan – whichever suits their needs best. Each of those subscriptions comes with the same features. Whichever way you look at it, hide.me premium is a bit expensive. But right now, hide.me is offering our readers a three-year subscription (with three free months) for $94.99 (that is just $2.43 per month). We also have an exclusive discount for the two-year plan – $99.95 ($3.84 a month). So be sure to click our link below if you are interested in this service!
Hide.me has a free plan that allows up to 10GB per month on one device and five locations to choose from. These restrictions aren't ideal for those that are online frequently or wanting to unblock streaming services, but you don't even need to sign up to use their free VPN plan, meaning you can keep your personal details to yourself.
The monthly plan – which costs $9.95 – is slightly cheaper than the other premium single-month plans on the market. ExpressVPN, CyberGhost, and VyprVPN, for example, all cost more than $12. This price seems fair because like those services Hide.me unblocks many sought-after streaming services – and it has an extremely wide range of advanced VPN privacy features.
A yearly subscription costs $79.99, which is definitely more competitive. But at the equivalent of $6.66 per month, it is still quite expensive. On the other hand, hide.me is extremely competitive with our exclusive three-year discount; which reduces the cost to just $2.43 per month. This makes it a real bargain.
We are happy that hide.me has added this subscription plan and strongly recommend users take advantage of this discount if they like this VPN.
But don't forget that competing VPNs also sometimes have a two-year plan that reduces their cost even further (to less than $3 per month) – so even this "cheap" hide.me plan is slightly overpriced.
Finally, subscribers get a 30-day money-back guarantee to test the service, and we have been assured that the 500 Mb data limit that used to exist has been lifted – so you should be able to test the VPN as much as you like and still get your money back.
Money-back Guarantee
All of our approved VPNs come with a hassle-free money-back guarantee. Should you purchase one of the recommended VPNs via ProPrivacy.com and struggle to get a refund, contact us and we will do our very best to help you get your money back.
Users can pay for a subscription using PayPal, credit or debit cards, iDeal or wire transfer. Hide.me also accepts payment via a range of crypto-currencies. This allows consumers to pay for the service anonymously if they wish.
Payments are handled on behalf of hide.me by the third-party firm, Cleverbridge AG. This is a positive aspect of the service because it means that hide.me does not have payment records stored anywhere near subscriber information. For those that are interested, Cleverbridge is located in Germany, which is generally considered a good place for data privacy.
Unblock Netflix?
We tested hide.me VPN using the Windows client to see if it would unblock popular streaming services. The good news is that hide.me can now unblock Netflix regions, access BBC iPlayer outside the UK, and also access; ITV, Amazon Prime Video, Disney+, Hulu, PlayStation Vue, HBO Now, DAZN, Joyn, Maxdome, RAI, and more.
This makes hide.me VPN a great all-rounder, and much better value for money than it used to be.
Features
Simultaneous connections
10
Server locations
75
Routers supported
Split-tunneling
Total servers
2000
Hide.me is a service that is feature-rich across its various clients. Here is what you get with a premium subscription:
- Zero-logs service, it doesn't request personal info, nor does it keep activity logs
- 2,000 Servers in over 75 locations across 40 countries worldwide
- High-Speed unlimited bandwidth
- Unlimited data on premium plans
- 10 simultaneous connections
- IKEv2, OpenVPN, WireGuard, SoftEther, and SSTP VPN protocols
- Military-grade AES 256-bit encryption
- Windows, macOS, Android, and iOS apps
- Compatibility with Linux, gaming consoles, and smart TVs
- Kill switch
- DNS, IPv4, IPv6, and WebRTC leak protection
- P2P permitted on 99% of the servers on premium plans
- Dynamic Port Forwarding on premium plans
- 24/7 live chat support
- SOCKS proxy
- Static IP (optional)
- Split Tunneling
- Dynamic Multihop VPN
- Unlimited server switching
- Stealth Guard – This firewall feature allows you to choose apps that will only work if you are connected to the VPN. This ensures you never accidentally use these apps without the privacy of the VPN. For example, you could firewall your torrent client to ensure you never leak torrent traffic to your ISP.
- Full IPv6 support – Excellent from a tech perspective, and one of the few VPNs to implement full IPv6 connection compatibility.
- WireGuard protocol (a new protocol that some techy users may prefer)
- Access to popular streams including Netflix, Amazon Prime, Disney+, Hulu. HBO GO, PS Vue, and more.
