Alternative Choices for You
![]()
From $6.67
Visit Site
Read review
![]()
From $3.69
Visit Site
Read review
![]()
From $2.19
Visit Site
Read review
Swiss-based Proton Technologies AG has now also introduced a Virtual Private Network (VPN) service. Given the deservedly good reputation of Proton Mail, it is not surprising that expectations for Proton VPN are very high. Read on to find out if Proton VPN lives up to these expectations!
Unified Service
Proton VPN now comes as part of Proton's unified privacy ecosystem, which also includes Proton Mail, Proton Calendar, and Proton Drive. Proton's users can now sign in to their Proton Accounts via the new website, proton.me, which acts as a centralized hub for all of Proton's privacy services. Besides receiving full access to all of Proton's services, including Mail, VPN, Calendar, and Drive, proton.me is where users can find all of Proton's privacy resources in one place. All links from protonmail.com now forward to proton.me by default.
This centralization of Proton's services is an attempt to cement itself as a one-stop shop for living your digital life with a measure of privacy. As part of this shakeup, Proton has changed its price plans to make it easier to buy into its unified service with the addition of two new plans, Business and Unlimited.
Price
Proton VPN provides four distinct plans, each of which offers a 50% discount if you purchase an annual subscription (except for the Free VPN plan, of course), or a generous 55% discount if you buy a two-year subscription.
Free Plan
Proton VPN won our Best Free VPN 2024 Award for good reason. Unlike most other "free" VPNs, it provides a largely unlimited service which is so good that many users may feel no need to upgrade to a more premium plan.
The primary limitation is access to only five VPN servers, located in the Netherlands, Japan, Romania, Poland, and the US.
There are no bandwidth or speed limits, although the inevitable increased load on the free servers means that speeds are not as good as when using Proton VPN's premium servers (at least in theory – in practice we found free servers to be almost as fast as the premium ones!).
Free users cannot use this VPN for torrenting. Only one device connection is allowed, but there is nothing to prevent you from signing up for multiple free accounts.
| Proton VPN | ExpressVPN | NordVPN | |
|---|---|---|---|
| Netflix | |||
| iPlayer | |||
| Amazon Prime | |||
| Hulu | |||
| Disney+ |
In the past, it was necessary to verify free accounts with an SMS message sent to your phone, so we are pleased to note that it is now possible to verify accounts using just an email address. And a disposable email address works just fine for this.
Proton Mail Plus
This plan is similar to the free plan in terms of your VPN access, but it does come with a few more email addresses and 15GB of Proton Drive storage space.
Unlimited Plan
This is the primary plan with 10 simultaneous connections and access to all of Proton VPN's features, including Secure Core, Tor over VPN, and additional content-unblocking powers. The full VPN experience from Proton gives you:
• 10 simultaneous connections
• Consistent speeds
• Over 116
servers in 91 countries
across the globe
• NetShield malware and ad-blocker
• Access to worldwide streaming services
• P2P/BitTorrent support
• Secure Core servers
• Tor over VPN
• Strict no-logs policy
• Unlimited volume/bandwidth
• DNS leak prevention
• Kill-switch/always-on VPN
• Encrypted VPN servers
• Router support
• Split tunneling (Android and Windows only)
Visionary Plan
The visionary plan is no longer available to new consumers and is only kept here as a reference. This is the Plus plan with a subscription to the Proton Mail Visionary Plan and an additional five simultaneous connections thrown in. It has to be said that the Visionary Plan does not make strong economic sense for most users when you look at the regular pricing for Proton Mail, so is probably only likely to appeal to businesses and those who wish to support Proton above and beyond the call of duty.
Proton VPN accepts payment via card or PayPal. It is also possible to pay via Bitcoin once have an account. Not so well advertised is the ability to pay in cash or via direct bank transfer if you contact support.
Features
| Simultaneous connections | 10 |
| Server locations | 116 |
| Routers supported | |
| Split-tunneling | |
| Number of countries | 91 |
| Total servers | 4500 |
Proton VPN offers various plans with higher-priced plans providing access to a greater number of features, as shown below:
This is a review of Proton VPN's "Unlimited" plan. This provides full access to all of Proton VPN's mainstream features:
- No logs (see the Privacy and Security section below for full details)
- Up to 10 simultaneous connections
- P2P torrenting allowed on selected servers (including US servers)
- Full access to all 116 servers in over 91 countries
- Full access to Secure Core and onion servers (Unlimited and Visionary plans only)
- Tor over VPN (Unlimited and Visionary plans only)
- Transparency report and warrant canary
- Unblocks US Netflix and many other services (paid plans only)
- Open-source apps
- Alternative routing through third party networks (optional)
All servers used by Proton VPN are bare metal single–tenancy physical servers. To deal with a surge in usage thanks to the COVID-19 crisis, Proton VPN has increased its server capacity. Proton is also donating spare computing resources to Rosetta@home, a project run by the University of Washington that predicts the atomic-scale structure of important coronavirus proteins.
