Want to get the most out of your Netflix subscription? With a VPN for Netflix, you can access new titles that aren't available in your region at no extra cost. However, as with everything in life, there is a small catch. Many VPN providers struggle to access Netflix, so you'll need to stick to the few VPNs that can access this popular streaming service.
Are you tired of hitting a brick wall every time you try to access different Netflix libraries from your region? Navigating the digital maze of geo-restrictions might seem daunting, but what if the key to unrestricted Netflix content was just a VPN away? Let's explore the best VPN for Netflix, ensuring you can enjoy your favorite shows and movies no matter where you are in the world.
Finding the perfect Netflix VPN isn't just about unblocking content; it's about seamless streaming, maintaining speed, and keeping your browsing safe. The top contenders in this arena boast robust server networks, lightning-fast speeds, and iron-clad security features. They ensure that not only can you access a global content library, but you also enjoy it in the highest quality with no buffering.
We have reviewed over 150 VPNs, and always test them to make sure they can reliably access in-demand streaming services like Netflix. From our research, we've found that the following VPNs will work best:
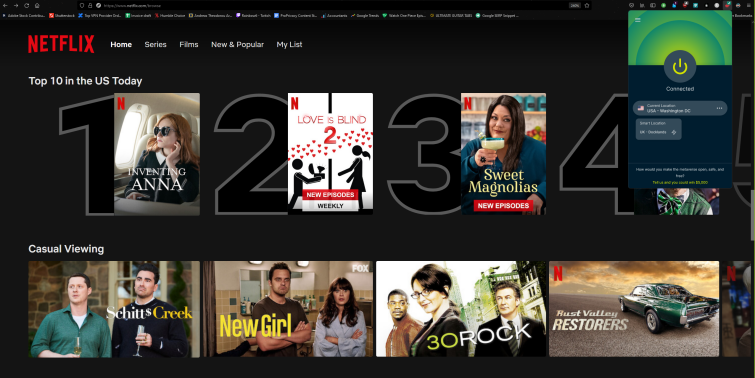
- ExpressVPN - The very best Netflix VPN. It accesses any Netflix library you'd like to explore, and offers a 30-day money-back guarantee.
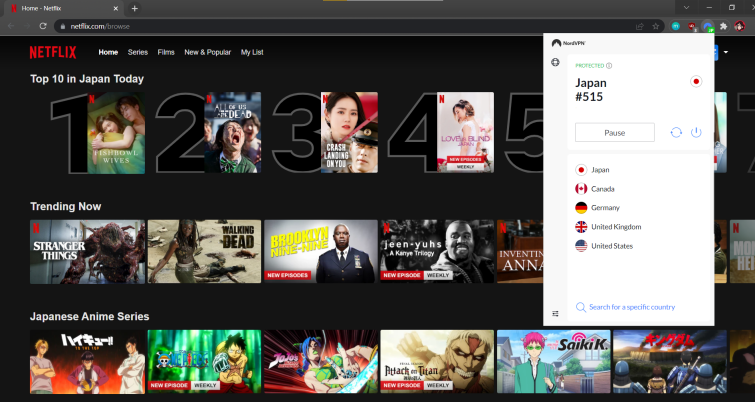
- NordVPN - The best value VPN for Netflix. A broad network of servers that can access regional catalogs, and apps for all devices.
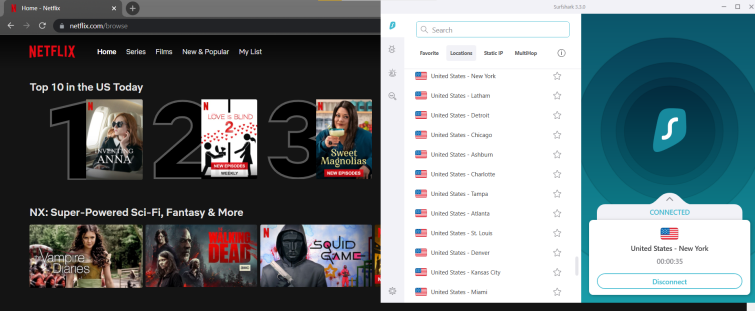
- Surfshark - The best midrange for money Netflix VPN with robust encryption, unlimited simultaneous connections, and user-friendly apps.
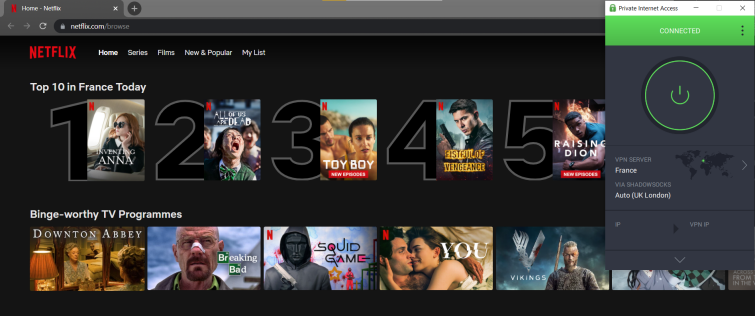
- Private Internet Access - The most secure VPN for Netflix. Open source apps and tough encryption, as well as a range of protocols.
- PrivateVPN - The best cheap Netflix VPN. Low-cost plans and easy-to-use apps help anyone broaden their Netflix horizons.
