Video Review
Find out what we thought of TorGuard in our brief video review, or keep scrolling for a more detailed look at everything the provider offers.
TorGuard Review | ProPrivacy

Alternative Choices for You
|
|
From $6.67 |
ProPrivacy.com Score
9.6 out of 10
|
Visit Site Read review |
|
|
From $3.69 |
ProPrivacy.com Score
9.4 out of 10
|
Visit Site Read review |
|
|
From $2.19 |
ProPrivacy.com Score
8.6 out of 10
|
Visit Site Read review |
Features
Routers supported
Simultaneous connections
8
Server locations
50
Total servers
3000
TorGuard servers are located in 50+ countries. This gives subscribers plenty of choices and allows them to unblock lots of content from around the world. In addition, this means that no matter where users are located, TorGuard will have a server nearby (for achieving optimal connection speeds).
TorGuard allows subscribers to use up to eight simultaneous connections. However, users can purchase more for $1.00 per month (per additional connection to the VPN). This is a useful option for people who own a lot of devices, however, it is worth noting that it is a little on the pricey side considering that a growing number of VPNs are allowing unlimited simultaneous connections.
A kill switch is available on the macOS and Windows platforms, but not the mobile versions of the client. Similarly, Domain Name System (DNS) leak protection is available on Windows and macOS. It can be toggled on and off in the software. OpenVPN encryption is available on all popular platforms, and the VPN has just released WireGuard connections on Windows, macOS, and Linux (and it will be coming to Android and iOS in the near future). WireGuard is an interesting protocol that uses modern cryptographic primitives to provide secure and super-fast connections to TorGuard's VPN servers. This is great news and shows that this provider is still actively developing its platform and staying up-to-date with new developments.
Stealth connections for bypassing firewalls (like the Great Firewall of China) are also available on all of TorGuard’s VPN plans. Furthermore, there is an ad-blocker and malware blocker that can be toggled on and off in the software. All in all, this is a lot of advanced features, which makes TorGuard a great option for just about any VPN user with advanced needs.
P2P
TorGuard permits P2P downloading right across its network. So if torrenting is important to you, TorGuard is perfect (the Tor in the name is there because of its focus on BitTorrenting, as opposed to any affiliation to the Tor Project). For more information, see our best VPN for torrent sites.
Proxy
TorGuard provides a basic proxy service that is now included free with all VPN plans. This option will provide some privacy, but will not come close to offering the level of security that the VPN does. However, it is ideal for unblocking geo-restricted content and P2P file-sharing (for which it is optimized). The proxy service allows subscribers to use Socket Secure (SOCKS5) and Hypertext Transfer Protocol (HTTP)/Secure Sockets Layer (SSL) proxy on up to eight devices. Subscribers can also use the proxy service to access any torrent client.
Anonymous Email Service
For those who want it, TorGuard also has an anonymous email service available in one of four different subscription plans. With prices starting at $6.95 per month.
The good news is that VPN users get a limited free version of the anonymous email service when they sign up for any of TorGuard's VPN plans. That bolted-on plan provides 10mb of offshore email storage and works on any device or operating system. We find this to be a useful extra that is definitely worth taking advantage of.
Paid plans to the anonymous email service come with 30GB encrypted storage with desktop sync apps for Windows, iOS, and Android. G/PGP Email Encryption, Tasks/Notes/Calendar, POP3/IMAP support, File Storage, Email filtering, Address book, and more.
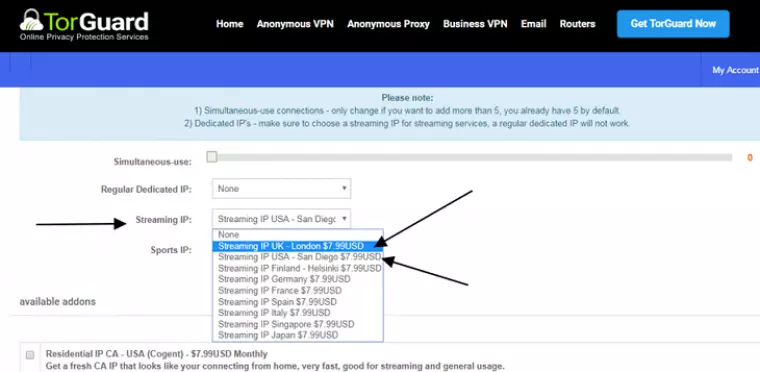
Dedicated IPs for Streaming
For anyone wanting to stream US Netflix, Hulu, BBC iPlayer – and other streaming services – the basic VPN plans will not be enough.
