What is Tor Browser?
Tor Browser is software that allows you to browse the web anonymously.
If you've spent even an average amount of time on the internet, chances are you've heard of Tor Browser. The gossip surrounding Tor is intriguing. That's why many people end up researching how to use Tor. After all, who doesn't want to maximize their security by browsing the internet anonymously? Or investigate something called the "dark web"?
Tor Browser is said to be the gateway to ultimate privacy. As such, we've taken a look at Tor Browser from all angles, to give you a full overview.
Is Tor illegal?
Tor Browser is not illegal. It simply offers the opportunity for anonymous browsing. Thankfully, anonymity is not - and hopefully never will be - illegal.
If your intention is to access websites like Facebook in a more secure setting, you can go forward knowing that using Tor Browser for that purpose is not against the law. If an extra layer of privacy is what you're looking for, Tor Browser is definitely a good option.
That's not to say that every use of Tor Browser is legal. Indeed, many users turn to the infamous onion router in the hope of committing illegal activity without getting caught. That said, Tor Browser is not as anonymous as you might think. If you download the application for illegal purposes, chances are you will get caught.
Is Tor Browser safe?
Overall, Tor Browser is safe. It can give you an extra layer of security during your everyday browsing.
However, it's important to know that Tor Browser has both advantages and disadvantages when it comes to online safety. The application itself is safe to use, but if you're using Tor Browser for something other than normal web browsing, you risk accidentally downloading something malicious.
Tor is a popular gateway to criminal activity. If you want to be as safe as possible while using Tor Browser, you should use it for its intended purpose only: anonymity while browsing.
How do you install Tor Browser?
Installing Tor Browser is easy, even if you aren't familiar with the technicalities.
Windows
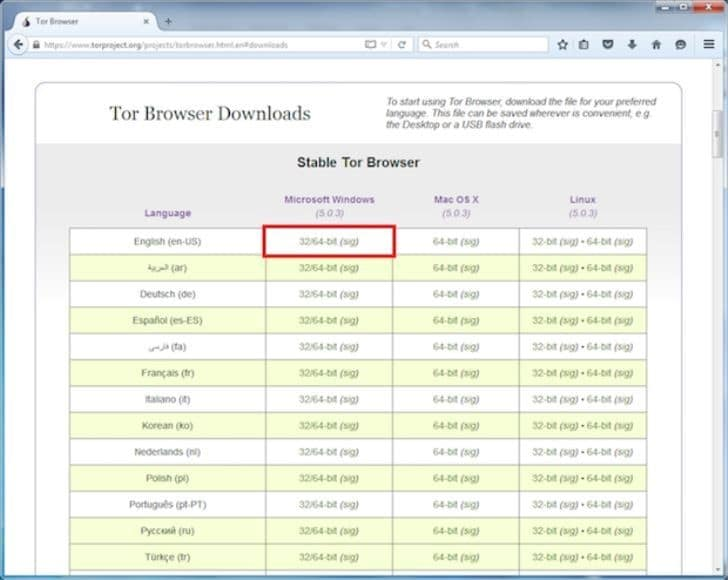
- Navigate to the Tor Browser bundle.
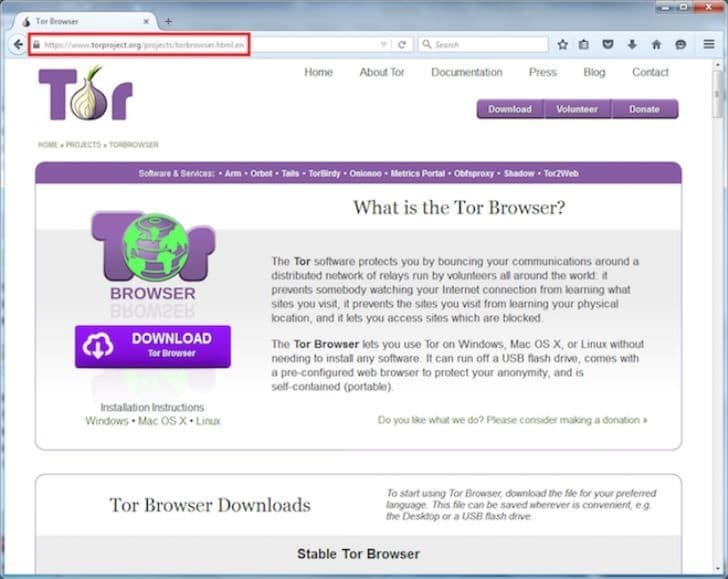
- Find the appropriate download for your system and preferred language.