To ensure that we're recommending VPNs that can actually access Netflix, we regularly test the services listed on this page to ensure that they meet the following criteria:
- Can it access Netflix catalogs from around the world?
- Is it fast enough to stream in HD and 4K?
- Does it offer great customer service?
- Does it have great apps for popular devices?
| TEST WINNER ExpressVPN | NordVPN | Surfshark | Private Internet Access | PrivateVPN | |
|---|---|---|---|---|---|
| Website | ExpressVPN | NordVPN | Surfshark | Private Internet Access | PrivateVPN |
| Ranking for Deezer | 1 | 2 | 3 | 4 | 5 |
| Performance | 10 | 9 | 9 | 8 | 7 |
| Reliability | 9 | 8 | 8 | 8 | 7 |
| Free trial | |||||
| Total servers | 3000 | 6200 | 3200 | 3386 | 200 |
| Payment | PayPal Visa/MasterCard Amex Cryptocurrency | PayPal Visa/MasterCard Amex Cryptocurrency | PayPal Visa/MasterCard Amex Cryptocurrency | PayPal Visa/MasterCard Amex Cryptocurrency | PayPal Visa/MasterCard Amex Cryptocurrency |
| Unblocks: | Netflix iPlayer Disney+ Amazon Prime Hulu | Netflix iPlayer Disney+ Amazon Prime Hulu | Netflix iPlayer Disney+ Amazon Prime Hulu | Netflix iPlayer Disney+ Amazon Prime Hulu | Netflix iPlayer Disney+ Amazon Prime Hulu |
| Supported platforms | Windows macOS iOS Android | Windows macOS iOS Android | Windows macOS iOS Android | Windows macOS iOS Android | Windows macOS iOS Android |
The 10 best VPNs for Netflix | In-depth analysis
Below, we take a closer look at the ten best Netflix VPNs on the market. If you'd like to learn more about any of the providers listed here, or want to compare even more services, then head on over to our dedicated review pages.
ExpressVPN is the best Netflix VPN. It's lightning-fast, unblocks Netflix (and other services) in a few clicks, and has apps for all devices. With a 30-day money-back guarantee. ExpressVPN Demo ExpressVPN is a titan of the VPN industry, and one that's an absolute joy to use! Its apps download in a few clicks, meaning you can start unblocking Netflix libraries right away, and there are plenty of security-enhancing features to play with, too. Admittedly, an ExpressVPN won't come cheap, but I think it's clear that you're paying for a premium provider that's at the top of its game. ExpressVPN remains my go-to service when it comes to checking out international Netflix catalogues – and that's because it can unblock content from pretty much anywhere you can imagine. In fact, ExpressVPN has servers in 105 countries
countries around the globe! During my tests, I had no trouble connecting to Netflix US, UK, and Japan, and hopping across Europe to browse through specific libraries was a cinch, too. It's well worth noting that ExpressVPN is seriously fast. It routinely claims a top spot in our daily speed tests, so you won't have to worry about low-quality streams or buffering interruptions ruining your movie marathons. Plus, ExpressVPN can also put a stop to ISP throttling! This is a quick, reliable service that's well-suited to unblocking streaming services from around the globe, and can even keep up with online gaming and VoIP calls. Nobody wants to be tracked across the web by a nosey ISP or network admin, and ExpressVPN's solid OpenVPN encryption ensures that your browsing sessions remain private. Users also have the option to select a different VPN protocol, which can come in handy if you're looking to tailor your connection! For example, OpenVPN is my top pick for secure browsing, especially when relying on public Wi-Fi hotspots, but IKEv2 is a great alternative for those looking to maximize their speed. ExpressVPN's proprietary protocol, Lightway, is also making waves, seeing as it balances performance and privacy into one lightweight package – so it's worth checking out if you're an avid streamer! ExpressVPN leads the pack when it comes to proving its commitment to privacy. For a start, its zero-logs policy clearly states that it has no interest in storing your activity or connection logs, and the provider has even invited powerhouse auditing firm, PwC, to validate these claims. It's this kind of transparency that keeps ExpressVPN at the top of our list – and why I recommend it to anyone who wants a super secure service that can unblock anything you point it at. The ExpressVPN apps are some of the freshest on the market! They have an arty design that's free of clutter and feel thoroughly modern, and I'm confident that VPN newbies will have no trouble navigating through the GUI to tweak settings or find their perfect server. These apps are available for all devices, and you'll even be able to use ExpressVPN on your smart TV – so you can stream international Netflix content from the comfort of your living room! Ideally, ExpressVPN will up the amount of simultaneous connections on offer from 8
to something more generous, to keep up with cheaper providers offering more for less. Whilst ExpressVPN is easy to use and install, a superb customer service team is available 24/7, via live chat and email, if you run into trouble. Plus, with a 30-day money-back guarantee, you'll have plenty of time to trial ExpressVPN on your own devices, and explore new Netflix content from across the globe. NordVPN is the best value Netflix VPN. It's jam-packed with features and incredibly easy to use, with a 30-day money-back guarantee. Nord Demo NordVPN is the full VPN package – and its modest price tag is the cherry on top. With NordVPN, you're getting a privacy-oriented service that has plenty of customizable features as well as geo-unblocking power, so you can stream international Netflix shows and stay secure whilst you do it! NordVPN's apps are some of the most intuitive out there, too, which makes the provider a great pick for VPN newcomers. NordVPN blew me away during the testing process! It was able to unblock US, UK, and Japan Netflix libraries without any hassle, and I could even check out content from across Europe with the same ease. Ultimately, NordVPN makes it possible (and downright easy) to get the most out of your Netflix subscription. With servers in 111 countries