Secure Core
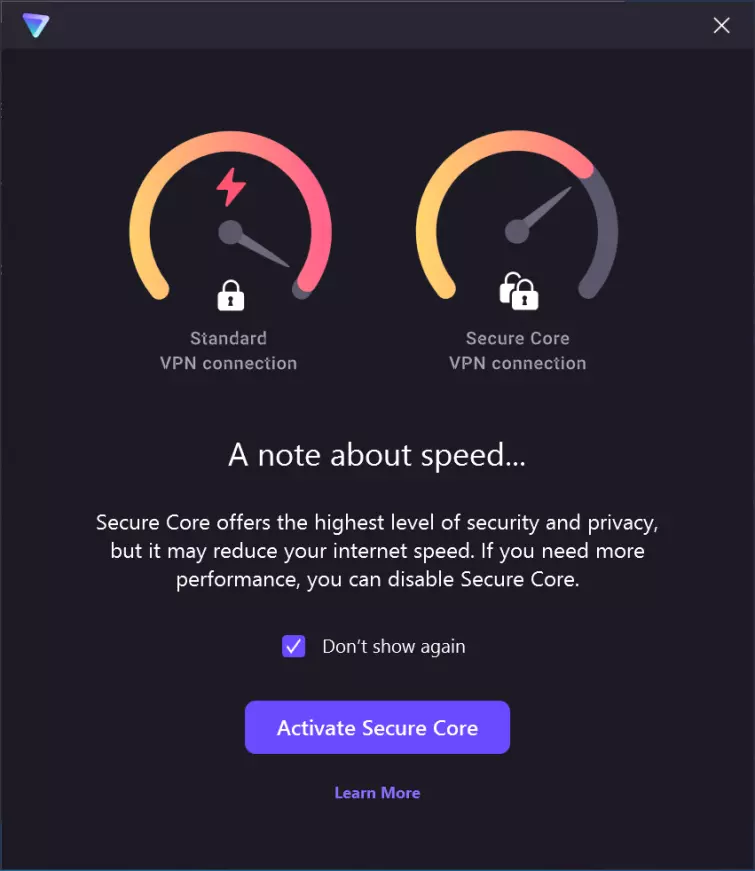
This is a "double-VPN" feature aimed at protecting users from time correlation attacks, which just means monitoring connections as they enter and leave a server in order to correlate them with behavior of interest on the internet.
Such attacks are difficult to pull off anyway, but routing connections through two servers located in different jurisdictions makes an already hard job even harder.
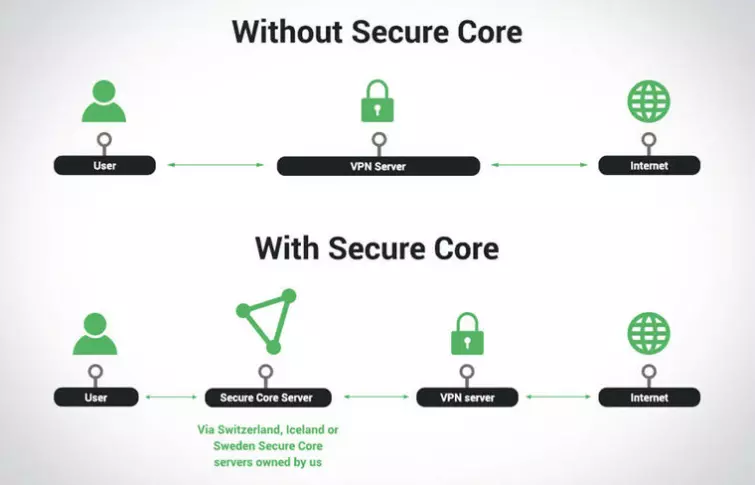
It is still possible to perform traffic analysis on the initial Secure Core server, but Proton VPN has mitigated against this by locating these only in countries with very strong privacy laws and by protecting them with a very high standard of physical security.
Furthermore, "Secure Core servers are connected to the internet using our own dedicated network with IP addresses that are owned and operated by our own Local Internet Registry (LIR)."
Secure Core is undoubtedly unnecessary overkill for the vast majority of VPN users but does provide meaningful extra privacy for those concerned about targeted surveillance from state-level actors.
The mark of a private VPN service is privacy by design, and Secure Core shows that a lot of thought has been put into designing Proton VPN.
Tor over VPN
Proton VPN allows you to connect to Tor (onion) servers through the VPN. In this configuration, you connect first to a VPN server, and then to the Tor network before accessing the internet.
This makes connecting to the Tor network very easy and means you do not need to install the Tor Browser. It prevents your ISP from knowing that you are using Tor, hides your real IP address from the Tor entry node, and allows you to access Tor Hidden services (.onion dark web sites).
It should be noted, though, that a similar effect can be achieved by using the Tor Browser when connected to any VPN service. Indeed, this configuration is more secure than the Tor over VPN setup offered by Proton VPN.
Open-source
All of Proton VPN's apps are fully open source. Proton VPN says that it has been audited by SEC Consult, although as far as we can tell, these audits (or even their summaries) have not been made public, which is a shame.
We are big fans of open source, but a VPN provider can see what you get up to online anyway, so from a security perspective, the main advantage is simply that the code can be checked for flaws by anyone qualified to do so.
