Alternative Choices for You
|
|
From $6.67 |
ProPrivacy.com Score
9.6 out of 10
|
Visit Site Read review |
|
|
From $3.69 |
ProPrivacy.com Score
9.4 out of 10
|
Visit Site Read review |
|
|
From $2.19 |
ProPrivacy.com Score
8.6 out of 10
|
Visit Site Read review |
Price
24 months + 3 months FREE
$53.95 billed for the first 27 months12 months
$38.95 billed for the first 12 months1 month
PureVPN is not particularly unusual when it comes to its pricing structure. As with other premium VPNs, it rewards consumers for committing for a longer period of time. However, no matter which subscription plan you decide on, the level of service and features you receive remain the same.
A single-month plan to PureVPN costs $10.95, which is a little on the expensive side. Though, admittedly, it is cheaper than a number of its competitors for a single month. Thus, if you do need a VPN for a short period (for a vacation, for example) – this VPN is not necessarily a bad option.
Things get confusing on the lengthier plans. If you visit PureVPN's website from Google, you will see the following prices advertised:
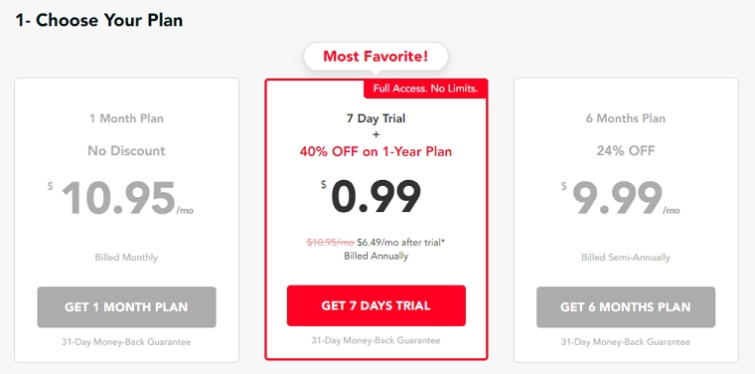
A cost of $9.99 per month on the six-month plan seems extremely expensive. However, it is possible to get the six-month plan for $49.99 (in total) at times too, so it is worth following the link in this article to see if the offer in on.
A one-year plan at a cost of $6.49 per month works out at $78, which, although much more reasonable, is not as cheap as many other providers. As you can see in the screenshot above; a cheaper two-year plan is not available on PureVPN's website by default.
The good news is that PureVPN does have an exclusive offer available via ProPrivacy – that you can access by following the link in this review! Our offer reduces the cost of a single year subscription to just $5.83 per month. A 2-year plan becomes available at a cost of just $2.88 per month. This makes PureVPN much more reasonable! So, be sure to follow the link in this article if you want to avoid the higher prices.
In addition, PureVPN is offering a 7-day trial for $0.99. This gives users an easy way to test the VPN for a week – without initially needing to commit a larger sum of money. We like the option of a cheap trial period, though admittedly some VPNs do provide this kind of trial completely free.
It is also worth noting that PureVPN has a 31-day money-back guarantee (7-days when purchasing a one-month subscription). This allows you to cancel if you do change your mind, which at least prevents you from being instantly locked into a subscription.
Finally, PureVPN accepts payment via credit/debit card, PayPal, AliPay, and CashU. Potentially anonymous payments are possible via gift card or a variety of crypto-currencies – processed by US-based third-party payment provider PaymentWall. However, please bear in mind that payments using anonymous methods are non-refundable.
Finally, it is also worth mentioning that PureVPN also provides optional extras that subscribers can pay for. This includes dedicated IPs and a port forwarding addon. Dedicated IPs are available in the US, the UK, Singapore, Malta, Germany, Australia, Canada, and Hong Kong.
A dedicated IP will cost you an extra $0.99 per month. The port forwarding add on will cost you just $0.20 per month. These are very reasonable prices for these features if you require them. It is also worth noting that PureVPN is the only service that is offering port forwarding as an add on (however, some VPNs do have it as part of their service without having to pay extra).
