Features
TunnelBear might not have a dazzling array of features for prospective subscribers to consider, but the tools the provider does offer are well implemented and fundamental must-haves for any VPN. All in all, they make up a solid service that clearly values your security as much as you do.
Simultaneous connections
N/A
Routers supported
Split-tunneling
Number of countries
47
Total servers
1000
TunnelBear Servers
It's not the largest VPN network out there, but TunnelBear provides access to servers in 23 countries, allowing users to pretend to be in any of these locations to bypass geo-restrictions and locally-enforced censorship. So long as you're paying for TunnelBear's premium plan, you'll be able to take your pick of the 23 locations. It is worth bearing in mind that customers on the free plan won't be able to access the Australian server, however.
TunnelBear is compatible with Windows, Mac, Android, and iOS devices, as well as VPN-friendly routers. VPN Browser extensions for Chrome, Firefox, and Opera are also available. Because TunnelBear's premium account permits five simultaneous connections, you'll be able to secure most of your gadgets with a single subscription.
VigilantBear (Kill-switch)
VigilantBear is TunnelBear's kill-switch feature. Ultimately, it prevents unencrypted data leaking to your ISP in the event your VPN connection drops. VigilantBear will keep your info secure whilst your VPN automatically reconnects to the network, and is available to Windows, Mac, and Android users. Keep reading for a more in-depth look at TunnelBear's other security measures, by the way.
Peer-to-peer (P2P)
TunnelBear is based in Canada, which once meant that the service was a no-go when it came to torrenting. Thankfully, TunnelBear has changed its official stance, and now states that you can use their VPN for P2P downloading and for accessing Tor.
This change of heart came with a much-needed reassurance that the provider is staunchly no-logs, making time-correlation attacks a thing of the past. It also means that TunnelBear has no user data to hand over to the Canadian authorities should they come knocking.
GhostBear
TunnelBear also boasts its very own obfuscation tech (sometimes also referred to as "stealth mode"). GhostBear conceals OpenVPN traffic from your ISP in order to bypass VPN firewalls. This feature is particularly handy in places where internet access is heavily restricted – like China, Iran, and the UAE. By implementing a choice of TCP over port 443 or by using obfsproxy (users have the option of either), GhostBear makes it harder for an ISP to detect VPN usage, as it'll look like regular HTTPS traffic.
You won't be massively insecure if you're not using GhostBear – in fact, TunnelBear itself recommends that you not use the feature unless you truly need to disguise your VPN usage or have trouble connecting to the servers in the first place. When using GhostBear, it's also normal to notice a slight reduction in speed. The feature has to go to extra lengths to conceal your VPN usage, which, unfortunately, takes a toll on the quickness of your connection – though that's a small price to pay in exchange for online freedom of speech. GhostBear is currently available on Windows, Mac, and Android apps, though iOS users will have to go without due to restrictions in the iOS design.
SplitBear
As the name suggests, SplitBear is TunnelBear's split tunneling feature. With it, you'll be able to control which apps are routed through the VPN and which remain unencrypted, routed through your regular ISP. You may need certain sites to identify your original IP address (think work infrastructures or local streaming services), and with SplitBear you'll be able to run through a list of applications you can have TunnelBear bypass. It's simply a matter of toggling SplitBear on! At the moment, however, SplitBear is only available on Android devices.
Fastest Tunnel
This neat little feature will be of particular use to VPN newbies, who might be overwhelmed by TunnelBear's available selection of servers. Fastest Tunnel automatically selects a server for you based on proximity, meaning your data travels a shorter distance and you get the quickest connection speeds possible. Of course, if you want to access geo-restricted sites or check out streaming content from overseas, you might need to manually select a server, but otherwise, Fastest Tunnel does the hard work for you. This tool is compatible with Windows, Mac, Android, and iOS devices.