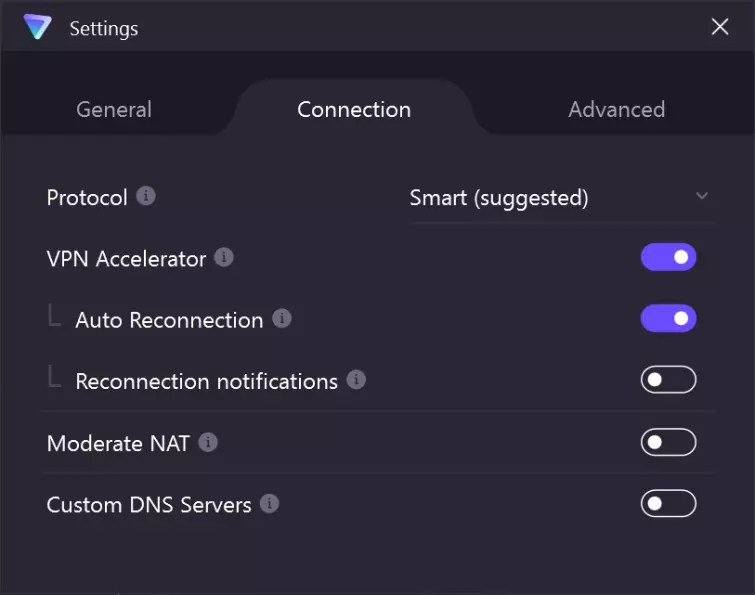
VPN Accelerator
Proton has developed a new feature for improving connection speeds and stability which they're calling VPN Accelerator. They claim this feature improves VPN connection stability and can boost your VPN speeds by up to 400%. VPN Accelerator comes enabled by default and improves your connection speed and quality by performing optimized routing on congested or distant networks.
This is the top end of what's possible and not what your average improvement will actually be like, but we dug into the VPN Accelerator a little more to work out what it's doing.
These improvements don't just come from one single technology, but rather several optimisations performed in parallel. Chief amongst these is rewriting OpenVPN to take advantage of multiple CPU cores when processing packets. Proton also employs advanced networking techniques, a custom Linux networking stack, rewritten VPN protocols, and working across bare metal servers instead of hosted virtual machines to get the most out of your VPN speeds. The further you are from a server, the more likely that VPN Accelerator is going to help you out.
Speed and Performance
Proton VPN
ExpressVPN
NordVPN
ProPrivacy.com SpeedTest (average)
53.4
100
85.9
Speed
490.4
100
568.0
Performance
6
10
9
Reliability
6
9
8
Since our last review, we've been able to gather more data on Proton VPN's average speeds, with the last few months showing an impressive 53.4 Mbps average speed with a maximum burst hitting 490.4 Mbps. This is plenty for data-intensive tasks, streaming, and even online gaming. It certainly holds its own against the top names in the industry, and shows that Proton is continually improving its service.
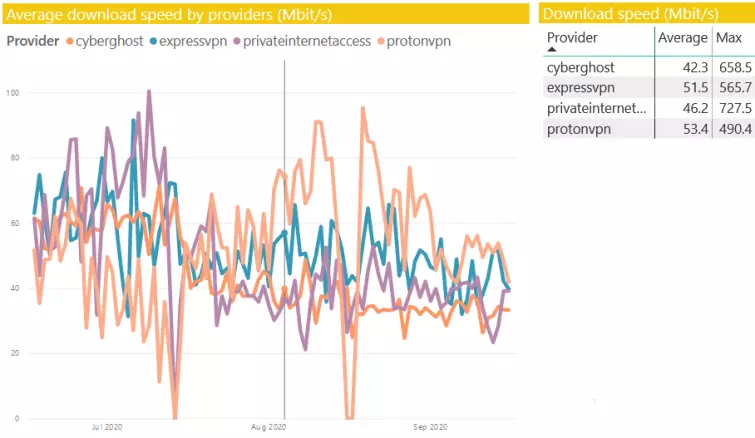
An average DNS lookup time of 0.94 seconds is pretty quick (albeit about half a second slower than some leading VPNs). A 7.2 second connection time is nothing to write home about and will have you twiddling your thumbs when you first turn the VPN on. However, after that, it should be smooth sailing, as Proton operates fast servers. We'll keep monitoring these speeds to see whether it improves over the coming months, as this is the only downside we have discovered.
It's not nearly as scientific as our full speed tests, be we also wanted to get a rough idea about how using the free service and Secure Core affects internet performance. Tests were performed in the UK.
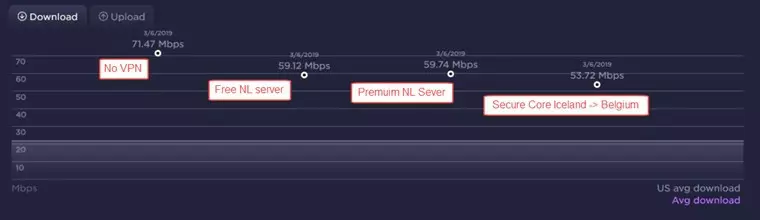
As we can see, the difference between using a free and non-free server in the Netherlands is negligible. Given that our data was being routed to Belgium via Iceland, we are also very impressed at how fast Secure Core is.
We detected no IP leaks of any kind in Windows and macOS, including WebRTC and IPv6 leaks. We cannot currently test IPv6 on mobile devices but detected no IPv4 WebRTC leaks in iOS or Android VPN apps.