Features
| Simultaneous connections | 10 |
| Server locations | 96 |
| Routers supported | |
| Split-tunneling | |
| Number of countries | 78 |
| Total servers | 6500 |
PureVPN has both solid state and virtual server locations in its network. These can allow users to gain an IP address in a wider choice of locations, but they can create certain privacy drawbacks (if you aren't 100% certain which real location you are connecting to when the DNS routing trickery occurs).
PureVPN solves this for its users by clearly marking which locations are virtual i.e. do not have a physical server located there, and are instead using Smart DNS routing. For most users, whether they are using a virtual location will be largely irrelevant, but some users may prefer to connect to a guaranteed physical location if they are concerned about individual servers potentially being served a warrant by local authorities.
In locations where physical servers are used, they are all bare metal single-tenancy servers. This is good because bare metal servers are much more secure than software VPS instances hosted on shared servers.
PureVPN WiFi Security
This nifty feature automatically detects when you connect to an unrecognized WiFi network and offers to secure your connection by turning on the VPN. This is a great way to ensure you never surf the internet on an insecure WiFi hotspot without the protection a VPN affords.
Dedicated IP addresses
One of PureVPN's biggest strengths is that it will unblock just about every popular international streaming service available. This includes services such as BBC iPlayer and Netflix US which are known to block IP ranges that belong to VPN companies.
In addition, PureVPN (slightly confusingly) provides two different kinds of dedicated IP address. The first kind is an IP address temporarily created by the service to give users access to a particular event or online streaming service. These IPS are 'dedicated' to that particular event or service – but can be used by any PureVPN user who requires it.
If you want to use a service that appears to have been blocked on PureVPN's standard server options – simply contact PureVPN's 24/7 Live Chat support and an agent should be able to provide you with a 'dedicated' server IP address that works. We, for example, asked for access to Australian TV channel Ten when the Melbourne Open was on, and customer service was instantly able to provide us with a dedicated IP address that worked.
In addition to this kind of temporary “dedicated IP,” PureVPN leases out the more traditional kind of dedicated (static) IP for $1.99 per month. This is a single-user IP address that is unique to your account and only available to you.
These unique personal VPN IPs are good for getting around blocks that target known VPN IP ranges. They are useful for people who run things like games servers – or who want to access LAN resources that require connecting to a fixed static IP address. Or for poker players who want to pretend to be in a different country but require the same fixed, personal-use IP address time and time again.
Advanced port forwarding
Like most modern VPN services, PureVPN servers have a NAT firewall to prevent unsolicited incoming connections. The problem with NAT firewalls is that while they are good for security – they are a drawback if you actually want unsolicited incoming connections to better facilitate file-sharing (like P2P torrent-heads).
Port forwarding solves this problem by allowing users to open holes (ports) in the NAT firewall through which incoming connections can pass. Besides being useful for torrenting, this feature is useful for anyone who wishes to access resources such as printers, LAN drives, and games or media servers that are behind the VPN.
Please see our Ultimate Guide to VPN Port Forwarding for a full discussion on this feature, including potential issues.
It is worth noting, though, that port forwarding does not work if shared IPs (NAT Network) are used.
Other Features
- Apps for all major platforms
- Browser extensions (with added support for the Microsoft Edge browser)
- P2P torrenting permitted
- Kill-switch
- Zero logs (based in Hong Kong)
- Over 2000 servers in 180+ locations
- Split tunneling
- Auto-connect feature
- Smart connect chooses a location based on the subscriber's previous habits
- Port forwarding (optional extra)
- Dedicated IPs (optional extra)
- 10 simultaneous connections
- Built in WiFi hotspot feature
- Support for 7 languages in the Chrome Extension
- New apps currently in Beta (with lower connection times when conecting to VPN servers)
- Coming soon: Wireguard and diskless servers
Does PureVPN unblock Netflix?
| PureVPN | ExpressVPN | NordVPN | |
|---|---|---|---|
| Netflix | |||
| iPlayer | |||
| Amazon Prime | |||
| Hulu | |||
| Disney+ |
In addition to being able to unblock Netflix US and BBC iPlayer services, PureVPN unblocks Amazon Prime, Hulu, and many more sought after international streams.