- Free VPN subscription plan with 10GB of data per month
- 30-day money-back guarantee
As you can see, this VPN has some excellent advanced features that some techy users may need. If that is you, hide.me is definitely worth considering.
Speed and Performance
Connection speeds are a vital component of any VPN, as they will affect what you can do with your VPN on a day-to-day basis. We test hide.me VPN using our rigorous testing methodology. We test the UK, Hong Kong, US, and Australian servers regularly. We check for local burst speeds (in the UK) and average download speeds across all those server locations.
| Hide.me | ExpressVPN | NordVPN | |
|---|---|---|---|
| ProPrivacy.com SpeedTest (average) | 35.3 | 100 | 85.9 |
| Speed | 248.5 | 100 | 568.0 |
| Reliability | 6 | 9 | 8 |
| Performance | 6 | 10 | 9 |
Below, you can see that from June to September 2024, hide.me's download speed averages were 35.3 Mbps and registered a max burst speed of 248.5 Mbps. These are fast connection speeds that put hide.me in range with many other top VPNs on the market. A VPN this fast is more than suitable for all data-intensive tasks such as streaming in HD, gaming, and videoconferencing.
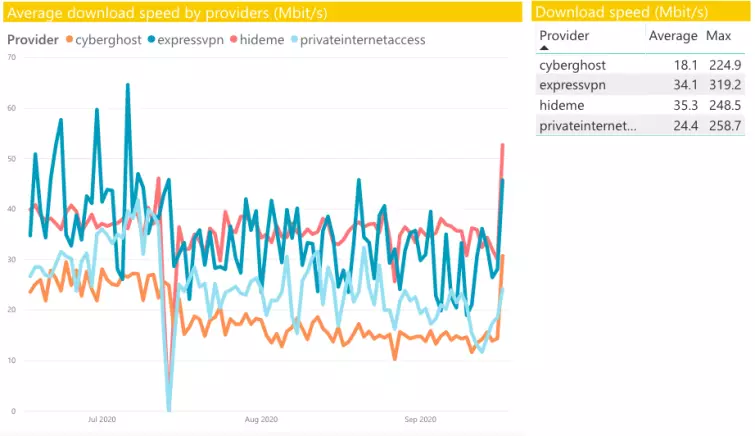
While this is a fast VPN, you can get similar speeds from much cheaper VPNs. So unless you are especially enamored with this service, it is possible to get similar performance at a fraction of the cost. Of course, this service has a lot of extra features and is based in the privacy-friendly country of Malaysia, meaning it could be the right choice for certain people who can justify the extra cost.
Leak tests
ProPrivacy.com SpeedTest (average)
35.3
Speed
248.5
Reliability
6
Performance
6
Using ProPrivacy's very own leak testing tool, we checked for IPv4, IPv6, WebRTC, and DNS leaks. Please read our Complete Guide to IP Leaks to understand why a VPN must never leak.
We tested the macOS client for IPv6 and IPv4 and found no leaks using the most recent Mac client. The very latest version of the hide.me client now has full IPv6 compatibility, so it should no longer have any IPv6 issues.
Next, we checked Windows using the most recent Windows client. First, we tested for leaks using the office's IPv6 connection. We detected no IP leaks, no WebRTC leaks, and no DNS leaks. The screenshot below shows the Windows leak test results.
These are excellent results that demonstrate this VPN can be trusted for privacy purposes, both on Windows and Mac, without concerns about leaks.
Alternative Choices for You
|
|
From $6.67 |
ProPrivacy.com Score
9.6 out of 10
|
Visit Site Read review |
|
|
From $3.69 |
ProPrivacy.com Score
9.4 out of 10
|
Visit Site Read review |
|
|
From $2.19 |
ProPrivacy.com Score
8.6 out of 10
|
Visit Site Read review |
Privacy and Security
Kill-switch
Obfuscation (stealth)
IPv6 leak protection
WebRTC leak protection
Hide.me is based in Malaysia. This is a country where the government does not enforce any mandatory data retention directives on VPNs. As a result, it is considered a great place for a VPN to be based.
Hide.me stores no logs about what people do online using its service. Also, bandwidth connection logs are “securely erased every few hours” and those logs are never kept alongside real IP addresses or timestamps.