Does Proton VPN Unblock Netflix
Proton VPN tells us it's Plus and Visionary plans (only) now unblock Disney+, Netflix (US, UK, and Germany), Amazon Prime Video (US and UK), HBO Now, Hulu, and ESPN. We haven't tested all of these but can confirm that Proton VPN unblocks the US Netflix catalog.
Ease of Use
Custom VPN apps are available for Windows, macOS, Android, and iOS. A command-line Linux script is also available for auto-configuring and controlling OpenVPN (which must be installed separately, along with various other packages). A manual IKEv2 setup guide is also available for Linux.
We are pleased to note that the Proton VPN website and all its apps are now available in English, Dutch, French, Italian, Polish, Spanish, and Portuguese.
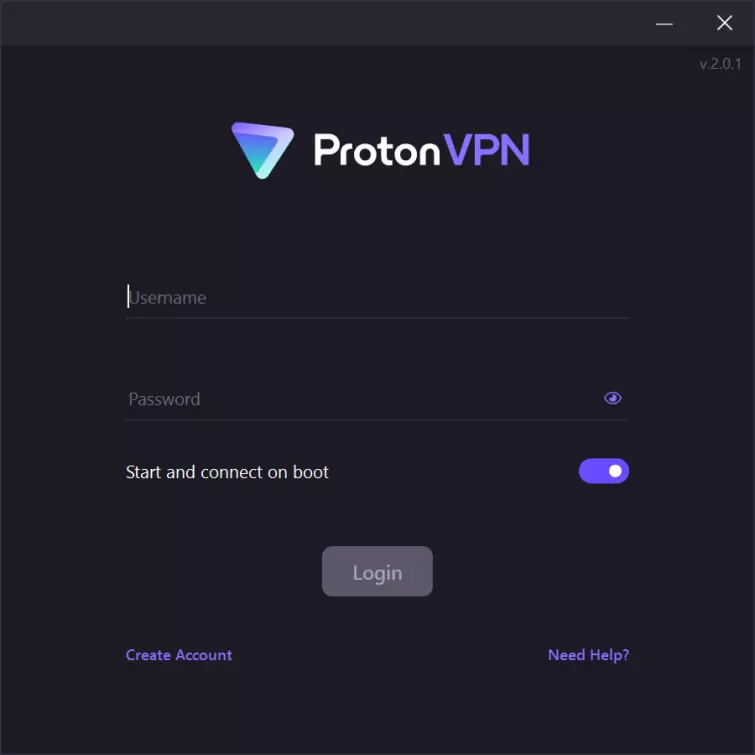
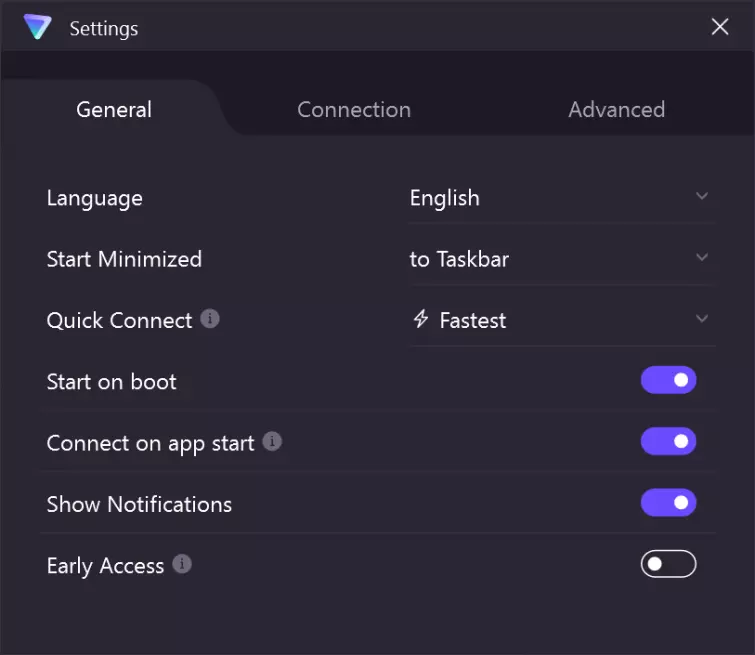
The Proton VPN Windows Client
The Windows version of Proton VPN is easy to install and get started. Once you've downloaded and installed the client, you're presented with a pretty standard login screen. The ability to set the client to automatically start and connect on boot from the login screen is pretty useful and putting it before the login process makes sense – it's most likely the first option you'll want to toggle on once you're in if you're concerned about privacy.
Log in and you're presented with Proton VPN's onboarding process. It's pretty light, giving you a quick idea of the major features of Proton VPN without getting in your way or bogging you down with a long list of technical terms. You can click through or choose to skip the tutorial and get started.