Thanks to the combination of its standalone VPN apps and browser extensions (as well as the availability of temporary dedicated IP addresses for users who request them) – PureVPN can be considered excellent when it comes to accessing geo-restricted streaming services from around the globe.
In addition, PureVPN will unblock YouTube videos that are restricted in your region.
Below, we have included a list of regional services that PureVPN is known to unblock:
- Disney+ in Canada, Australia, and Germany
- HBO in Australia, the UK, Europe, Canada, and Germany
- Netflix in the US, the UK, Canada, Germany, Australia, Japan, and France
- BBC iPlayer and Channel 4 in the UK
- Zee5, Voot, and MX Player in India
The company is also working on adding more Netflix regions (Turkey, India, Mexico, Brazil, and Sweden) and more international services (Peacock TV in the US, DR TV in Denmark, RTE Player in Ireland, and Tenplay in Australia) to its service. Thus this is a service that is good for streaming and that is actively working to improve its service.
Speed and Performance
| PureVPN | ExpressVPN | NordVPN | |
|---|---|---|---|
| ProPrivacy.com SpeedTest (average) | 66.6 | 100 | 85.9 |
| Speed | 736.6 | 100 | 568.0 |
| Reliability | 7 | 9 | 8 |
| Performance | 7 | 10 | 9 |
At ProPrivacy.com we use our speed testing methodology to provide you with the most accurate VPN speed comparisons available online. We test all the world's leading VPNs regularly using the OpenVPN UDP protocol for consistency. We look for average download speeds and burst (max) speeds across four server locations: the UK, the US and South Africa.
Below you can see the results of PureVPN's speed tests for a three-month period in the summer of 2021.

As you can see, PureVPN is a fast VPN that provides connection speeds that are in a close range with a number of its competitors. Average downloads of 66.6 Mbps make this VPN ideally suited to data intensive tasks such as streaming in HD or gaming. Overall, we consider the speeds recorded by PureVPN in the last few months to be highly impressive, because, as you can see, it is faster than a number of its close competitors.
However, we urge you to take the speed results with a pinch of salt. PureVPN is known to be a service that often yoyos in terms of speeds. In the past few years we have recorded download speed averages ranging from just 9.1 Mbps – to around 29 Mbps.
Thus, PureVPN's current highs might be considered a little unusual. Potentially, PureVPN has improved its infrastructure to provide better speeds to its subscribers, but it is just as possible that we will see another downturn later on. For this reason we would recommend tempering your expectations.
Next, we tested DNS lookup times as these can have a big effect on page load times – and on how the VPN feels in terms of performance.

DNS lookup times were pretty good (though we have seen better, as you can see from ExpressVPN's results). However, the average DNS lookup time for all the VPNs we test is slower than what we registered for PureVPN.
A 0.53 seconds average lookup time (and 2.33 seconds maximum lookup time) is nothing to phone home about, and should mean that pages load pretty quickly.
Leak tests
We ran IP leak tests using our in house leak test system. All tests were performed using a fresh virtual machine with a browser that supports WebRTC installed. We tested using private/incognito mode to prevent any errors due to cache issues.
In Windows, we detected no leaks whatsoever, which is great news. However, the macOS client leaked our IPv6 address via both regular DNS and WebRTC. As a result, anybody using PureVPN on a Mac will need to manually disable IPv6 in macOS to ensure they have reverted back to IPv4.
No WebRTC IPv4 leaks were detected when we disabled IPv6, which means that disabling it will work. However, just to be sure, it is probably advisable to also disable WebRTC in your browser too
No IP leaks were detected when using PureVPN's browser proxy add-ons. However, it is worth noting that the extension's “Prevent WebRTC leak feature” only prevents WebRTC leaks for its own proxy connections. It does not prevent WebRTC leaks when using the VPN (meaning that you must still disable IPv6 on macOS even if you use a browser extension and this feature).
We are currently unable to test for IPv6 leaks in Android but detected no IPv4 leaks of any kind.
ProPrivacy.com SpeedTest (average)
66.6
Speed
736.6
Reliability
7
Performance
7
Ease of use
PureVPN has apps for Windows, macOS, and Android VPN. In addition to regular Android, PureVPN offers custom apps for the Amazon Firestick and Android TV. PureVPN also has browser extensions for Chrome and Firefox, and custom applet for Kodi and DD-WRT. This is an enormous amount of choice.