countries, you'll also be able to unblock geo-restricted content hosted on a wealth of other streaming services – Amazon Prime and BBC iPlayer included. I also liked that NordVPN has a large selection of specialty servers, including servers optimized for P2P activity, double VPN, and Onion over VPN. This allows users to tailor their VPN experience depending on what they plan to do whilst connected, and helps keep NordVPN's generic servers free from congestion – it's a win/win! The Quick Connect feature is another handy extra that shouldn't go ignored. It uses a special algorithm to detect, and connect you to, the server that suits you best, which comes in particularly handy for commuters or adventurers using mobile devices. As you'd expect from a premium provider, NordVPN supports OpenVPN encryption, which is perfect for preventing third party snooping! If you'd rather pick your own protocol, you can check out the speedy IKEv2/IPsec at the push of a button, or even opt for NordVPN's very own NordLynx, which is built around the blisteringly fast WireGuard protocol. I especially like that NordVPN's automatic kill-switch was enabled by default; this means that users don't have to go searching through settings to toggle it manually. This kill-switch keeps your original IP from leaking in the event of a VPN dropout, and can be customized to specify which apps should be affected. NordVPN is a zero-logs service that won't collect your identifiable logs, like connection timestamps, IP addresses, and traffic data. To further cement its position as a champion of user security, NordVPN invited PwC, a big-name auditing firm, to comb through its logging claims. Just like ExpressVPN, this is an encouraging move that I hope other services emulate – and I hope NordVPN continues to invest in these audits as the years go by! My favorite thing about NordVPN is just how user-friendly its apps are. There are no overwhelming GUI elements to battle, and even the VPN's advanced options are clearly labeled in its settings menu. The NordVPN map is a particularly great piece of interface, too! It's fun and stylized, and users can click and drag to navigate around it. I think this is a great way of visualizing the distances between certain servers – and this is an important consideration for anyone who wants to minimize their latency. NordVPN's customer service team is quick to respond and not deterred by techy questions, so be sure to reach out whenever you're in need of advice; the team is available 24/7 via live chat and email. As with all our top providers, a NordVPN subscription comes with a 30-day money-back guarantee, so you can put the service through its paces without risking a single dime. Surfshark is the best midrange for money Netflix VPN. Users get a long list of security features, reliable access to Netflix, and a 30-day money-back guarantee. Surfshark Demo Surfshark is another relative newcomer to the VPN scene – and its already making waves! The service unblocks virtually any streaming platform you can imagine, whether they're international giants or local services, and makes it easy to follow your favorite shows on any device. Oh, and don't forget about the unlimited simultaneous connections. Using Surfshark during my tests was a breeze – I had no trouble connecting to the Surfshark servers or hopping from location to location, and the VPN was able to unblock the UK, US, and Japan libraries without issues. I was also able to browse geo-restricted content across Europe! Users can (and should) take advantage of the Surfshark servers to check out previously restricted content libraries on Netflix, Amazon Prime, and Hulu, and even unblock social media services that might've been blocked by your workplace or school. Being able to favorite servers made them much easier to find again the next time I booted up the VPN (and I think Netflix fans should use this feature to bookmark the servers they use to unblock the site!). I also liked that Surfshark's Connect Options can automatically pick out the fastest local server, which comes in handy if you're looking to eliminate latency, or even connect you to the closest, quickest server that isn't in your home country. Surfshark users get their pick of battle-tested VPN protocols, including OpenVPN, IKEv2, and WireGuard. I recommend sticking to OpenVPN if you want a well-rounded, secure connection, but WireGuard is a great alternative for those folks (like streamers and gamers) who want to prioritize performance! Surfshark even comes with the Shadowsocks encrypted proxy. This isn't a VPN protocol, but it can help users overcome oppressive internet restrictions – like the Great Firewall of China. There are a veritable wealth of security features to check out, too, like a kill-switch that'll keep your data secure in the event of a dropout (although you'll need to toggle it on, first) and a CleanWeb feature which removes trackers, ads, and malware from your browsing sessions. I'm also happy to report that Surfshark is a fully audited zero-logs provider! The VPN won't store your digital whereabouts or activities, and has worked with Cure53, renowned security testers, to validate its logging policy. As a result, you can rest assured that your digital footprint will remain private. One of Surfshark's main bragging points is its unlimited simultaneous connections. This is a big deal, as it means that you'll be able to