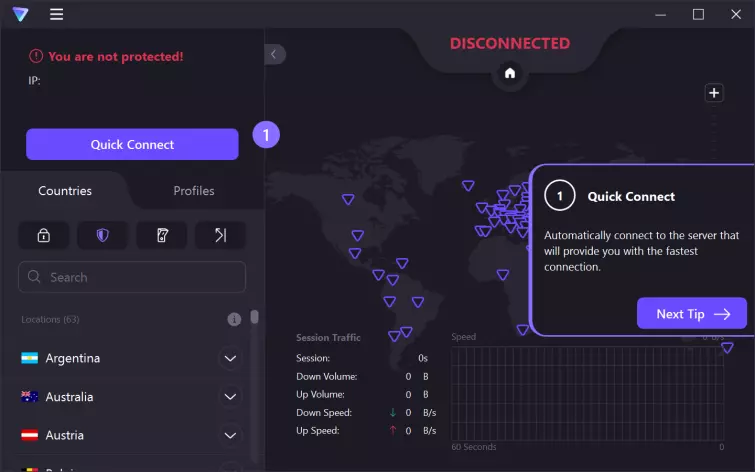
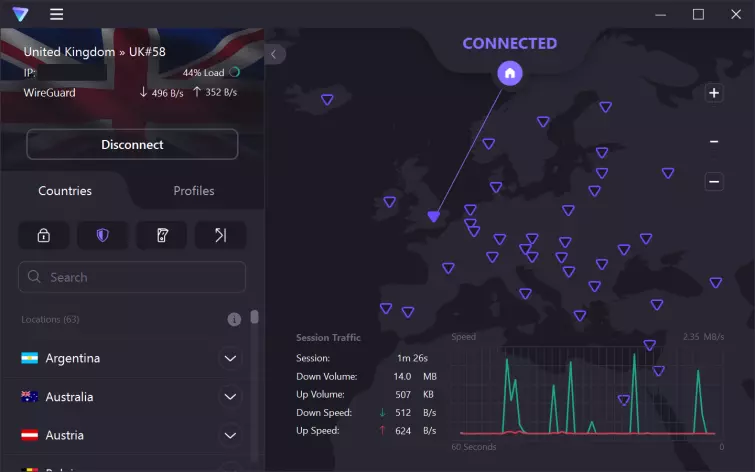
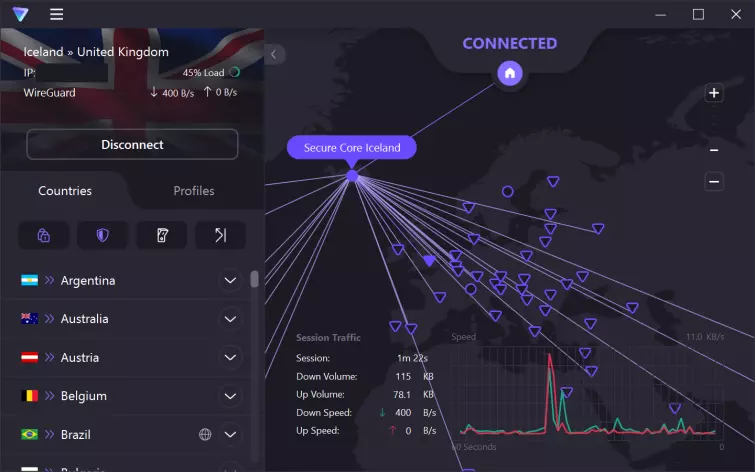
Before we even get into the technical stuff, it should be apparent Proton has put a lot of thought into this slick VPN interface. The world map displayed in the center of the client shows off every location you can connect to. So, if you wish, you can bypass the server list entirely and pick your server based on geography. It definitely feels much cooler doing it this way, but if you need to be slightly more particular about factors like server load, P2P connectivity, and geospoofing, there's also a full server list in the bottom left to browse at your leisure.
The Windows VPN client looks just as smart and provides a ton of useful information. Pick any server to be presented with a light-up icon representing your connection. You also get access to a wealth of information: your current IP, server load, connection protocol, and even a readout of your recent session network usage, all from the VPN dashboard! Proton leaves all this information at your fingertips in a sleek and stylish package that isn't overwhelming.
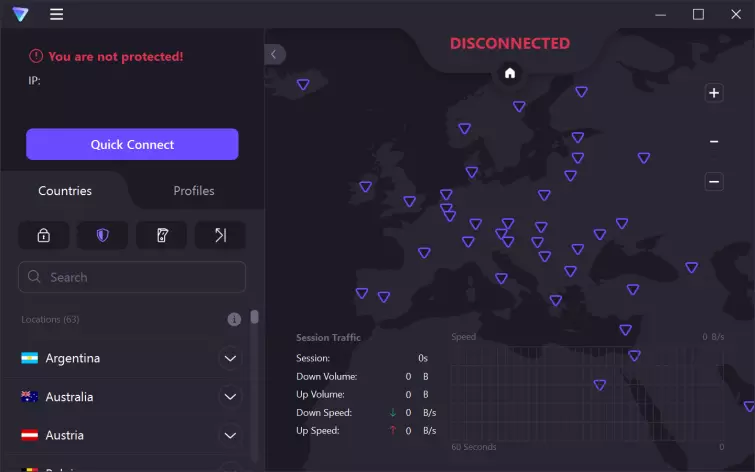
Clicking on the shield icon in the middle of the tab bar gives you access to Secure Core, Proton VPN's multi-hop function that chains your VPN connection through two servers for additional privacy and security. When you're connecting to a Secure Core server for the first time, you're warned that Secure Core will degrade your internet speed. In practice, we found that our connections consistently degraded below the maximums found in our speed test.