- Double click on the ".exe" file after it's downloaded.
- A window will pop up; select Run.
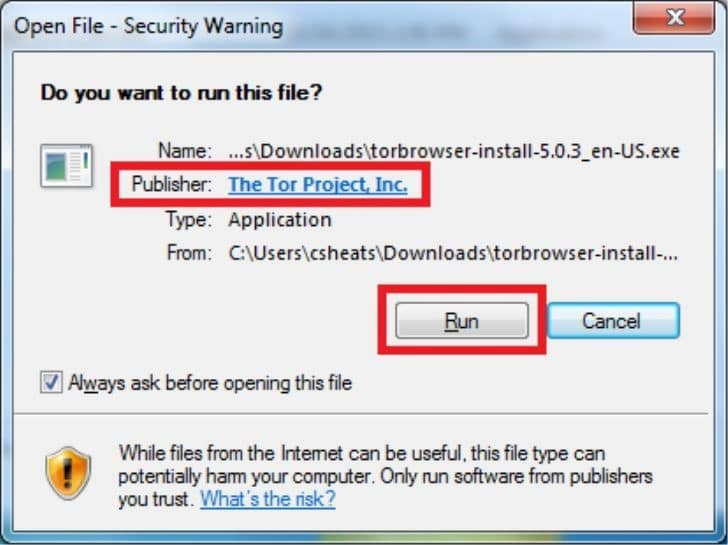
- Follow the installation prompts.
- After the download is complete, select Finish.

- Bam! You're done!
Linux
- Navigate to the Tor Browser bundle.
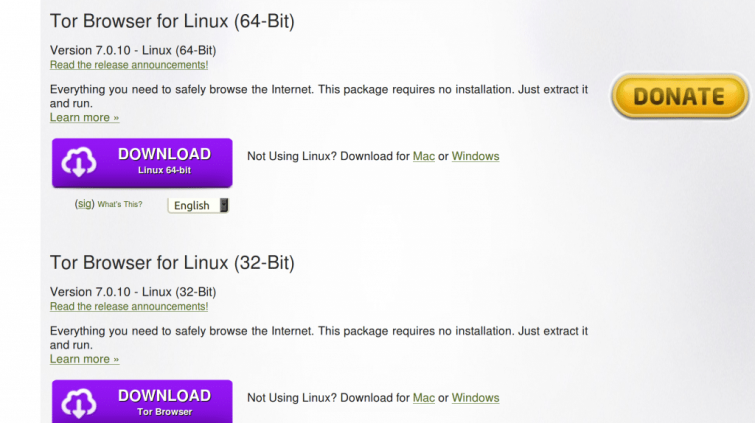
- Find the appropriate download for your system.