secure all of the devices in your home, share your subscription with friends and family, and still have connections to spare! It's great value for money, especially when you consider that Surfshark apps are available for all major platforms, too. I really like the Surfshark apps. They feel clean and uncluttered, and it's easy to navigate through the server list or tweak settings – there are no clunky UI elements to slow you down. As with most of our top Netflix VPN picks, Surfshark's customer support team is available 24/7 via live chat and email – so don't hesitate to get in touch if you run into any issues. The provider also offers a 30-day money-back guarantee, so you can take Surfshark for a test spin (or should that be test swim...) before deciding whether to take the plunge with a longer subscription. However, a 7-day free trial is also available to Android, iOS, and Mac users! Private Internet Access is the most secure Netflix VPN. Includes advanced security options, superb OpenVPN encryption, and a 30-day money-back guarantee. PIA Demo Private Internet Access (PIA) is one of the most security-oriented services in our top 10 – and in the industry at large! Its suite of customizable features make it particularly well-suited to advanced VPN users who want to tailor their VPN connection, but its instant setup and inuitive apps also keep it accessible to newcomers interested in unblocking Netflix US. PIA has an enormous network of servers dotted across 84 countries
countries – and that's great news for anyone looking to unblock multiple Netflix libraries! During my tests, PIA was able to unblock the UK, US, and Japan catalogs in a few clicks, although I was served with a collection of generic Netflix originals when attempting to browse through the Spanish library. As a result, I'd recommend PIA to anyone who wants to check out the larger geo-restricted catalogs, like the UK and Japan – and thanks to its "domestic focus" in the US, PIA is a great option for those looking to access American content. I liked that PIA lets users favorite servers, too! It's a neat little consideration that allows users to curate their own personalized lists that can be real time-savers – for example, you could favorite the servers you routinely use for unblocking Netflix or Amazon Prime (or any number of popular streaming services), or the local server you prefer when relying on public Wi-Fi hotspots. Whether you're streaming the newest Netflix original, hopping into a gaming lobby, or banking online, PIA prevents snoopers from pawing through your sensitive details. It implements sturdy OpenVPN encryption, although users can also opt for the speedy WireGuard alternative, and packs a plethora of extra security features that are well worth checking out. PIA's ad-blocking functionality can be toggled on via a simple switch, and will banish ads and trackers from your browsing sessions, and its kill-switch is automatically enabled by default. PIA is a zero-logs provider that isn't interested in storing your user data, although some prospective customers may be put off by the fact that its based in the United States. It's understandable, given that the US is home to the invasive NSA and CIA, but PIA has proven its zero-logs claim in court on multiple occasions, so I have no qualms about recommending it to even the most private of individuals. Ideally, PIA will also one day working with a public auditing firm to carry out a public security audit of its logging policies. There are PIA apps for Windows, Mac, Linux, Android, and iOS, so you'll be able to take your Netflix subscription (and unblocking power) with you wherever you go! The VPN also supports up to Unlimited
simultaneous connections. This means that you'll be able to share your subscription with friends and family, if you're feeling generous, and I'm condiment that anyone will be able to use PIA's apps, thanks to a clean, straightforward interface. The PIA customer service team (who are around 24/7) doesn't shy away from complicated questions, and can also help you pinpoint which server you should connect to in order to unblock a particular Netflix library. A 30-day money-back guarantee gives users the opportunity to try the service before committing to a lengthier subscription, and iOS and Android users can even take advantage of a free 7-day trial! PrivateVPN is the best cheap VPN for Netflix. A feature-rich and easy-to-use service that has a 30-day money-back guarantee. PrivateVPN Demo I'm consistently impressed by PrivateVPN, one of the newer VPN providers on the block, and one that proves that a premium-feeling service doesn't need to cost the earth. PrivateVPN can unblock Netflix libraries with ease, thanks to its dedicated IP addresses, and has plenty of security features to safeguard your traffic data. If you're looking to unblock Netflix libraries from around the world whilst using PrivateVPN, make sure you check out the provider's dynamic dedicated IP addresses! They're housed in their own tab in the PrivateVPN app and are available to all users at no extra cost – which is pretty generous. These dedicated IPs make it incredibly easy to unblock Netflix content; just connect to the dedicated IP in the location of your choice, load up Netflix, and enjoy a new selection of shows and movies! Using these servers, I was able to unblock the US, UK, Japan, France, and Spain catalogs without breaking a sweat. I like that PrivateVPN displays the speed of its servers, so you can pick out the best performers at a glance, and servers can also be favorited for future reference. Admittedly, PrivateVPN has fewer servers overall than other providers on this list – but that's because the firm is still young, with plenty of growing to do, and