TCP Override
If you’re experiencing sluggish speeds when using TunnelBear servers, or entirely broken connections, toggling on the TCP Override could make all the difference. When enabled, the VPN will utilize TCP protocols instead of UDP. The TCP protocol is slower, but generally more reliable. TunnelBear does warn that if you’re using the TCP Override and not experiencing any improvement in speed, then you probably don’t need it – so some trial and error may be required!
If you want more information about this topic, check out our TCP vs UDP article.
Does TunnelBear unblock Netflix?
Simply put – no. TunnelBear cannot unblock Netflix regions including US, UK, or even BBC iPlayer. The VPN is speedy enough to stream content from your local providers without buffering hiccups, but TunnelBear has explicitly stated that it doesn't allow access to geo-blocked content. This is pretty disappointing considering the price of the VPN. If you look elsewhere, though, you can find VPNs for Netflix (and other streaming services) for a comparable cost.
Pricing and plans
TunnelBear has three different subscription options on the table: a 1-month plan, 1-year and 3-yearly plans, as well as an exclusive 2-yearly plan for ProPrivacy readers. There's also a free VPN plan available if you're more interested in trying before you buy, and you'll be granted 500 MB of free data each month. Free users have access to all servers... aside from the Australian one.
The paid plans can be bought for monthly or yearly use. The monthly plan will set you back $9.99 each month, and it's recurring, so you'll need to cancel it yourself.
You can bag some colossal savings if you're willing to pay right away. The 1-year plan works out to around $4.99 a month, billed $59.88 per year for a saving of 67%. The ProPrivacy exclusive plan equates to $4.17 per month, or $99.99 for both years. Similarly, you can save a huge 67% with the 3-yearly plan, which'll cost you $3.33 a month, or $120 upfront.
Sadly, TunnelBear has dropped its 30-day money-back guarantee. The service now opts for non-refundable purchases, though select circumstances might very well be refunded if you reach out to the Support Bears. We'd recommend making use of TunnelBear's free tier before committing to a lengthy subscription.
Customers can pay for their plan via credit or debit card, including American Express. TunnelBear is very specific about how it handles payment info in its privacy policy, operating exclusively with PCI compliant payment processors. Unfortunately, PayPal is not accepted by TunnelBear at this moment in time. On a happier note, however, you will be able to use Bitcoin to purchase a subscription if you so wish.
Speed and performance
| TunnelBear | ExpressVPN | NordVPN | |
|---|---|---|---|
| ProPrivacy.com SpeedTest (average) | 50.6 | 100 | 85.9 |
| Speed | 385 | 100 | 568.0 |
| Reliability | 6 | 9 | 8 |
| Performance | 6 | 10 | 9 |
We use our rigorous testing methodology to measure TunnelBear's connection speeds. if you'd like to learn more about how this test works, check out our how we conduct speed test article.
During our tests, we found that TunnelBear provided impressive connection speeds. The VPN is more than quick enough to handle HD streaming and other data-intensive tasks, like online gaming and VoIP calls.
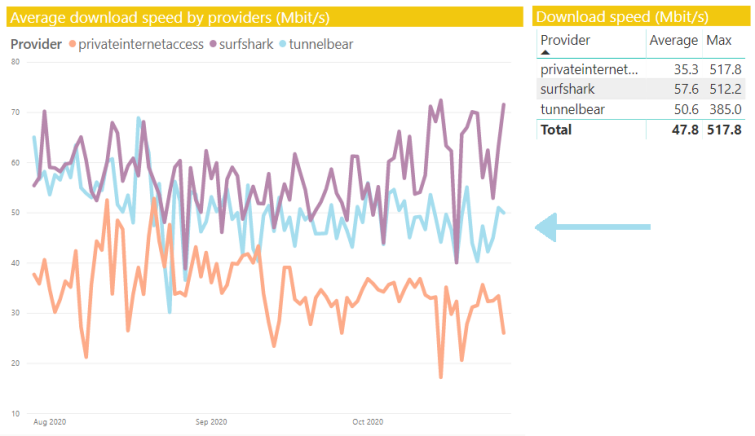
Over these three months, TunnelBear clocked in with an average download speed of 50.6 Mbit/s, and a max speed of 385 Mbit/s. These results are excellent and definitely mark TunnelBear as one of the fastest VPNs on the market. So, whilst a handful of other providers will be quicker, you certainly won't feel like your internet is moving at a snail's pace with a TunnelBear subscription.