Proton VPN currently offers three Secure Core servers which act as intermediary servers, routing your connection to another server which acts as your endpoint. These are Iceland, Sweden, and Switzerland, all known for their strong data laws. The Secure Core servers themselves are hardened against attack and administrated by Proton VPN on location, ensuring that even if your endpoint connection was compromised, an additional layer of security protects you from discovery.

However, users cannot connect to all endpoint servers from each Secure Core server. This is where the server map really shines. You can select a Secure Core location and the server map will visually list every endpoint with a connection to the Secure Core. This makes it much easier to figure out where you want to connect to and how. This feature will only become more useful as Proton adds more Secure Core servers, or additional multi-hop functions.
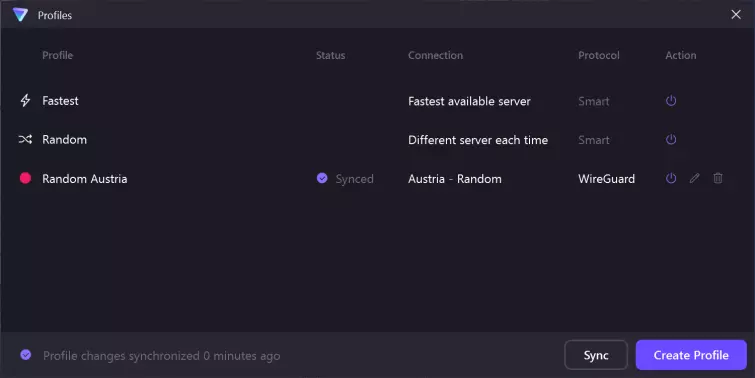
Organization is a strong point of the Proton VPN client, which allows you to pick and customize quick-access VPN profiles based on your current needs. This can be particularly handy if you're swapping between streaming content in different territories. Each profile can be adjusted to pick either a particular server, the fastest, or a random server within a given territory. You can also color-code them for easy access!
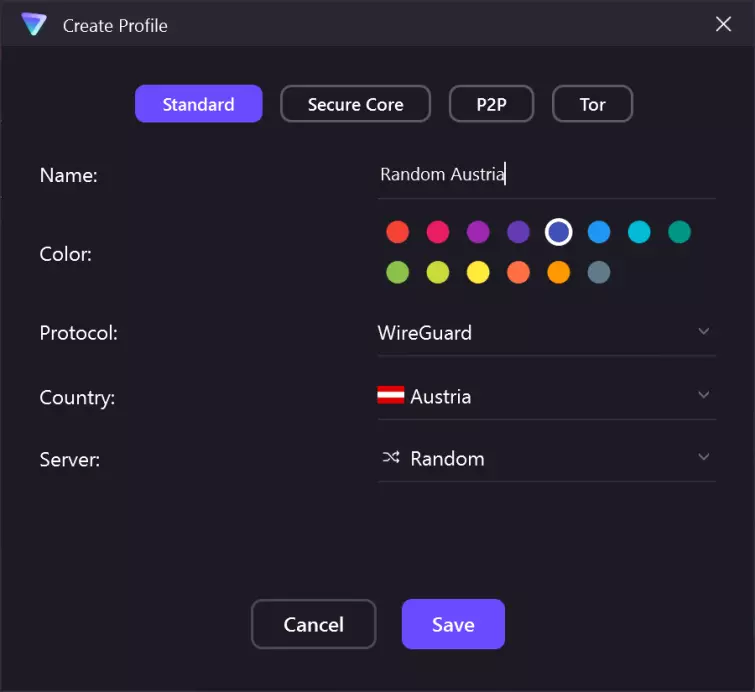
You can see the profile manager gives you a quick readout of each VPN profile you've created, as well as the attributes of the profile and which protocol you use to connect. This tool worked like a charm and made it easy for us to try out various different connections during our testing of the dedicated P2P and Tor over VPN servers.
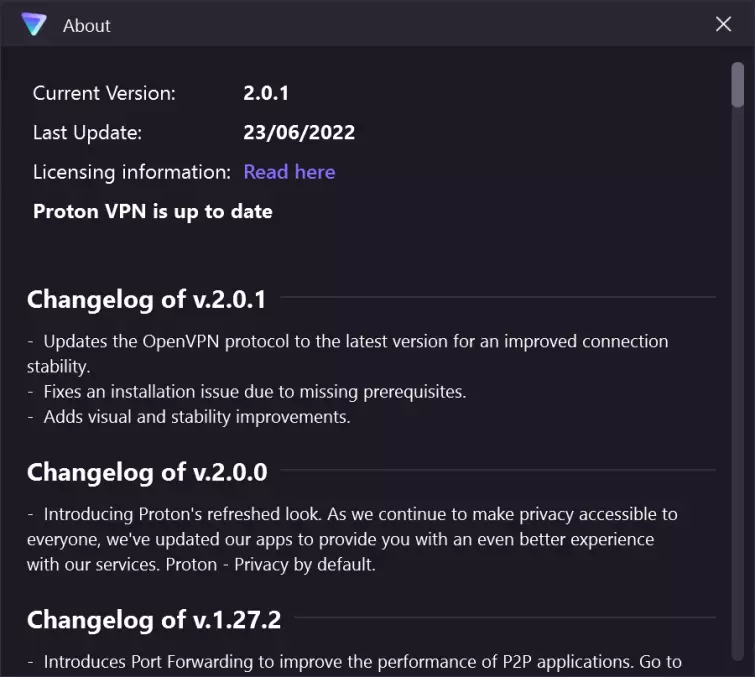
A handy changelog gives you an idea of Proton VPN's progress as a project and highlights the transparent approach Proton VPN is known for. Proton claims they are committed to safety, transparency, and privacy in their company ethos and policy. The open-source nature of the client itself certainly lends credence to that stance, as well as their third-party security audit confirming Proton VPN's no-log status.