- .Save the file to your chosen directory
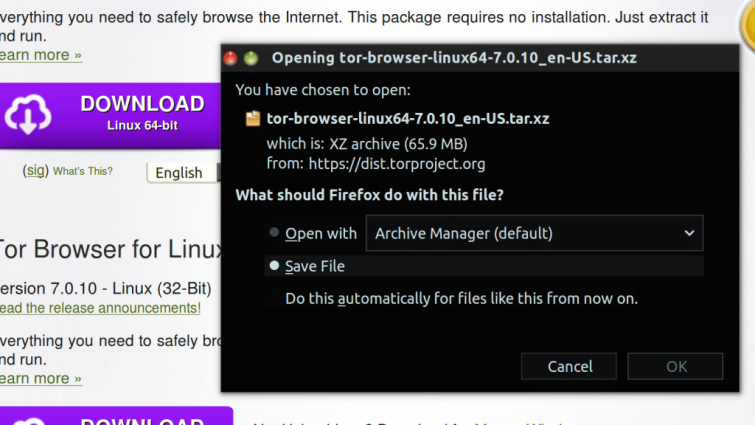
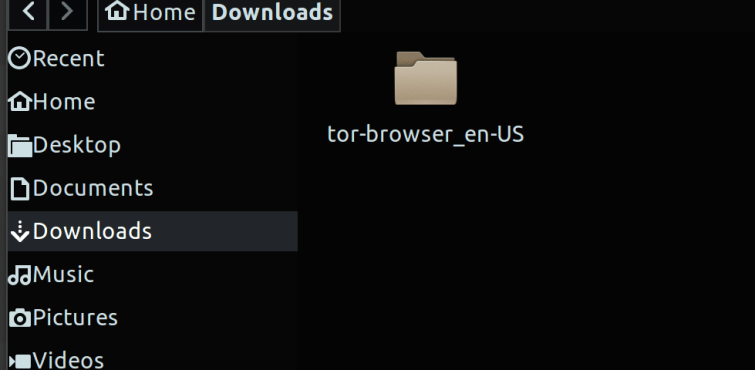
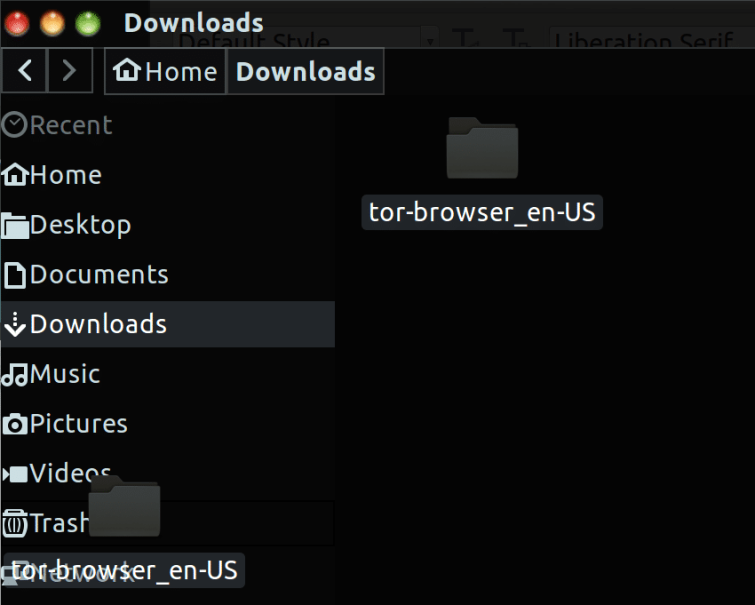
- After the download is finished, navigate to your chosen directory.
- Right-click on the file.
- Select Extract Here.
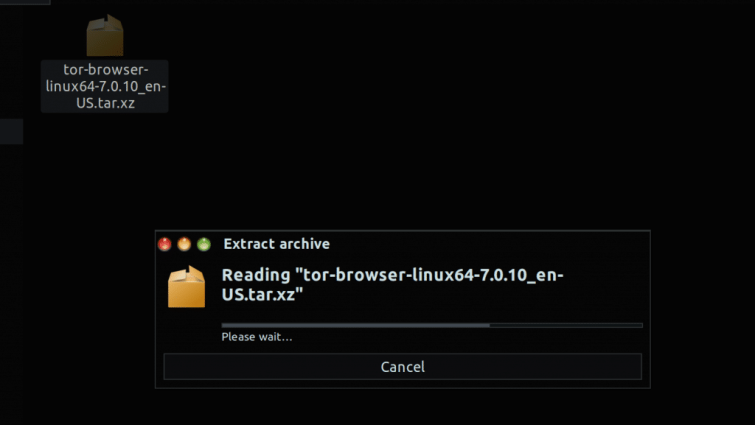
- A folder will appear – click on it.