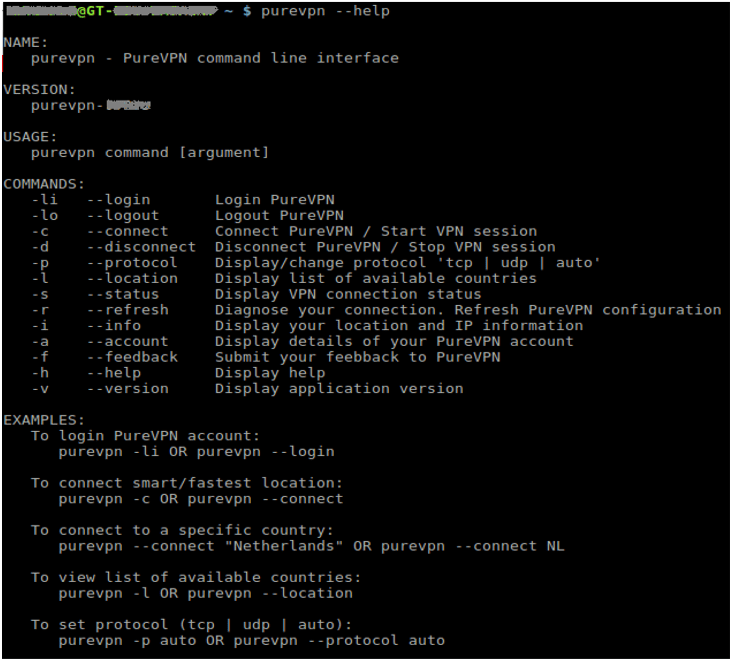
A new OpenVPN Linux app is available, though it is command line only – not GUI. An iPhone VPN is now also available, which is good news for iOS users.
Good manual setup guides are available for a bewildering combination of platforms and VPN protocols. This includes iOS, Linux (many distros) and a variety of routers.
Compatibility
PureVPN
ExpressVPN
NordVPN
Android
iOS
Windows
macOS
Linux
The Windows Client
The Windows client features a rather cute animation while it installs. Once installed it looks smart and is packed with useful features.
It starts by asking you which mode you want to use: stream, internet freedom, security/privacy, etc. PureVPN does not explain in detail what difference each mode makes to your connection settings, so we'll just assume they are correctly optimized for the advertised tasks.
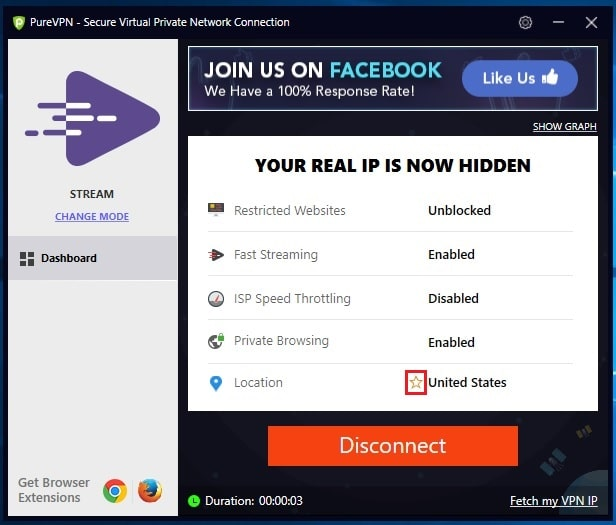
VPN Hotspot uses Windows 10's built-in Hotspot feature to allow other devices to connect through Windows to the internet while benefiting from VPN protection. This definitely cool, but is only available to Windows 10 users and only if you a have WiFi interface that is compatible with the windows Hotspot feature (many aren't).
We are pleased to note that features which were once available to mainstream users are now where they belong – in Beta, and only available to volunteer guinea pigs. This includes split-tunneling and “Gravity” (an ad-blocker and a safe search feature which filters out explicit results from a selection of popular search engines).
By default, the Windows client uses the IKEv2 VPN protocol. This is an increasingly popular choice because although not battle-tested in the way OpenVPN is, IKEv2 is widely considered secure and is undoubtedly faster than OpenVPN.