Once you have subscribed, it is necessary to get a Dedicated Streaming IPs plan. The good news is that users can use a discount code (TGLifetime50) to reduce the cost of a yearly subscription with a dedicated IP. Using the code, it is possible to get a year's worth of dedicated streaming IP for just $27.50. However, if you want to pay for a dedicated IP for the UK's iPlayer and for US Netflix, you will need to pay for both, which we consider pretty pricey.
TorGuard also offers a premium 'Residential IP VPN service'. The provider leases legacy residential IP addresses directly from big ISPs in the US and UK, giving the appearance that users are connecting using a standard residential IP address. The provider says this makes it virtually impossible for a website or third party service to determine if a user is tunneling through a known VPN provider.
Speed and Performance
| TorGuard | ExpressVPN | NordVPN | |
|---|---|---|---|
| ProPrivacy.com SpeedTest (average) | 22.6 | 100 | 85.9 |
| Speed | 303.8 | 100 | 568.0 |
| Performance | 10 | 9 | |
| Reliability | 9 | 8 |
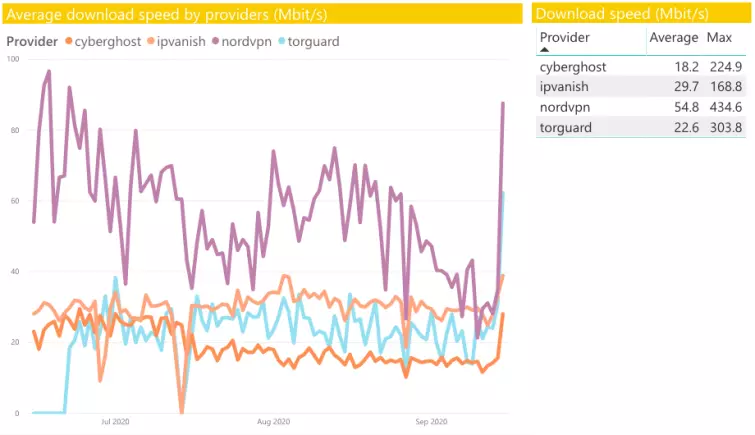
As is always the case, we conducted our speed tests as part of our rigorous testing methodology. The graph below gives you the results, updated regularly – so you always get accurate and up-to-date data. The graph reveals averages across the four server locations we test: Hong Kong, Australia, the UK, and the US.
As shown on the graph, TorGuard performs decently well when compared to other premium VPNs. Download speeds for the time period between June and September 2024 averaged 22.6 Mbps with max burst speeds of 303.8 Mbps. Those speeds are great considering the price for a longer-term subscription and are plenty fast enough for data-intensive tasks like gaming or torrenting.
Leak tests
ProPrivacy.com SpeedTest (average)
22.6
Speed
303.8
We tested TorGuard for IP leaks using ipleak.net. The good news is that we detected no IP leaks, no DNS leaks, and no WebRTC leaks. TorGuard uses its own DNS resolvers by default, which, in our opinion, is always the most secure option to opt for.
However, subscribers can also choose from the following DNS options in TorGuard app settings: Level3, Google, OpenDNS, CloudFlare, Quad9, or TorGuard Ad Blocking DNS. This is a nice addition to the service, that lets people switch their DNS resolver if they prefer.
Price
TorGuard's anonymous VPN service will run you $9.99 when purchased month-by-month. Those prices reduce substantially if you commit for a longer period of time: $19.99 quarterly, $29.99 semi-annually, $59.99 annually, or $99.99 biennially (which works out at just over $4 per month).
We really like the fact that the proxy service is now included free of charge with each VPN subscription, whereas before, it was offered as a standalone service for an additional charge. Now, subscribers get even more value for their money as the proxy service comes free with the VPN.