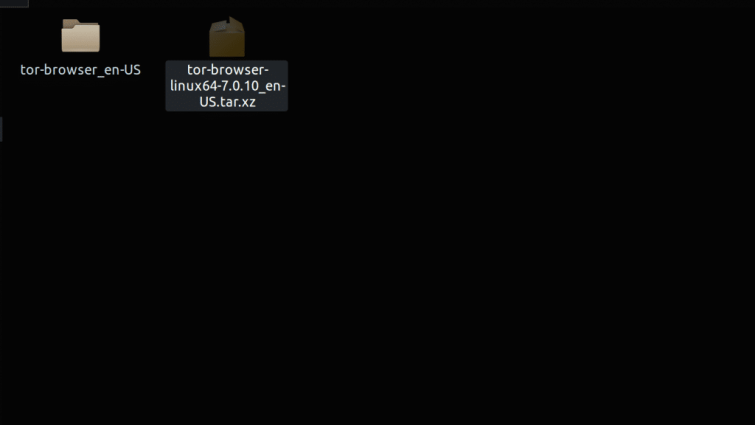
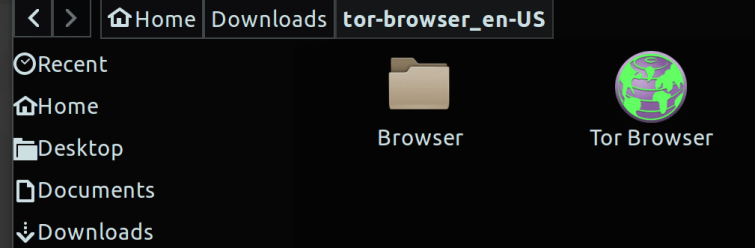
- Double-click on "Tor Browser Setup" and Tor Browser will appear.
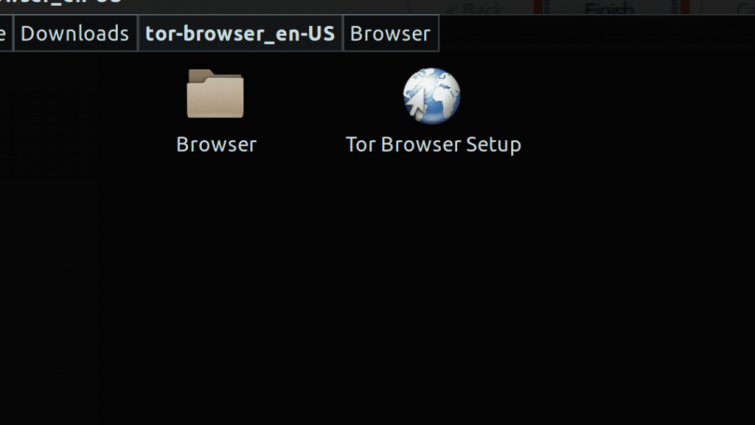
- Bam! You're done!
Mac
- Navigate to the Tor Browser bundle.
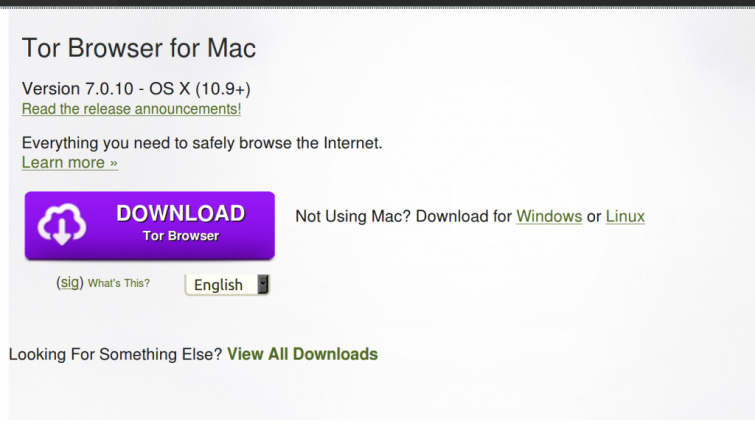
- Find the appropriate download for your system and preferred language.