It is good to see that IPv6 leak protection is now enabled by default, although the firewall-based kill switch is not. This is the better kind of kill switch, as it prevents any traffic entering or exiting your PC outside the VPN tunnel. It also survived a simulated software crash, and so uses system-level Firewall walls. Again, this is good.
Like most VPN services, PureVPN offers shared IP addresses. Unlike most VPN services, this feature is optional. You only gain the privacy benefit of using shared IPs with the NAT network option enabled. Non-NAT-users are assigned a unique IP address.
It is therefore important to note that by default PureVPN's software will select NAT or non-NAT connections based on availability. If you want to use shared IPs then you must specify NAT Network type in the client's advanced settings.
Other Platforms
The Mac app appears identical to the Windows app in almost every way. One thing it doesn't have is IPv6 leak protection, so you will need to disable IPv6 manually in macOS to make it secure.
At present, the Mac client does not support IKEv2. It uses the SSTP VPN protocol by default, but this can be changed to OpenVPN (UDP or TCP). Because it uses the macOS built-in VPN client by default, the VPN will remain in place even if the PureVPN client crashes.
The Android app is extremely feature packed. It offers port forwarding, a kill switch and “secure WiFi.” The VPN protocols supported in the Android app are OpenVPN (UDP or TCP) and IKEv2 – both of which are secure options.
After a few years of promising it, an iOS app is now available for iPads and iPhones. However, please note that it does not have a kill-switch. In addition, it does not provide OpenVPN encryption, instead, it provides IKEv2 with an AES 256 cipher, which is secure and fast.
The command line OpenVPN app for Linux work wells, but is rather basic. Other than coming pre-configured for PureVPN, we can see no advantage to using it over the regular OpenVPN command-line client.
Browser add-ons
Browser proxy add-ons are available for Firefox and Chrome. These are useful for quickly spoofing your location, but provide no security or privacy benefits as proxy connections are not encrypted.
Customer service
| PureVPN | ExpressVPN | NordVPN | |
|---|---|---|---|
| Money-back guarantee | |||
| 24-hour support | |||
| Live chat | |||
| Money-back guarantee length | 31 | 30 | 30 |
| Free trial |
Our Customer Service audit was very favorable on PureVPN. The service has a superb reputation on Trust Pilot, and according to the firm its live chat has a 93% satisfaction rate, which does not surprise us because its live chat is always available and is a superb resource for both subscribers and potential subscribers alike.
Its 24/7 live chat staff are knowledgeable about most things we expect front-line support staff to be knowledgeable about, and were happy to pass on queries about more technical matters to the correct department for an email response later.
These email responses were, in general, fast and answered our questions well. The only issue was that we failed to receive a response to one of our harder questions, but once we pushed on we were able to clarify the matter.
The service also has a selection of articles and guides, FAQs, tutorial videos (including YouTube videos) available on its website. This is a large and varied customer support resource that is definitely great news for subscribers seeking help.
Please Note:
In light of the COVID-19 pandemic sweeping the world, PureVPN announced on March 18, 2021 that it is set to continue providing 24/7 support remotely across its social platforms, live chat, and email.
"For the safety of employees, PureVPN has implemented the policy to work from home. With Coronavirus in full-swing and work from home processes implemented globally, it is more important than ever before to stay connected and provide instant support to our customers. With our customers being the top priority, we want to let you know that here at PureVPN, our Customer Support Heroes are readily available around the clock 24/7 to help you with any issue or query you might have."
Privacy and security
| PureVPN | ExpressVPN | NordVPN | |
|---|---|---|---|
| Money-back guarantee | |||
| 24-hour support | |||
| Live chat | |||
| Money-back guarantee length | 31 | 30 | 30 |
| Free trial |
Jurisdiction
PureVPN is based in Hong Kong, which despite being governed by China enjoys some of the most uncensored internet access in the world. However, the recent implementation of a National Security Law in Hong Kong might put VPN servers and companies at risk, as the situation in the region is becoming much more unstable.