Tracking bandwidth use on its servers is non-invasive and is not a concern. For this reason, hide.me is indeed a true no-logs VPN. Hide.me has also joined the i2Coalition VPN Trust Initiative, showing once again its honest intentions towards its users' privacy and security. This is as good as it gets, and the zero-logs policy is one of the best things about this service.
Encryption Implementation
PPTP
L2TP/IPSec
SSTP
IKEv2
OpenVPN
Other protocols
SoftEther, WireGuard
Hide.me provides OpenVPN encryption on all platforms. Since we last reviewed it, hide.me has stopped providing access to several protocols such as L2TP and PPTP. However, SSTP is still available for those who want to use it.
Overall, this is all splendid news for hide.me subscribers, because OpenVPN is our recommended protocol for privacy and security. And hide.me uses a strong implementation of OpenVPN with PFS:
Control channel: an AES-256-GCM cipher with RSA-8192 handshake encryption. Additional authentication is not required with GCM, but HMAC SHA384 hash authentication is also specified in the encryption suite. Perfect Forward Secrecy (PFS) is provided using a standard Diffie-Hellman Exchange (DHE).
Data channel: an AES-256-CBC cipher with HMA SHA-256 hash authentication.
This is an extremely tough OpenVPN implementation thanks to its robust RSA-8192 handshake, which makes encryption with hide.me both secure and future-proof.
The kill-switch is available in Windows, Mac, and Android clients. This is ideal and means that users can ensure they don't leak on all of those clients. The lack of a kill-switch on iOS is not surprising, because this is normal across the VPN industry (and is generally considered to be Apple's fault).
User Experience
Hide.me has a user-friendly website, with everything laid out in an easy-to-navigate menu system. The provider has accessible FAQs, tutorials, and detailed articles in its knowledge base. Subscribing is hassle-free and requires only minimal information (you can use a burner email if you prefer).
The clients are easily available once you sign up, and they install with minimal fuss. We also found the clients to be incredibly informative, whether you are a paying subscriber or free user, with each working excellently. The introduction of a live chat and ticket system in English and German allows users to get the most up-to-date information on new features and servers added to the VPN clients.
We also like the blog on its website, which provides articles on various VPN, privacy, and online security topics.
Customer Service
Money-back guarantee
24-hour support
Live chat
Money-back guarantee length
30
Free trial
Hide.me provides a 24/7 live chat feature, and we found their agents to be knowledgeable. However, we cannot say the same when asking techy questions about certain aspects of the service. We asked about obfuscated servers, for instance, and the support agent could not tell us exactly how obfuscation (stealth guard) is implemented. We found this slightly frustrating as it means that customers will need to send a message via the ticket system if they need answers to more in-depth technical questions.
We asked a few techy questions using the ticket system and found responses to be slow. In addition, we had to press on quite a few times to get the information we wanted. Overall, it left us feeling a little disappointed, considering the high cost of the service.
On a more positive note, hide.me has a useful knowledge base that contains guides for installing the clients and fixing common problems. This is a useful resource that can help most people to get the VPN working correctly. In addition, we like that the service also offers a community forum which can be very helpful for users searching for solutions to any issue. It's also great that the community forum is available in both English and in German.
Windows client
Hide.me's Windows VPN client comes with a kill switch and OpenVPN encryption. For this reason, we consider hide.me to be a Windows-friendly service. With that in mind, many people that require a robust VPN for a single Windows computer may be happy with the cheaper one-device plan. Since we last reviewed hide.me, it has also added a couple of new features to the client: split tunneling and a new Firewall feature (that stops you connecting to the internet unless you are connected via hide.me).
We found that the Windows client performed excellently. And because it provides fast speeds, it is ideal for streaming HD video files and doing other data-intensive tasks such as gaming and video conferencing.
During our tests, we discovered no leaks whatsoever when using the Windows client. And, hide.me has now released Chrome and Firefox extensions designed to stop WebRTC leaks. The kill switch did cut our internet even when the app crashed, which is likely because we had the firewall feature switched on. Overall, it is an excellent Windows client that works efficiently.
The new Stealth Guard feature is perfect for people who use BitTorrent clients to download content regularly and ensures that you will never leak any unencrypted traffic to your ISP. It is basically a split tunneling feature that works in combination with the kill switch to ensure you can never connect to the internet using certain applications, unless the VPN is on.