- When the download is complete, open the directory you saved the file to (the default is the Downloads folder).
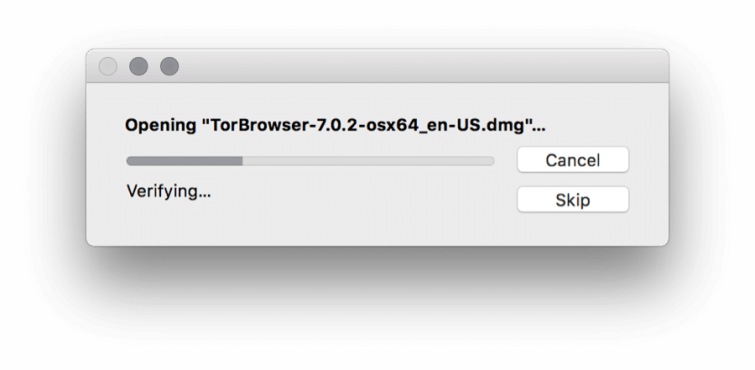
- After navigating there, double click on the appropriate file (most likely: "TorBrowser-7.0.2-osx64_en-US.dmg").
- Your Mac operating system will now verify that the file hasn't been tampered with before opening it.
- A new window will pop up, instructing you to drag Tor Browser to your applications folder. Do as it commands.

- Bam! You're done!
How do you use Tor Browser?
Thankfully, using Tor Browser is easier than installing it.
- Navigate to the directory your Tor Browser folder is saved in.
- Open the folder.
- Click on Tor Browser.
- The configuration wizard will pop up with several options.
- For most users, a direct connection will be just fine.
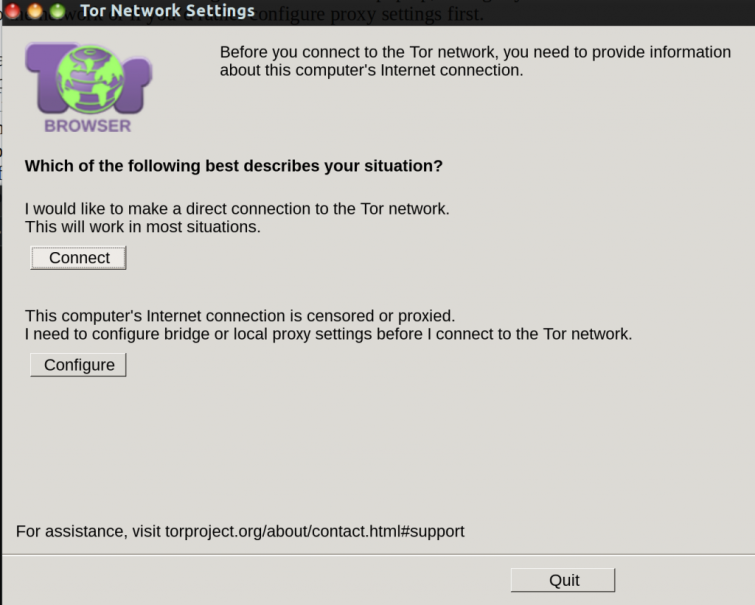
- Select Connect and Tor will establish the connection.