I expect to see it expand across the globe in due course. You'd expect a service called PrivateVPN to live up to its name – and I'm happy to confirm that it very much does! OpenVPN keeps invasive ISPs and governments from monitoring your digital footprint, and keeps you and your identifiable data secure whilst using public Wi-Fi hotspots. Users can also check out the IKEv2 and L2TP protocols, with the up-and-coming WireGuard currently in beta. PrivateVPN's kill-switch is enabled by default, so you don't have to spend extra time configuring the feature, and I like that the provider's stealth feature is a togglable switch. This feature, called Stealth VPN, can help folks living in oppressive regimes bypass pesky VPN bans, and its great to see an inexpensive service like PrivateVPN offer it for free. Currently, PrivateVPN makes its home in Sweden – and this isn't totally ideal, seeing as the country has some gnarly data retention laws. PrivateVPN is a zero-logs provider, however, which should allay most concerns (seeing as it'd have no user logs to hand over to authorities who come knocking with warrant). As with Private Internet Access, I would like to see the service invest in a public security audit to verify these claims. There are PrivateVPN apps available for Windows, Mac, Android, iOS, and Linux devices, so you can cover a whole household full of gadgets, and up to 10
simultaneous connections are supported. One of my favorite things about PrivateVPN is its user interface. All of the providers apps look friendly, are easy to click through, and don't require an encyclopedic knowledge of cybersecurity to use! It's this blend of quality and value-for-money that makes PrivateVPN a great pick for VPN newcomers or folks who want a straightforward experience. I have to commend the PrivateVPN customer service team, too, seeing as they were able to answer all of my Netflix-related questions in a timely manner. The team is around 24/7 via live chat and email, and composed of in-house developers who are happy to walk users through their queries. Be sure to take advantage of PrivateVPN's 30-day money-back guarantee – or, if you'd rather not part with a penny, check out the free 7-day trial! CyberGhost is the best user-friendly Netflix VPN. Its apps install in a blink and make unblocking international Netflix libraries a breeze. With a 45-day money-back guarantee. CyberGhost Demo For a lot of people, the first time they use a VPN will be to unblock Netflix (or other streaming services), so it's important that the client app is intuitive, easy to use, and not completely stuffed with technical jargon. CyberGhost ticks these boxes; its friendly apps make geo-hopping across the globe a straightforward process, and even customizing your security settings is a breeze. During testing, I was able to unblock all major Netflix libraries with CyberGhost – though I was served with generic content when attempting to browse Japan-specific content. Of course, whether a VPN can or cannot access a given library is something of a cat and mouse game, and you might have more luck! Generally speaking, however, CyberGhost is a great pick for avid streamers, thanks to its huge network of servers spanning 100 countries
countries. This gives users access to geo-restricted shows and movies from across the globe, via all sorts of streaming sites, and Netflix is most certainly one of them. I liked that CyberGhost has servers specialized for streaming, gaming, and torrenting, seeing as it makes the process of picking out a perfect match that much easier. If you'd rather have CyberGhost do the hard work for you, you can also get a tailored recommendation based on your preferences and geographical location – and this is especially useful for folks using mobile devices who want a speedy and secure connection. CyberGhost packs strong OpenVPN encryption, which is just what you need if you want to keep third party snoopers away from your sensitive traffic. Users can stick with OpenVPN to maximize their digital security, or opt for IKEv2 or WireGuard alternatives – and it only takes a few clicks to do so! The CyberGhost kill-switch is enabled by default, too, reducing the amount of time you'll need to spend tweaking settings, and the service's DNS and IP leak protection ensure that you'll be able to browse the web without worrying about whether you're leaving an identifiable trial. It's also great to see that CyberGhost abides by a zero-logs policy – however, the service hasn't invested in a security audit since 2012. I think it's time that CyberGhost joined forces with a public auditing firm to prove that they follow their privacy policy to the letter! Even so, privacy-conscious individuals will appreciate that the VPN is based in Romania, a country without data retention laws or ties to the 5 or 14 Eyes surveillance alliance. Often, when I speak to folks who haven't used a VPN before (but want to unblock Netflix), they're worried about the client being too complicated for them to use. In these cases, I'll recommend that they check out CyberGhost! Very few services have apps that are as intuitive or self-explanatory, and I particularly like that they don't look too different than the menus you might find on an ordinary Windows device. Users can install CyberGhost on just about any platform, of course, and the service currently supports 7