Leak tests
ProPrivacy.com SpeedTest (average)
50.6
Speed
385
Reliability
6
Performance
6
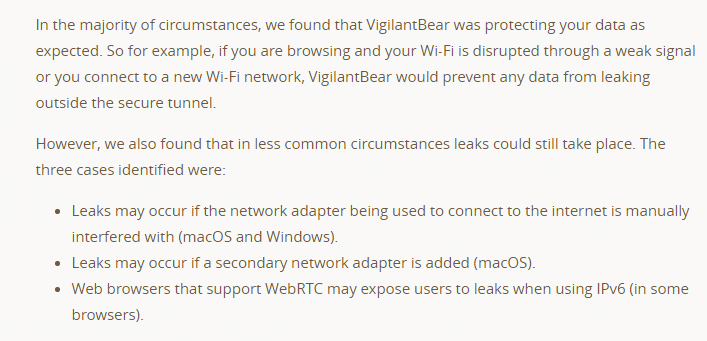
Next, we tested for IP and DNS leaks using ipleak.net. We're happy to confirm that no leaks were detected whilst using TunnelBear. Even better, we didn't detect any IP leaks on IPv4 or IPv6, either.
However, we did detect WebRTC leaks on both Windows and Mac while using IPv6. This means you'll need to disable WebRTC in your browser (or use a WebRTC blocking extension) if you want to use this VPN securely. Alternatively, you could disable IPv6 connections on your device.
TunnelBear claims to have a fix for WebRTC leaks under development, however, at the time of writing the problem persists.
Ease of use
Android
iOS
Windows
macOS
Linux
Signing Up
Signing up to TunnelBear is a blessedly easy process all the way through. To access the free plan, users need to enter an email address and password. Then, the site automatically redirects to the Downloads page where users can select the necessary software for their platform. Subscribing to any pain plan will, of course, require you to input credit card or Bitcoin information (PayPal is no longer supported).
The TunnelBear client downloads quickly, and a setup wizard walks you through a simple installation process without a hitch. Once installed, you'll be able to log in using your email and password.
Then, TunnelBear provides a quick walkthrough to explain its VPN capabilities. It'll ask subscribers to check their inbox for an account confirmation email, too. Once you've verified, you'll be able to start using the service and connect to a server.
The TunnelBear Windows VPN Client
The client looks great and is fun to use – which is a rarity! In keeping with its name, the software is filled with bear jokes and graphics that add a touch of whimsy to the experience. By default, TunnelBear connects to a random server situated nearby. If you'd rather select a specific location, you'll need to choose it manually from the list of server locations and hit connect.
Users can access a drop-down menu in the upper-left corner to change the VPN's settings. In General, subscribers can allow TunnelBear to boot up automatically when the computer starts up. Additionally, they'll be able to request that the client notifies them about a number of things; disconnections, disruptions to service, and network status information.
In the Security tab, users can enable the VigilantBear kill-switch and GhostBear stealth mode, a feature ideal for bypassing firewalls. Using the kill-switch is recommended at all times to prevent data from leaking to your ISP. GhostBear, however, is only necessary for people living in locations where VPN obfuscation is a must for sidestepping Firewalls or bypassing ISP throttling. In fact, GhostBear is actually TunnelBear's very own implementation of Obfsproxy.
Under Trusted Networks, users can add known networks and enable TunnelBear to connect to a VPN server every time they connect to an unknown network (perfect for people who use random public WiFi hotspots regularly).
Finally, the Account tab can be used to manage your subscription, request support using the ticket system, or to log out of TunnelBear VPN.
Other Platforms
As well as Windows, TunnelBear offers an iOS VPN app. The iOS client provides L2TP/IPsec encryption instead of OpenVPN encryption, so if you require OpenVPN, you'll also need to use third-party OpenVPN connect software (TunnelBear can help you to get this setup).