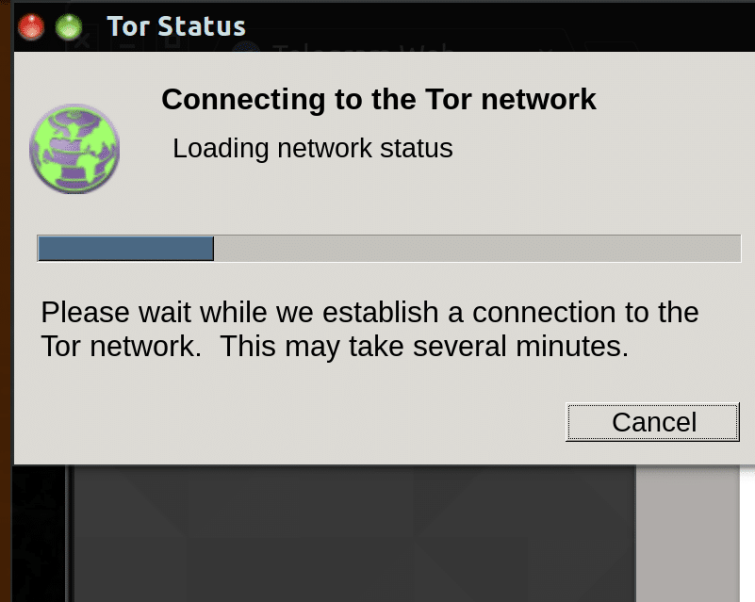
- The Tor Browser homepage will pop up in a new window.

- To double check that the network is working properly, navigate to ipchicken.com.
- Your IP address will automatically appear – does it show your location?

- No? Good! That means you're good to start your anonymous browsing!
How do I Uninstall Tor Browser?
Uninstalling Tor Browser is as easy as deleting its directory/folder from your system.
Tor Browser creates a folder on your system that allows you to use the network whenever you please. This means that if you want to uninstall Tor Browser, you can simply delete the Tor Browser folder or directory (or move it to your trash bin manually). You have now removed it from your computer.
How do I remove Tor from my Mac?
You can uninstall Tor from a Mac manually or with a third-party program. Removing Tor Browser from a Mac isn't as easy as it is for Windows and Linux users.
You can uninstall Tor manually by exiting the browser, finding the application folder, and dragging it into the trash bin. However, because Macs keep the service files of removed programs in a hidden library folder, you still have to remove Tor's service files yourself. To do this:
- Using the Finder, select the Go menu at the top of your screen.
- Select Go to Folder.
- A window will open – enter "~/Library" and select Go.
- Navigate to Tor's leftover subfolders and delete them:
- ~/Library/Application Support/TorBrowser-Data
- ~/Library/Preferences/org.mozilla.tor browser.plis
To be extra safe, double check that there are no Tor leftovers in the following subfolders:
- ~/Library/Caches/…
- ~/Library/Containers/…
The other way to remove Tor from your Mac is with a third-party program. If convenience is what you're looking for, try installing the free App Cleaner & Uninstaller Pro tool. The best part? This tool can be used for any app – not just Tor.
If you're looking for a VPN for Mac, take a look at our best VPN for Mac guide.
Is Tor Browser a VPN?
Tor Browser is not a Virtual Private Network (VPN). For those unfamiliar with how a VPN operates, its purpose is to establish an encrypted and secure connection to a remote server from your computer.
This is exactly why Tor Browser is not a VPN. Tor's main function is to pass your data from one node to another. Every time your data passes through a node, Tor encrypts it and then re-encrypts it.
Can you use Tor with a VPN?
Yes, you can use Tor Browser with a VPN. Tor is centered more towards anonymity and privacy than security and speed. If security and speed are what you're after, you need to use a VPN in addition to Tor.
Is using a VPN worth it? Well, while using a VPN with Tor has some extra benefits, it also has its disadvantages. This is why it's important to find a VPN service that you trust completely.
All that being said, using a VPN is definitely worth it – whether you use it with Tor, or without.
Can you be tracked if you use Tor with a VPN?
Theoretically, no - you can't be tracked if you use Tor with a VPN. However, things are complicated by the fact that your VPN provider has access to your real IP address.