simultaneous connections. This is roundabout the industry standard, and should be more than enough for you to cover all of your favorite gadgets. If you'd like help getting things set up, or want to know which server would suit your needs best, reach out to the CyberGhost customer service team. They're available 24/7, and can handle your requests in a whopping four languages! CyberGhost also gives users a generous 45-day money-back guarantee – so you'll have over a calender month to explore the VPN's features and unblocking power for yourself. Or, if you want something more immediate (and free), you can check out a 24-hour trial via the CyberGhost website. VyprVPN is the best all-rounder VPN for Netflix. It's a service that combines excellent server coverage, security, and a 30-day money-back guarantee. VYPR Demo VyprVPN is a well-known and well-respected service that has the potential to be a streamer's best friend. I like that it offers apps for all platforms, access to all sorts of streaming services, and some handy security features that'll keep your digital footprint private. Best of all, you can scoop up a VyprVPN subscription for a pretty modest price! VyprVPN had no trouble connecting to Netflix during my tests, although I was often served with generic content (like Netflix originals or shows that the provider has a global license for), so the VPN may be a better option for folks living somewhere where the site is blocked entirely. However, as always, a VPN that struggles to unblock a certain library one day may have better luck on another. VyprVPN certainly has an impressive network of servers in 70
locations, and the provider is one of only a handful to offer real coverage across Africa and South America! I was also impressed by VyprVPN's connection times. Even when I selected a server in Japan, the VPN connected almost immediately, and I was able to reload Netflix and comb through a new library of content in less than a minute. Users who want to maximize their performance, and minimize the impact of latency, also have the option of displaying servers by speed rather than location, which is a handy quality-of-life feature I'd recommend making good use of! VyprVPN doesn't pull punches when it comes to safeguarding user security – and the service owns its own servers, hardware, and DNS, which dramatically reduces the risk of third party interference or disruptive man-in-the middle-attacks. That's great news for folks who plan on streaming Netflix whilst on the commute, or when relying on public Wi-Fi hotspots in an airport or cafe. As per usual, VyprVPN supports the OpenVPN and WireGuard protocols, and also offers its very own Chameleon protocol! Chameleon scrambles OpenVPN metadata to make it impervious to Deep Pack Inspection (DPI), so you don't have to worry about VPN bans or government-imposed censorship issues that might otherwise impede your ability to access Netflix catalogues via a VPN. As you'd expect from a service in our top ten, VyprVPN is a zero-logs provider, and one that's gone the extra mile and invited independent auditors, Leviathan Security, to sift through its privacy policy. VyprVPN even made Leviathan's report accessible to the public – which is a nice gesture of transparency that other services could learn from. The VyprVPN apps are fairly straightforward to use, even if their design is a little on the clunky, cramped side. It was easy to switch protocols, but I didn't like that doing so required tapping through a separate layer. It'd be much sleeker to have these settings all contained on one page that the user could scroll through, without having to navigate back and forth between layers, but these are aesthetic issues that don't impact the VPN's performance. On the brighter side, it's great that VyprVPN allows for 10
simultaneous connections! This gives users the opportunity to cover all the devices in their home... and then some. VyprVPN support is dished out 24/7 via live chat, email, and a handy FAQ page that might be especially useful for newbies. If you fancy taking the VPN for a test drive in your own time, a 30-day money-back guarantee is just what you need – and just what VyprVPN offers. IPVanish is the best multi-platform Netflix VPN. With unlimited simultaneous connections, users can stream content from any device. With a 30-day money-back guarantee. IPVanish Demo IPVanish is a robust service that's a great pick for anyone who has a small army of devices they'd like to secure – or use to stream fresh Netflix content! For a budget price, users get unlimited simultaneous connections to play with, as well as top-notch encryption that'll deter even the most invasive snoopers. IPVanish has an impressive spread of servers in over 75
locations, so you'll be able to unblock content from pretty much any spot on the globe! When putting the service to the test with Netflix, however, I had a little trouble reliably unblocking the service – though this isn't entirely unsurprising, seeing as IPVanish doesn't officially claim to offer access to all international catalogs. Unblocking content from the UK and US was easy-peasy, and if you want to stream shows from across Europe, I'd suggest connecting to servers that aren't located in capital cities. For example, IPVanish's Madrid server didn't unblock Netflix ES, but its Valencia one did. What I like about IPVanish is that it comes with a ton of auto-connection customization. This is handy for those folks who have dedicated devices that they use for streaming, like a tablet or a laptop, and who want to save time by having IPVanish automatically connect to their server of choice when they boot up the app. The internet is full of prying eyes, unfortunately, and even your ISP and workplace can keep tabs on the sites you visit or the things you download. IPVanish can put a stop to this snooping, thanks to its superb OpenVPN encryption! The IKEv2 and WireGuard protocols are also available, amongst others, so users have the option of tailoring their encryption to suit their needs (and WireGuard is a great pick for anyone looking to improve their speeds whilst