Proton VPN comes with all of the features you'd expect from a top-tier VPN. Privacy-conscious users can rest assured Proton VPN has them covered from the moment they boot up, and there's a variety of languages to choose from including English, French, Dutch, Polish, Spanish, German, Italian, Portuguese, Russian, and Persian. There's also the choice to opt into Proton VPN's early access program, which gives you access to cutting-edge beta updates to the client for a sneak-peak at new features being tested.
Proton VPN for Windows supports both the OpenVPN protocol (UDP or TCP) and WireGuard. Generally, OpenVPN is what we recommend to anyone serious about safeguarding their digital security. WireGuard features significantly reduced connection times and is often faster, but the default implementation has fundamental IP logging issues that make it unsuitable for a privacy-focused VPN. Thankfully, Proton implements its own design that fixes these issues.
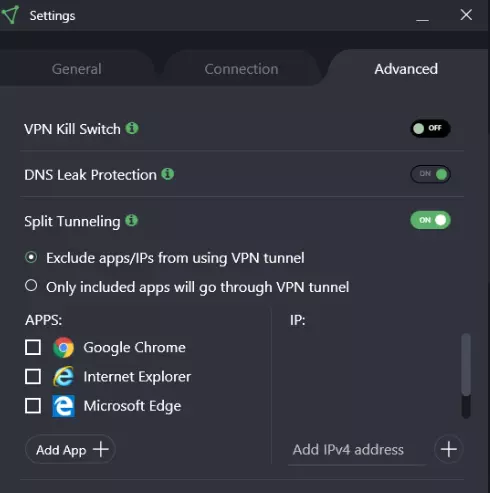
Advanced settings are pretty standard fare. Port forwarding functionality is great if you're a gamer or you're running network services (like a HTTP server) that need to be accessible from the web. DNS leak protection, which is enabled by default, ensures your DNS requests don't leak your IP by using Proton VPN's proprietary DNS servers that don't do any logging. Alternative Routing sidesteps VPN filtering by using alternate routing pathways to direct your traffic to and from your VPN. It's unlikely you'll need Alternative Routing, but if you're finding a provider is blocking your traffic, it might be worth checking out. Both DNS and IPv6 Leak Protection were effective and passed our leak tests. Finally, the split tunneling feature is pretty handy if you want to only put certain programs through your VPN connection and keep others on your home connection.
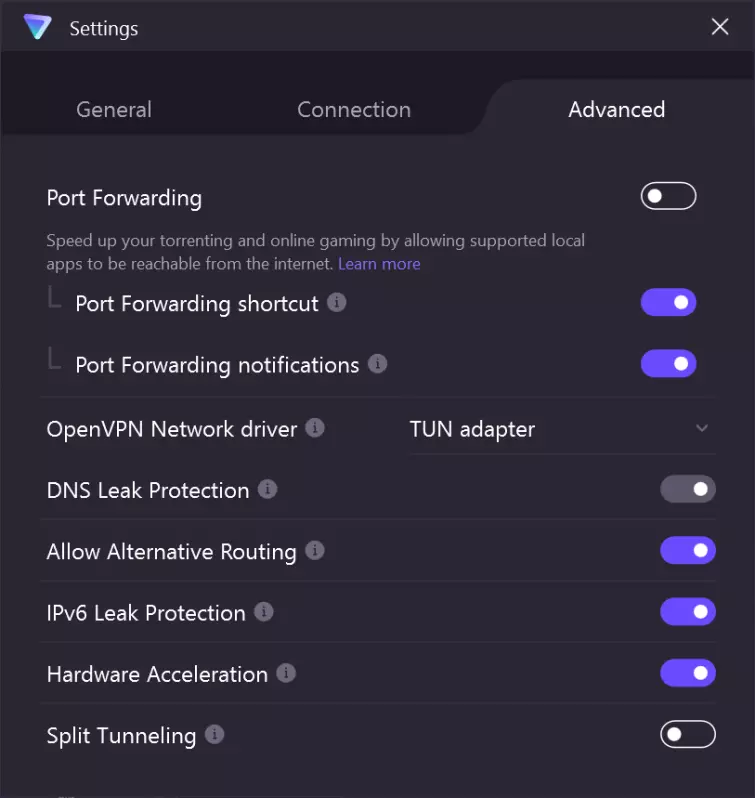
This allows you to decide which apps do or don't use the VPN, and to exclude or include specified IPs. It is worth noting that split tunneling does not work with sites or services that resolve to multiple domains, which includes the likes of Netflix, Amazon, BBC iPlayer, and other popular streaming services. This is a shame, but is an inherent limitation of the technology. This VPN will also enable you to unblock YouTube videos that are restricted within your region,
A new Linux graphical user interface (GUI) client
As of June 22nd, Proton now offers a Linux GUI client. You can even access the GUI on the free Linux plan – making it the best free Linux VPN! The GUI comes with a wealth of features, too:
- Quick connect
- NetShield ad-blocker
- Kill-switch/Permanent kill-switch
- Secure Core
- DNS leak protection
- IPv6 leak protection
- Easy access to P2P torrenting, Tor over VPN, and streaming servers
- Linux desktop integration (via NetworkManager)

Other Platforms
The macOS, iOS, and Android apps use the IKEv2 VPN protocol (with OpenVPN support now available in the MacOS and iOS apps). MacOS and iOS users can also benefit from alternative Routing to iOS and MacOS apps, which lets people connect to our VPN servers over networks that are very difficult to block; alongside Smart Protocol which automatically selects the optimal protocol to provide peak performance and bypass network censorship attempts.