If you need a little extra than what you get with the standard VPN plans, you can opt for the 'Anonymous VPN Pro' plan, which grants you 12 simultaneous connections, a dedicated IP, the 10Gbit Premium Network addon, along with additional ports for port forwarding. The 'Pro' plans will run you $12.99 monthly, $34.99 quarterly, $69.99 semi-annually, and $119.00 annually.
Like most other services and what is standard in the industry, TorGuard's pricing structure rewards subscribers for committing for longer periods of time.
Subscribers can also opt to pay for a dedicated IP address and port forwarding. These services are pretty expensive: $7.99 per month, $18.99 per quarter, $36.99 per six months, or $54.99 per year. However, users can use the discount code "TGLifetime50" to get their VPN subscription and a dedicated IP for streaming at half price. This will reduce the cost of a yearly VPN with a single dedicated IP to just $57.50 (which is an extremely good price).
Payments are accepted by credit card, Bitcoin, Amazon Pay, gift cards, or a vast number of other online payment methods. TorGuard offers more payment options than just about any other VPN. TorGuard also offers several anonymous crypto payment methods including Monero. They also accept Bitcoin and Litecoin payments through BTCpay (for added privacy compared to BitPay). TorGuard was the very first VPN provider to accept Bitcoin and Litecoin Lightning Network payments in early 2018.
Money-back guarantee
TorGuard provides a seven-day money-back guarantee so that anybody can trial the service risk-free for a full week. However, please remember the guarantee is not available to anyone that pays using Bitcoin or other crypto-currencies.
In addition, TorGuard does not offer a refund to any subscriber who pays for a dedicated IP. These conditions are worth keeping in mind in order to avoid any disappointment.
Ease of Use
Android
iOS
Windows
macOS
Linux
Signing Up
Signing up to TorGuard is nice and easy. To sign up with a credit card, users will need to hand over an email address, full name, billing address, and password. However, people can use false information and bitcoins to pay, thus protecting themselves further with a layer of anonymity at the subscription stage.
Subscribers have a huge amount of payment options: Visa, Amex, Mastercard, Discover, Altcoins, Alipay, CashU, PaySafeCard, Amazon Pay, US gift cards, and Bitcoin (which is by far the best for anonymity). TorGuard sends out an email that explains how to get started once the customer has subscribed.
Once subscribed, consumers can log in to the members' area and download the client that they need. The clients download quickly and install with great ease. Once installed it is just a case of running the software, logging in, selecting your preferred encryption options, and connecting to a server.
The TorGuard Windows VPN Client
Despite being simple and uncluttered, TorGuard's client has all the necessary pro-features you would expect from a top-end VPN service.
A kill switch stops users from leaking data to their Internet Service Provider (ISP) by making all data pass through the VPN tunnel by default (when applied). In addition, there is built-in Web Real-Time Communication (WebRTC), DNS, and Internet Protocol version 6 (IPv6) protection that can all be toggled on and off in settings. What's more, TorGuard has now added Stunnel (obfuscated servers) to its desktop clients (both Windows and Mac)
Subscribers can connect using either Transmission Control Protocol (TCP) or User Datagram Protocol (UDP). UDP is better for streaming as it is faster. Subscribers can select the level of encryption they desire – we suggest that you opt for AES-256 as this is the most secure option (and is now available on all TorGuard servers).
Connecting to TorGuard's servers is extremely easy – just choose a server location and click Connect. The VPN takes around twenty seconds to connect and makes it clear when a connection has been established.
Other Platforms
TorGuard is also available on Android, iOS, macOS, and Linux. It has custom apps for mobile devices and also offers extensions for Chrome and Firefox browsers. TorGuard VPN also sells flashed routers and has guides for flashing DD-WRT and Tomato routers with its software (for connecting with OpenVPN), along with Boxee routers (PPTP only). This is a great addition, and it is nice to see a pre-flashed router on sale.
Android
We downloaded and used the Android platform. Despite the fact that it is a lot more minimal than the Windows software, it did work with no problems. Connection speeds were the same as the ones we encountered on the Windows client. OpenVPN is available from within the client, and users can change the encryption settings and select up to AES 256 with 512 SHA (which is an extremely robust form of encryption).