streaming). The IPVanish kill-switch isn't enabled by default, but you can simply check the box on the main screen of the app to switch it on. Similarly, IPVanish's "Scramble" option can be toggled on and off with a click – and this obfuscation (stealth) feature can help overcome VPN blocks imposed by countries with a less-than friendly attitude towards the tech. IPVanish abides by a zero-logs policy, and although the service performed an internal audit after its acquisition in 2017, I'd like to see it invest in a public security audit, too. This is doubly important when you consider that IPVanish is based in the United States – a country known for its liberal use of warrants and gag orders that can force VPN providers to hand over user logs! Fortunately, IPVanish's logging policy prevents this grim eventuality, but an audit would go a long way to properly reassuring users. During testing, I was blown away by how quickly IPVanish installed – I barely had time to take a sip of my drink before it was ready to use. The app's interface is a little more cluttered than I'd like, especially if you're looking at the server map instead of the server list, and I recommend maximizing the tab wherever you can. However, any Windows, Max, Android, iOS, or Linux device will be compatible with the service, which boasts an impressive unlimited simultaneous connections! This is superb value-for-money, and gives users the chance to share the unblocking power with interested friends and family. As always, an excellent customer support team is on-hand 24/7 to field questions via live chat and phone, and a 30-day money-back guarantee allows prospective subscribers to play with the IPVanish app without risking a penny. Ivacy is the best specialized Netflix VPN. It has dedicated streaming servers, great speeds, and a 30-day money-back guarantee. Ivacy Demo Ivacy is a fantastic all-rounder that boasts some seriously nifty streaming features – like platform-specific servers and coverage across more than 100
locations. In addition, the VPN can be installed on all devices, so you can stream at home, on the go, or even at work. I didn't have any trouble unblocking key Netflix catalogues with Ivacy, and was able to browse US, UK, Japan, France, and Spain libraries by simply hopping servers and reloading my Netflix tab. Ivacy is a particularly great pick for movie fans thanks to its staggering collection of site-specific streaming servers! The US Netflix option worked like a charm, and there are Hulu, BBC iPlayer, and Amazon Prime options to check out, too. All in all, there are Ivacy servers dotted across 100
locations, so users shouldn't have trouble unblocking geo-restricted content – whether that's Netflix exclusives, social media sites, or even news outlets that might've been restricted by an oppressive government. Ivacy uses well-implemented OpenVPN encryption to prevent nosey third parties from following your activity across the web – nobody wants their ISP or network admin keeping tabs on the sites they visit, after all. L2TP and IKEv2 protocols are also available, which gives users some extra alternatives that can come in handy if you're having trouble unblocking Netflix via OpenVPN. I like that Ivacy protects users from DDoS attacks and IPv6 leaks, which is particularly useful to gamers or Twitch streamers who might otherwise be targeted by disgruntled opponents or sore losers. A kill-switch is another great security feature that prevents your original IP address from leaking – you'll just have to remember to activate it, first! Ivacy scores another point for abiding by a zero-logs policy, although it misses out on full marks seeing as it hasn't invested in a security audit. Plenty of other premium services have taken this extra step to reassure users and prove their commitment, so it'd be great to see Ivacy follow suit in the near future. Admittedly, my Ivacy app took a long time to install on my Windows device – and booting up the app sometimes takes ages, too. This is a bit annoying, especially if you're in a rush to tune in to Netflix, and I'm not a huge fan of the Ivacy UI, either. It doesn't feel as fresh or modern as the ExpressVPN or Surfshark apps (and the Ivacy Chrome extension is especially tricky to navigate), but similar to IPVanish, these issues are purely cosmetic. Ivacy currently supports 10
simultaneous connections, which is fairly generous, and is compatible with pretty much any platform you can imagine – including Linux devices! If you need help getting your Ivacy app setup, the customer service team can help you out at any time via email, live chat, or support ticket. It's well worth trying Ivacy for yourself, and with a 30-day money-back guarantee, you'll have ample opportunity to do so. ProtonVPN is the best privacy-oriented VPN for Netflix. Fully audited, packed with security features, and with a 30-day money-back guarantee. Proton Demo ProtonVPN, developed by the same good folks over at ProtonMail, is an outstanding security-conscious VPN that packs some impressive privacy features. However, it's also a great pick for streaming fans, thanks to its broad network of servers and reliable access to some of the world's most in-demand streaming services. ProtonVPN made unblocking Netflix libraries nice and easy, and I was able to browse the UK, US, France, and Spain catalogs by server-hopping. The Japan catalogue gave me more trouble, and I often found myself scrolling through a generic library of Netflix originals instead of location-specific shows and movies. Generally speaking, however, ProtonVPN's server network is expansive, and ideal for bypassing geo-restrictions, thanks to servers in 91 countries
