31 August 2014 is likely to go down in internet history as ‘the Fappening 2014’. To cut a long and very seedy story short, a member of the 4Chan website yesterday released a trove of intimate photos of almost a hundred (almost entirely female) A-list actors, singers and celebrities, including the likes of Jennifer Lawrence, Avril Lavigne, Kim Kardashian, Rihanna, Kirsten Dunst, Aubrey Plaza and Winona Ryder.
As news of the leaked photos spread like wildfire, first to Reddit and then to the wider media, a storm of interest arose. #Fappening continues to trend on Twitter, and the Fappening subedit within hours reached over 40,000 readers (with many men stylishly making crude references to jerking off over the photos).
The resultant media circus has declared outrage at the leak, but by continuing to splash the story over news headlines, has encouraged the public to seek out the photos. We ask our readers to respect the affected women’s privacy, and not to perpetuate sexist behavior or encourage the creep who obtained the photos (and who has promised to release more in return for payment), by resisting any temptation to search for and/or click on these images.
As horror movie actress Mary Elizabeth Winstead noted on Twitter,
‘To those of you looking at photos I took with my husband years ago in the privacy of our home, hope you feel great about yourselves.’
‘Nuff said.
How were the photos obtained?
The original leaker claimed to have obtained the nude photos through an exploit which allowed him (her/them?) to access photos stored on victims’ phones through their Apple iCloud accounts, and media attention has focused mainly on this area (including Apple's Photo Stream utility and iCloud photo backups service).
However, some of the photos are ‘selfies’, and clearly show celebrities using Android devices or webcams to take the photos, and some photos have text overlaid on them that point to their being uploaded using Snapchat (a service with a record of security problems).
Given the huge number of photos featuring such a wide range of celebrities, it has also been suggested that social engineering was used to get close to the targets (perhaps by some form of collective), obtaining positions of trust, such as personal assistants or bodyguards, that would allow access to the stars intimate records. Physical theft of personal phones is also a possibility.
How to prevent this happening to you
Media attention has focused on Apple’s iCloud service, but as noted above this may be somewhat unfair to Apple, and similar services such as Dropbox and Google Drive present comparable security risks anyway. Therefore, while these notes concentrate on iCloud and iDevices, we strongly recommend users of other devices and cloud services take similar precautions.
Use strong passwords
Weak passwords are the single greatest security risk there is on the internet. Not only are passwords such as ‘123456’ and ‘password’ ridiculously common, but in the case of celebrities, where are large amount of personal information about their lives is in the public sphere, it is not difficult for attackers to guess weak passwords based on their family or pets names, where they have lived, their hobbies and interests, etc.
A strong password should contain a long string of random letters and numbers, including symbols and a mix of capital and non-caps letters. Of course, remembering even one such password is next to impossible for us mere mortals, let alone one for each and every important account, so this is where password managers come in.
Password managers randomly generate secure passwords, remember them for you, and integrate with your OS and/or browser to make using them as easy and seamless to use as possible. Although perhaps a little rougher around the edges than commercial offerings such as LastPass and 1Password, we recommend KeePass for iOS and KeePassX for OSX (both fully compatible iterations of the excellent KeePass) because they are free and open source.
Use two-factor authentication
Two factor (or step) authentication (2FA) secures an account by requiring that anyone accessing it needs not just a password and username, but a code sent to their phone, combining ‘something you know’ i.e. your username / password, with ‘something you have’ i.e. your phone.
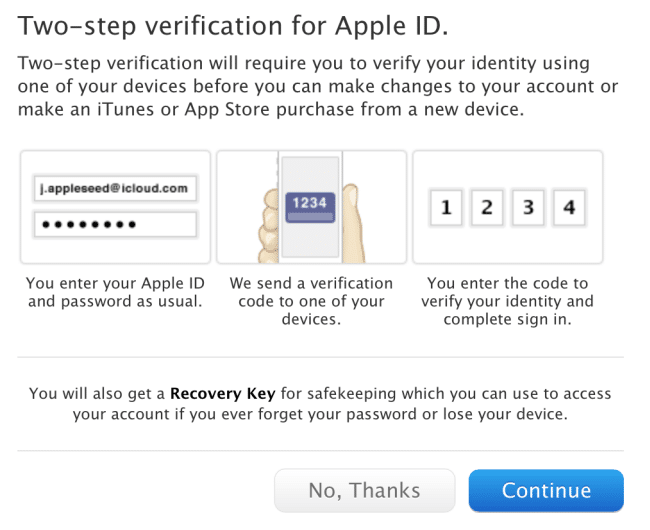
Instructions for turning on 2FA for iCloud are available here, but this feature is also available for similar services such as Dropbox, Google (including Drive) and Microsoft (SkyDrive). A more complete list of services which offer 2FA is available here.
Turn off photo auto-upload
In common with most major cloud storage services, iCloud offers a feature known as Photo Stream, which automatically backs up photos taken on an iPhone or iPad, and uploads them the cloud. This is widely regarded a security weak point (although iCloud does use at least 128-bit AES encryption), and it may be a good idea to turn any such feature off, no matter how useful it is.
Conclusion
It is likely that the celebrities’ accounts were hacked through poor security at the user-end, rather than through a fundamental flaw in technology, and following the simple steps outlined above you can vastly improve the chances of a similar thing never happening to you.