Unfortunately, there is no kill-switch on Android. But we did not encounter any DNS leaks when using the Android client and TorGuard told us that the client includes DNS leak protection, which is good news and critical for protecting user privacy. Also excellent: TorGuard has added Stunnel (obfuscated servers) to the Android client. This allows people to conceal their VPN use from the ISP and lets them get around Firewalls in countries like China and Iran.
iOS
The iOS app only provides IPsec or IKEv2 encryption. Thus, to connect using OpenVPN, you will need to use the third party OpenVPN Connect App. The good news is that TorGuard has guides to help you get this set up.
Unfortunately, there is no kill-switch on iOS either. However, it implements DNS leak protection.
Linux
TorGuard is one of the only VPN providers that provides a VPN client app with a Graphic User Interface (GUI) for all distros of Linux. This makes TorGuard an excellent option for Linux users.
Other/Free Services
The main extra service available on TorGuard is its anonymous email account. This is available for various costs but comes free with a VPN subscription. The free version gives access to 10mb of encrypted email storage. You can use it on any OS.
Customer Service
Money-back guarantee
24-hour support
Live chat
Money-back guarantee length
7
Free trial
Customer support with TorGuard is handled via live chat and an email ticketing system. Important to note, though, is that the live chat option has been temporarily suspended -- but we're told that it should be back soon.
When available, however, the live chat option is a superb resource that allows both potential subscribers and customers to ask questions and instantly get help with any issues they may be having. The representatives are highly engaging, knowledgeable, and friendly. In addition, they communicate quickly and have all the links they need at their fingertips. The result is that they can quickly advise users on how to solve problems, and can link them to guides to help get the job done.
As previously mentioned, subscribers can also use a ticketing system to ask questions, which TorGuard answers via email. We wanted to ask some highly technical questions about the encryption, so contacted them via the ticket system. We received an answer in under 24 hours from the tech team, who told us everything we needed to know about any recent improvements to the service.
In additional tests of the email ticketing system, asking general softball-type questions, we once received an email reply within a minute, and at another juncture waited two hours to receive a response.
Though knowledgeable, friendly, and truly helpful, overall, we found the responsiveness of the customer support a bit spotty at times. When available, the live chat option is great, but sadly it's not currently an option for the customer, and one can often be left waiting around for a response in its absence. That said, when agents are available, responses via the email ticketing system are indeed nearly instantaneous, it's admittedly just a bit more cumbersome than using live chat.
TorGuard also provides an FAQ section that addresses a range of questions users and prospective customers may have, an extensive knowledge base, a YouTube channel with video guides, as well as a community forum. All of these options combine for a great resource for users to find an answer or get help right away at any time without having to wait for a response from a support agent.
Setup guides and tutorials are available to help people set up everything from flashed routers to OpenVPN using third-party apps. Furthermore, the website has subsections for each different platform, so that users can get access to the guides that apply to them.
Again, the customer support is helpful, but you may have to wait a bit to get a response at times. Because of this, we found TorGuard's claim that it offers 24/7/365 support a bit misleading. Sure, you can browse the knowledge base, forum, and FAQ, and send an email support ticket at any time of the day, any day of the week, but don't expect to have instantaneous access to human support agents at all times via live chat or email...at least for now. Hopefully, TorGuard will resume its 24/7 live chat service soon, and we'll update this review when that happens. But for the time being, users can consult the extensive resources on TorGuard's website at any time for immediate help with most issues.
Privacy and Security
Kill-switch
Obfuscation (stealth)
IPv6 leak protection
WebRTC leak protection
TorGuard is a US registered company. This means that, in theory, the US government could issue warrants and gag orders forcing TorGuard to comply with investigations without informing its subscribers. Sadly, this is true of all US-based firms, which is why the US is considered an iffy place in terms of privacy.
TorGuard's privacy policy states that it keeps no usage or connection logs, which is ideal. A zero-logs policy is excellent. It means that if TorGuard is approached by the government with a warrant; it has nothing much to hand over. The only thing that TorGuard keeps on file is billing information. However, because it is possible to pay with Bitcoins – even this part of the process could be done with a fake name if necessary.