To solve this problem, PureVPN has decided to remove the availability of servers in Hong Kong and China. This means that users are no longer able to get an IP address in those locations. PureVPN explained that:
As PureVPN is a certified No Log VPN service provider and our servers store no personally identifiable information (PII) on the user, we don't perceive any imminent threat from the legislative changes in Hong Kong.
While we don't see any direct threat and we may very well be in the clear, we've decided to remove the Chinese and Hong Kong server locations out of a lack of clarity of the repercussions that this recently enacted National Security Law will have on the integrity of our VPN servers in Hong Kong.
PureVPN has also improved trust in its service by hiring two separate independent security auditors to analyze its infrastructure and no logs claims.
Altius IT and KPMG have both assessed PureVPN's No-Log policy claims and both auditors have concluded that PureVPN does not store any personally identifiable user information on its system.
In addition, KPMG is on an ongoing contract that allows the auditor to reassess PureVPN's systems whenever it wants to within the next 12 months – without prior notice to the VPN company.
This is the first time that a VPN audit has been contracted in such a way that it is impossible for the VPN to clean up its servers and infrastructure in the run up to the audit. We applaud PureVPN for allowing an random spot check of this nature, and we agree that the audit serves to further assure subscribers of the authenticity of its no-log policy.
Logs
VPN providers in Hong Kong are not required to keep any form of logs. Until last year PureVPN kept extensive connection logs anyway, which on one occasion were used to help the FBI to help catch one of its users. This has now changed. PureVPN has updated its privacy policy and is now officially a no logs VPN.
A “bare minimum set of data is required to help you with technical assistance, solving connecting problems, and overcoming region-specific problems, but the IP address you connect from, the IP of the VPN server you connect to, and a timestamp of when you connect are not kept." We very much welcome this move.
Encryption Protocols
| PureVPN | ExpressVPN | NordVPN | |
|---|---|---|---|
| PPTP | |||
| L2TP/IPSec | |||
| SSTP | |||
| IKEv2 | |||
| OpenVPN | |||
| WireGuard | |||
| Catapult Hydra | |||
| Shadowsocks |
On the client, different modes use likely use different protocols, although IKEv2 and SSTP appear to be the defaults. When using OpenVPN, PureVPN uses the following settings:
Data channel: an AES-256-CBC cipher with HMAC SHA1 hash authentication.
Control channel: an AES-256-CBC cipher with RSA-2048 handshake encryption and HMAC SHA384 hash authentication.
Perfect forward secrecy is provided via a Diffie-Hellman (DHE) key exchange, although we don't know the key length for this.
This is a secure setup that matches or exceeds our minimum recommendations in all areas. Please see the VPN Encryption Guide for more details.
Other stuff
As already noted, PureVPN uses only bare metal servers. It does use “virtual locations,” but these are hosted on servers directly under the control of PureVPN and so do not present a security threat. We are also pleased to note that PureVPN now handles all DNS requests using in-house DNS servers for maximum privacy.
Not so good is that the PureVPN website uses a variety of privacy-invading trackers, including Google analytics. These do not affect the privacy of your VPN browsing sessions, however.
All PureVPN apps offer OpenVPN over TCP, which we assume uses port 443 (though we have not been able to clarify this point with PureVPN so it is probably best not to assume that you can use TCP for obfuscation purposes). PureVPN does not offer any other additional VPN obfuscation technologies either.
Final thoughts
In previous years, the primary thing holding back this fully-featured VPN service was the extensive connection logs it kept. Now that it has stopped keeping logs that could potentially compromise users' privacy, PureVPN is pretty easy to recommend.
We consider PureVPN a superb choice for anybody looking to unblock almost anything; whether that be government censored content or geo-restricted streaming services.
Mac users, however, should be careful to disable IPv6 on their systems (and probably also WebRTC in their browsers). Beyond that we saw no problematic leaks, and as mentioned even that problem can be fixed manually, which is good.
Perhaps the only big criticism of this service is in terms of cost. PureVPN is much more costly if you visit the website directly – so be sure to make the most of our exclusive deal by clicking the link in this review. That will ensure that you get a much better price on a 1 year and 2 year plan!
5 User Reviews
Tobias S
John
Leave a Review
Thanks for your review!
141 Comments
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

Jerome T