The macOS VPN, Windows, Linux and Android apps all feature a built-in kill-switch for added protection. The iOS app doesn't, but has "Always-on VPN", instead, which re-establishes a dropped VPN connection quickly and automatically.
Customer Service
Proton VPN now offers live chat support to all its paid users, available between 09:00 and 23:59 CEST. This is a super convenient way to overcome VPN challenges, should you encounter any, especially since you get instant answers.
For non-paid users, there's a FAQ-style support page, featuring extensive guides and instructions that we find very useful. Other than that, knowledgeable customer service is available via email. It can take a day or two to respond (less than a day in our experience), but we were nevertheless impressed by the quality of the answers when they arrived.
Privacy and Security
Proton VPN
ExpressVPN
NordVPN
Kill-switch
Obfuscation (stealth)
IPv6 leak protection
WebRTC leak protection
Bare-metal servers?
Self-hosted DNS
Logging Policy
Proton VPN logs a timestamp of the last successful login attempt. This is stored indefinitely but is overwritten each time you log in. By default, IPs are not logged. This logging setup meets our VPN logs criteria, as it poses a minimal threat to users's privacy.
Jurisdiction
Switzerland is generally regarded as a good place to base a privacy company thanks to its strict privacy laws, the fact that it is not subject to EU legislation, and is not a member of the Five Eyes (or even Fourteen Eyes) US-led spying alliance.
On the other hand, Switzerland has passed some alarming new surveillance laws. These require Internet Service Providers (ISPs) and telecom operators to store detailed metadata connection logs for 12 months. What isn't clear (because the wording of the laws themselves isn't clear) is whether these logging requirements apply to email and VPN services.
Proton says it has received assurances from both the Swiss government and its own lawyers that the new laws do not apply to VPN or email services based in the country, but on both counts, it has been unable to provide hard evidence of this.
Protocols and Encryption
Proton VPN
ExpressVPN
NordVPN
PPTP
L2TP/IPSec
SSTP
IKEv2
OpenVPN
Other protocols
-
WireGuard
Catapult Hydra
The Windows client and Linux script use OpenVPN, while the macOS, Android, and iOS VPN apps use IKEv2. OpenVPN is known to be highly secure if properly configured, while IKEv2 is theoretically very secure and is usually faster than OpenVPN. Proton VPN uses the following OpenVPN settings:
Data channel: an AES-256-CBC cipher with HMAC SHA-512 hash authentication.
Control channel: Proton VPN supports a number of cipher suites, the weakest of which is an AES-256 cipher with RSA-2048 handshake encryption and HMAC SHA-1 hash authentication. Perfect forward secrecy is provided by a Diffie-Hellman key exchange (key length unknown).
Even at its weakest settings, this setup is secure. IKEv2 uses an AES-256 cipher with RSA-2048 handshake encryption, which, again, is secure.
Other stuff
As already mentioned, Proton VPN uses only bare metal servers, and none of the software we tested suffered IP leaks of any kind. It is also possible to pay for the service in Bitcoin and even cash.
Obfuscation tech for evading VPN blocks is limited to using OpenVPN TCP (presumably port 443) to disguise VPN traffic as regular HTTPS traffic. This can be quite effective but is defeated using even fairly basic Deep Packet Inspection techniques.
The website uses a number of trackers, including Google Analytics (GA). Proton has told us, however, that GA is not used on sensitive pages.
Proton VPN publishes a transparency report and operates a warrant canary. A transparency report is nice, but still requires trust in Proton to report all incidences. According to Proton Mail's similar transparency report, Proton has complied with a couple of requests for data that weren't backed up with a valid court order. In both cases, the circumstances appear to justify such a decision. It seems that Proton Mail was able to supply very little information, anyway.
We are somewhat dubious about the real value of warrant canaries, but many people find them reassuring.
Final Thoughts
Proton VPN is a fast and secure VPN service with lots of servers, some innovative ideas, and great software. It also shows a strong dedication to privacy, as befits the fearsome reputation Proton Mail has built in this regard.
Our only real criticisms are that we would like to see proper kill-switches in iOS, and that the Visionary plan pricing is quite steep in comparison to its other plans. The iOS kill-switch issue is mitigated to a certain extent by the "Always-on VPN" feature in both apps, and Proton's Plus plan is extremely reasonable. It's a solid service that holds its own against some of the top names in the industry. We'll be keeping a close eye to see how Proton VPN continues to improve its service.
4 User Reviews
Albert
Dead
Leave a Review
Thanks for your review!
39 Comments
replied to .
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

Bruce