TunnelBear also provides an Android VPN app that uses OpenVPN, and is similar in design to the iPhone version. Tunnelbear will work as a Linux VPN, however, it is important to note that Linux users will require the third-party OpenVPN client.
Overall the apps are very similar on all platforms, are easy to use, and provide similar connection speeds across the board.
TunnelBear also has a browser extension that is free to download and can be used with either Chrome or Opera (but not Firefox). The browser extension is a nice addition, but remember that it is a proxy service as opposed to a full VPN service (it only proxies data within the browser). The browser extension is multi-platform (works with Linux, Chrome OS, OS X, and Windows).
Customer service
Money-back guarantee
24-hour support
Live chat
Money-back guarantee length
N/A
Free trial
Free trial length
1000
Currently, there's no live chat function on the TunnelBear site. This is disappointing, and makes getting in touch with the support team a little more complicated. TunnelBear does have a handy little chatbot you can interact with, however, and it works in a pinch. The bot primarily directs your attention to various support articles based on the query you have, allowing you to do your own troubleshooting. If you'd rather speak to support staff, you'll need to do so by email via the TunnelBear site.
To put the TunnelBear customer support to the test, I sent its representatives a question about encryption on the platform to gauge whether anything had changed or improved since our last review. As before, I received an email telling me to expect a response in 24 hours.
As it so happened, my response did arrive within 24 hours, though I did have to ask for clarification about a point which wasn't explained entirely clearly. Despite this hiccup, I found the team to be friendly and eager to help. What's more, TunnelBear's reply gave me the exact details I was after.
The TunnelBear Help page is easy to find and easy to use, with links to various categories. Troubleshooting walks users through basic installation and speed issues, Billing & Information is the place to go for any account queries, and Getting Started... well, does what it says on the tin! Here, you'll find beginner-friendly information covering the benefits of using a VPN, how to check that a VPN is doing its job, as well as TunnelBear's FAQ. The FAQ is straightforward and relatively short, but it does provide bite-size answers to the most burning questions – like which devices TunnelBear is compatible with, and how many simultaneous connections are allowed.
Head on over to TunnelBear's blog if you're in the mood for some light reading. The articles here are well-written and varied, and the blog itself looks great. It's not overly cramped or riddled with clunky lists and menus. Users can navigate to a particular category and take their pick of articles, or select one from the home page. These articles cover news bites, TunnelBear updates, and longer features – including an interesting piece on experiencing censorship in the Middle East as a child.
Privacy and security
Kill-switch
Obfuscation (stealth)
IPv6 leak protection
WebRTC leak protection
Self-hosted DNS
TunnelBear stores some minimal logs for a month. This is what TunnelBear says about having to comply with the authorities in Canada:
In the event TunnelBear is required to comply with law enforcement where subpoenas, warrants or other legal documents have been provided, valid under Canadian jurisdiction, the extent of disclosure is limited to the Personal information you provided upon registration as well as the overall number of connections, overall MBs used that month.
That is a fantastic privacy policy which means that no data about VPN usage, or a users IP address is linked to an account and can be used to mount a time-correlation attack:
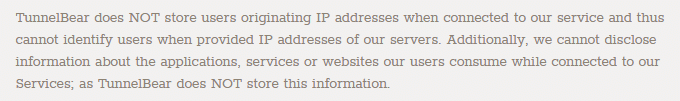
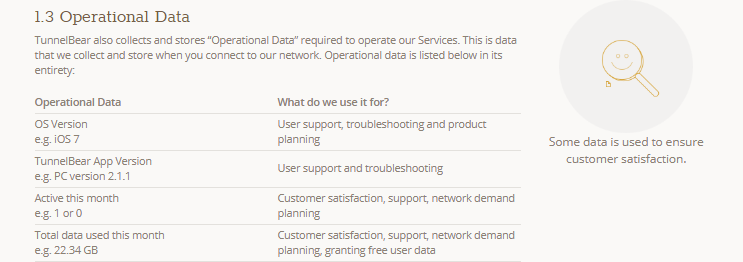
The highly minimal nature of what is kept by TunnelBear means that subscribers really never need to worry about what they use the VPN for. Even if served a warrant by the authorities TunnelBear VPN would have very little to hand over of any real value.