We also like the addition of Split Tunneling, which will let you connect some of your apps through the VPN while letting others apps surf the web without protection (great if you want to make use of the full speed of your internet connection when privacy is not essential, or if certain apps need to seem like they are located in the country you reside in).
Android client
The Android VPN client provides OpenVPN or IKEv2, which are both strong forms of VPN encryption. As on the desktop clients, speeds were fast, which means that this client did great for gaming and streaming in privacy. It's good for unblocking content from all around the world and a kill-switch is available for added security.
Mac client
Hide.me's Mac VPN client is easy to use and nice to look at. And the good news is that it now implements a choice of OpenVPN and SoftEther encryption (for concealing VPN use as regular HTTPS). We found connections to be stable, and we enjoyed using this platform more than Windows.
A kill switch is available on this platform, which means that this VPN is suitable for P2P downloading and other more sensitive tasks. No leaks were detected when using the newest client.
It is worth mentioning that hide.me has got Chrome and Firefox extensions designed to stop WebRTC leaks. However, we discovered no leaks when using the client anyway and it fully supports IPv6 too.

iOS
The iOS VPN client is very similar to the Android client, providing a choice of either OpenVPN or IKEv2 encryption. As mentioned, a kill switch is not available on this platform, but this is standard right across the VPN industry and is not something that we can criticize hide.me for.
The availability of OpenVPN in the iOS client (available since February 2024) is a very rare feature, and we must give Hide.me a lot of credit for adding this robust encryption protocol to its iOS mobile client.
Other Features
- Cross-platform support: hide.me is now compatible with Android TV, Amazon Fire TV Stick, and Amazon Fire Tablet.
- Automatic WiFi protection: This detects if your device automatically connects to an unsecured WiFi network and offers to connect the VPN to protect you. It is great for protecting you from hackers when using public WiFi hotspots.
- SoftEther: hide.me supports the SoftEther VPN protocol, which allows users to disguise VPN encrypted traffic as regular HTTPS over TCP port 443. This makes it difficult for firewalls to block and allows people to evade VPN blocking in countries like China and Iran. SoftEther is supported on Windows only.
- Static IPs: The ability to select a static IP is a pleasant feature that poker players (and some other specialist groups may want to take advantage of). However, these static IPs are shared, not dedicated IPs. This is good for privacy, but not as useful for evading website VPN blocks (which is why even this feature does not work with Netflix US). It is useful for bypassing NAT firewalls, and Universal Plug and Play (UPnP) is fully supported.
The free plan
If you are interested in the free plan, it is an excellent service that is extremely useful. It permits users to download 10GB of data per month, which is much, much better than the vast majority of free VPNs on the market.
With the free plan, users get a choice of the following locations: USA East, USA West, Canada, Netherlands, and Singapore. We think this is excellent considering it doesn't cost a penny!
Previously, free users did not get access to all the VPN protocols. However, hide.me has rectified this now, making all the VPN encryption protocols available.
Connection speeds may be a little slower than the paid version, presumably because of server congestion. On the whole, we can recommend the free version of hide.me, which is hard to rival due to its incredible generosity.
Final thoughts
For Windows and Mac, this VPN really does an outstanding job on the whole. A kill switch is available on both desktops and on Android, meaning hide.me is suitable for torrenting, and permits P2P connections on a choice of servers. The fact that hide.me now allows up to 10 simultaneous connections definitely makes the service better value for money than it was previously.
In our opinion, hide.me is most of interest to consumers who require the rarer VPN features that it provides. If that is you, this VPN certainly has a lot to offer. Hide.me was the first VPN provider that underwent a comprehensive third-party audit. Besides, it has been certified as the most anonymous VPN service in the industry by Leon Juranic, Founder and CEO of DefenseCode Ltd. So, it seems fair to say that hide.me is primarily a privacy-focused VPN – and for people who want those extra privacy and security features, this is definitely a VPN well worth considering.
Live chat support is available 24/7 and most of the time it is excellent. Plus, you do also have the ticket system to rely on if you need to ask a more techy question (and they do have tech guys that seem to be able to help most of the time).
This VPN is lightning-fast, so it is suitable for doing just about anything you can think of online. It even unblocks many of the world's most sought-after streaming services; which is great for users who love to stream content from around the globe. Also, if you need a VPN that has unusual and advanced VPN features, hide.me is a great option.
1 User Reviews
Leave a Review
Thanks for your review!
28 Comments
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

Shadow11