If your VPN provider was to relinquish your right to privacy, your IP address could end up in the hands of government or law officials. Those aren't the only people you have to worry about tracking you, either. If you use Tor for an illegal purpose, you risk exposing yourself to vulnerabilities like powerful scripts or malicious software.
In other words, you can still probably be tracked if you use Tor with a VPN. If you want to avoid trouble and stay anonymous, the key is to not do anything that will make authorities or criminals want to track you.
Is it legal to use Tor Browser in India?
Yes, it is legal to use Tor Browser in India. If you've done research on Tor, you know its purpose is to provide anonymity. Anonymity is legal in almost every country, no matter its level of government surveillance. India might be home to some of the largest surveillance programs in the world, but it is still legal to use Tor there.
However, just like in any other country, it is still illegal for citizens of India to use Tor for criminal activity. If you reside in India and intend to use the internet to commit a crime, not even Tor will protect you or your identity.
Is Tor Browser free?
Yes, Tor Browser is free to use. However, if you're in a giving mood, it does accept donations for use in the future development of its project.
What is the dark web?
The dark web is the non-indexed part of the internet that requires specific software to access. Furthermore, if you want to be truly safe while satisfying your curiosity, you also need to use Tor Browser.
Tor Browser is home to the dark web – or at least part of it. Using the .onion domain, many people download Tor to create their own hidden services. These offer illegal products like drugs, counterfeit items, and even firearms and hitmen.
Tor is designed with anonymity in mind. As such, criminals tend to flock to the service in the hope of doing their dirty work behind the protection of a computer screen.
Of course, some users also explore the dark web simply to satisfy their curiosity.
Is it illegal to use the dark web?
It is not illegal to use the dark web unless you're browsing websites that host illegal content like child pornography or human trafficking.
It is illegal to use the dark web for illegal activity – such as purchasing black market goods. If you do choose to investigate the dark web, the important thing is to stay safe while browsing. You should always use a VPN with Tor in order to avoid as many vulnerabilities as possible.
Can you access the dark web without Tor?
Technically, yes, you can access the dark web without using Tor. If you aren't concerned with privacy or security, a project called Tor2web might be of interest. The project allows you to access Tor's onion domain via reverse proxies.
While Tor2web does offer convenience, it isn't entirely safe. Hopefully a goal you have while browsing the internet is protecting your internet identity and your system from malicious intent. Using Tor2web defeats that goal. Accessing the dark web through a proxy means you're giving the operator of that proxy the opportunity to monitor your web traffic. Will all proxy operators breach your privacy? No, probably not. Is the risk still there? Definitely.
Are there alternatives to Tor?
There are a variety of other networks with similarities to Tor. If you're interested in projects that are similar to Tor, there are a few services you might want to check out, such as Freenet and I2P.
Just remember – although they might share some similarities, they are different from the Tor Project. Still, staying secure is possible if you do your research.
Why is it important to disable JavaScript on Tor Browser?
By disabling JavaScript, you're adding an extra step of security that ensures Tor will work the way it's supposed to. Java is normally used as a "client side scripting language." In other words, its code is written into HTML pages.
This means that JavaScript can be easily abused by users executing malicious scripts into your browser. The entire purpose of Tor is for you to stay anonymous. You can't be anonymous if the creators of those malicious scripts can discover and misuse your identity.
If you're worried about some websites not functioning properly without JavaScript, you can always temporarily re-enable it.
Is it possible to host my own Tor Hidden Service?
Yes, you can host your own Tor Hidden Service with a little bit of work. If you're ready to take on the challenge, you can begin by reading and understanding Tor: Hidden Service Protocol and Configuring Hidden Services for Tor.
Conclusion
Tor Browser is a fantastic way to add an extra layer of protection to your online security. By using Tor to browse the web, you're standing up for your right to online privacy. With intelligence/surveillance organizations popping up across the world, it's important to protect yourself while you still can. Luckily, if you're using Tor Browser, you're already taking the first step in exercising your legal right to privacy.