TunnelBear Terms of Service
It is worth noting that TunnelBear is based in Canada, a country that is a part of the infamous Five Eyes Treaty. Canada has been found snooping on citizens several times in recent years, but this doesn't stop TunnelBear from protecting your data.
While required to hand over data if approached by authorities, TunnelBear holds no connection logs or identifiable logs of any kind. As such, the most that the authorities should be able to get from the company is your name, email address, and payment details. It is also one of the only providers to perform regular full system, code and infrastructure audits by trusted third-party firms, and publish the results.
However, it's worth bearing in mind that TunnelBear does pretty much wash its hands of any responsibility for a number of things in its Terms of Service:
As you can see TunnelBear absolves itself of responsibility for just about everything. In addition, TunnelBear clearly states that users can't:
![]()
It also asks users to always abide by the laws of their own country and of the country that they tunnel into. All points that are definitely worth bearing in mind (especially because it is based in Canada).
Encryption Protocols
PPTP
L2TP/IPSec
SSTP
IKEv2
OpenVPN
Other protocols
-
WireGuard
When it comes to encryption, TunnelBear provides access to two different VPN protocols. The Windows, Android, and Mac OS X clients all implement OpenVPN. iOS users get the choice of either L2TP/IPsec) or IKEv2. Thus, anybody wishing to connect via OpenVPN on iOS will need to do so using the third-party OpenVPN Connect software (which is free).
Strong 256-bit Advanced Encryption Standard (AES) encryption with SHA256 authentication is used across the platforms, apart from iOS 8 and earlier (which is encrypted with 128-bit AES encryption and uses SHA-1 for data authentication).
All this information is available on TunnelBear’s blog, which is a fantastic level of transparency. Also positive: TunnelBear does not provide Point-to-Point Tunneling Protocol (PPTP) – an out of date form of VPN encryption that is now considered insecure and we always recommend against.
In addition to strong encryption and a strong privacy policy, last year TunnelBear invested in a third-party audit of its apps (but not server network). That professional security audit permits TunnelBear to confidently advertise the privacy and security provided by its software.
It is also worth noting that TunnelBear has now released updated software that protects against IPv6 leaks, and we found this to work successfully (last time we reviewed the service these were in Beta).
Final thoughts
TunnelBear is a fundamentally reliable service, with easy-to-use clients that'll make any VPN newcomer feel like a pro, and a charming design (who doesn't love bears?). The free plan is certainly a bonus, though 500 Mb per month won't go far, and won't be enough to use the service when streaming. However, it could help out anyone living in conflict areas or locations with heavy censorship. If you need to check out the news or perform other non-data-intensive tasks, then the free service will do just fine.
A strong privacy policy keeps users secure, and the few trivial connection logs that the firm keeps are for internal use only, and cannot be utilized to interfere with any subscribers' privacy. In addition to being based in Canada, TunnelBear's Terms of Service is a point of concern – seeing as it denies responsibility for just about anything and everything.
It's also worth noting that TunnelBear cannot access geo-blocked content from in-demand streaming sites. If you're looking to binge Netflix originals or catch up on the latest blockbusters, you'll need to shop elsewhere. However, if you're more concerned about shoring up your security, then TunnelBear offers solid pain plans and superb connection speeds.
0 User Reviews
Leave a Review
Thanks for your review!
35 Comments
Write Your Own Comment
Your comment has been sent to the queue. It will appear shortly.

Cabbache
Cabbache replied to Cabbache
Douglas Crawford replied to Cabbache
Douglas Crawford replied to Cabbache
Tom
Ray Walsh replied to Tom
karl
Your momma