This is what TorGuard has to say about falling under US jurisdiction:
Our legal representation at the moment is comfortable with the current corporate structuring in the US however we wouldn't hesitate to move all assets internationally should the ground shift beneath our feet. All of the main billing infrastructure, authentication servers, and engineering staff are already located internationally.
Encryption Protocols
PPTP
L2TP/IPSec
SSTP
IKEv2
OpenVPN
Other protocols
Shadowsocks, Stunnel, SSH tunneling, OpenConnect/AnyConnect, SSL Proxy
All platforms can connect to TorGuard using OpenVPN (our recommended protocol). However, OpenVPN is only native in Windows and macOS. On iOS, Internet Protocol Security (IPsec) and Internet Key Exchange version 2 (IKeV2) are provided by default, and you have to install OpenVPN Connect to use OpenVPN. On Android, it is necessary to use third-party OpenVPN software (available on Google Play Store). Although this is a bit of a pain, the reality is that third-party OpenVPN software is free, secure, and very easy to install.
Subscribers also get to choose between Point-to-Point Tunneling Protocol (PPTP) and Layer 2 Tunneling Protocol (L2TP) if they wish to (by connecting with Viscosity). However, we would recommend that you stay away from PPTP as it is not secure anymore – so the official client with built-in OpenVPN is perfect. What we really love about this service is that subscribers can choose between a lot of different OpenVPN encryption strengths.
It's nice to see that TorGuard has also recently begun offering WireGuard, the next-generation VPN protocol that promises to afford users faster connection speeds with even tighter security than other VPN protocols. TorGuard currently offers the WireGuard protocol on Windows, macOS, and Linux platforms, with support for mobile platforms in the works.
TorGuard also provides the option of enabling a “stealth proxy” (found in TG lite app > more settings > proxy > TorGuard Stealth Proxy). Users can select from five Japanese or five US servers, which are connected to via an encrypted SOCKS5 proxy tunnel. This adds a second layer of AES-256 (Advanced Encryption Standard) encryption. This option is great for people wanting to bypass firewalls like the Great Firewall of China.
This is what TorGuard has to say about offering various levels of encryption on the platform:
When you say there are known vulnerabilities to BF – CBC, one might assume that it is completely broken. This is not the case (yet), and if there was any supporting evidence of this we would remove the option from our software. By adding multiple encryption options to ALL OpenVPN servers (BF CBC, AES128, AES 256), this will allow the user to make their own choice on connection security.
The VPN.ac scandal
A few years ago, VPN.ac accused TorGuard of stealing its code. Although some people might not necessarily see this as much of a problem, the issue (according to VPN.ac) was that TorGuard had not copied the code correctly and had left consumers with security vulnerabilities. TorGuard denied that it had done anything wrong on purpose, claiming that a third-party developer had passed the issue on to it.
According to TorGuard, the problem was fixed very quickly and the TorGuard platform has been completely secure since the vulnerability was patched up. In addition, TorGuard now runs all of its servers. Thus, there is nothing for subscribers to worry about when using TorGuard's clients.
Final Thoughts
TorGuard's OpenVPN encryption options are formidable. Subscribers get a service that provides some of the highest levels of encryption on the market, with the option to bypass strong encryption in favor of faster speeds for tasks that don't require as much privacy. This gives consumers considerably more choice in the matter than many other providers offer, allowing them to use the service in different ways depending on their needs at different times, which is fantastic.
Speeds fared quite well even on the strongest encryption settings, and the zero-logs privacy policy speaks for itself. So you don't necessarily need to sacrifice your privacy to get great speeds with TorGuard. A choice of servers in 50+ countries rounds off the service nicely. This VPN has excellent support agents, superb guides, and it sells a flashed router (as well as offering helpful guides for setting up flashed routers). In addition, it provides a 7-day money-back guarantee so you can test the service for a week risk-free.
Although it is slightly pricey for a one-month subscription, it is in line with the top-end of the VPN market, and prices are much more reasonable when you opt for a longer-term subscription plan. Overall, TorGuard is an impressive VPN service that is exceptional when it comes to privacy and security.
0 User Reviews
Leave a Review
Thanks for your review!
62 Comments
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

Anon91
Anon29048
Pat
Johanna Ruth