countries. As well as Netflix, ProtonVPN can reliably unblock Hulu, BBC iPlayer, and Amazon Prime – so you'll be spoiled for choice! Like many of our other top picks, ProtonVPN allows users to Quick Connect to the server that'll suit them best – and this is a great feature to have if you spend a lot of time using public Wi-Fi hotspots and need quick access to a speedy server. I like that the service clearly marks which servers are reserved for free and Plus users, as well as which ones support P2P activity and VPN over Tor connections, so you can streamline your connection process and help prevent congestion. ProtonVPN was originally developed to protect activists and journalists, and now offers its superb encryption to all users. No matter if you want to avoid ISP snooping, government censorship measures, or workplace bans, ProtonVPN's OpenVPN encryption has you covered. Alternatively, you can check out the IKEv2 and WireGuard protocols if you're after a speedy substitute suited to streaming. It's great to see that ProtonVPN uses Perfect Forward Secrecy, too, which ensures that your encrypted traffic can't be decrypted again later by an opportunistic hacker – and the provider also blocks more mundane, and irritating, ads and trackers (though you'll first need to enable this option). Finally, as ProtonVPN is based in Switzerland (a country that isn't part of the infamous 14 Eyes surveillance network), there are no mandatory data retention laws to worry about. The good news doesn't stop there. ProtonVPN is a zero-logs provider that invited SEC Consult to examine its claim in 2020. These audits are just what I like to see from the industry's leading services. I enjoy using the ProtonVPN app and think it looks pretty stylish – and I had no trouble navigating my way around the server list and settings menu. Unfortunately, the map is purely decorative, though it does come in handy when trying to visualize the distance between servers (and make rough estimates about the amount of latency they might experience). There are ProtonVPN app for just about any platform you can imagine, including Linux devices, and users get up to 10
simultaneous connections to play with. This is more than enough to ensure all the gadgets in your house are covered and secure! Currently, ProtonVPN is lacking live chat support. This is disappointing, seeing as it makes it much harder to receive quick answers to questions big and small. Users instead have the option to email, use a contact form, or even reach out to the ProtonVPN team via Twitter. If ProtonVPN sounds like your perfect match, you can put it to the test without losing a penny thanks to a 30-day money-back guarantee. 1. ExpressVPN
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for
Website

Unblock absolutely everything
Unwavering security
Style and substance
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for
Website

Versatile streaming
Tailored security options
Apps for all devices and users
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for
Website

Easy streaming
Clean surfing
Breaking the limits
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for
Website

Spoiled for choice
Security you can see for yourself
Cross-platform functionality
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for
Website

Dedicated IPs for reliable access
Private by name and nature
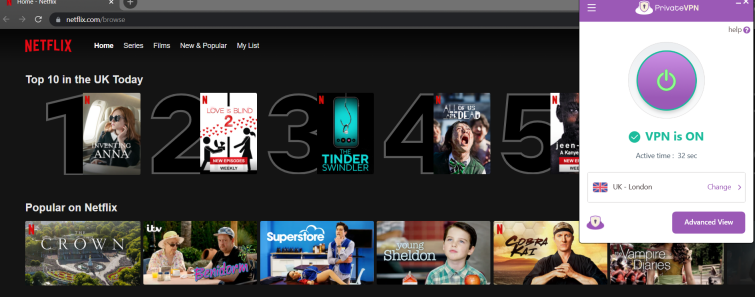
A user-friendly experience
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for
Website

A selection of servers
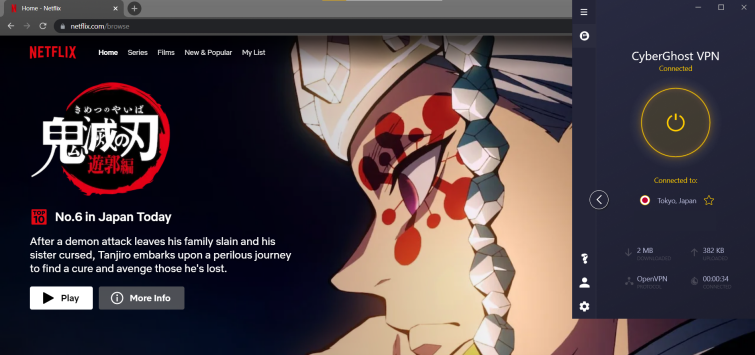
Threat protection
Awesome, accessible apps
7. VyprVPN
 www.vyprvpn.com
www.vyprvpn.com
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for

All corners of the globe
Proprietary privacy

Keep connected
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for
Website

Customize your connection
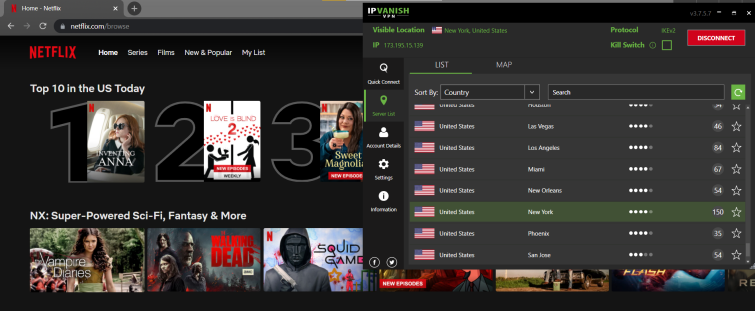
One-click obfuscation
Download, install, stream
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for
Website

Specialized streaming servers
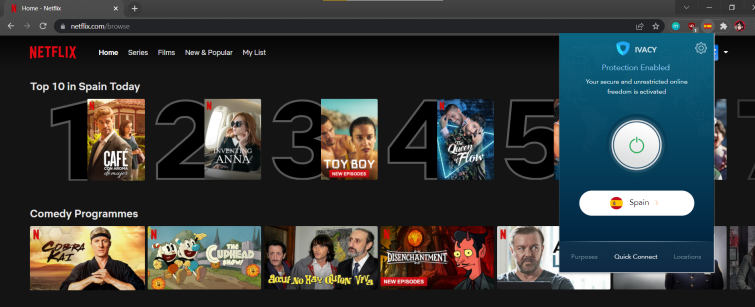
Private web browsing
Try before you buy
Pricing
Pros
Cons
Average server speeds
Unblocks content in the Netflix app
Unblocks Netflix in a browser
Unblocks popular Netflix libraries
Available for
One-click streaming
Designed with privacy in mind
Coverage for all devices
Compare the number of libraries they access
Before we recommend any VPN service to our readers, we put it to the test ourselves to figure out how many Netflix regions it can access, and whether it can access the most popular libraries – and we make sure to check out the Netflix USA, Canada, UK, France, Germany, and Japan libraries in particular.
Take a look at the table below to compare services based on which regions they access. We haven't included each and every Netflix region, however, just the ones with consistently popular content.
| No Value | ExpressVPN | NordVPN | Surfshark | Private Internet Access | PrivateVPN |
|---|---|---|---|---|---|
| South Korea | |||||
| France | |||||
| United States | |||||
| Canada | |||||
| United Kingdom | |||||
| Japan | |||||
| Denmark | |||||
| Finland | |||||
| Germany | |||||
| Norway | |||||
| Sweden | |||||
| Italy | |||||
| Australia | |||||
| Argentina | |||||
| India | |||||
| Israel | |||||
| Turkey | |||||
| Singapore | |||||
| Poland | |||||
| Belgium | |||||
| Mexico | |||||
| Portugal | |||||
| Thailand | |||||
| Chile |
How does ProPrivacy review VPNs?
Reviewing VPNs is a huge part of ProPrivacy's mission, and I've tested all of the VPN providers on this page to make sure they can access international Netflix catalogs. I kept my tests straightforward, to mimic the steps an ordinary user would take, and to weed out any services that require an overly complicated streaming configuration.
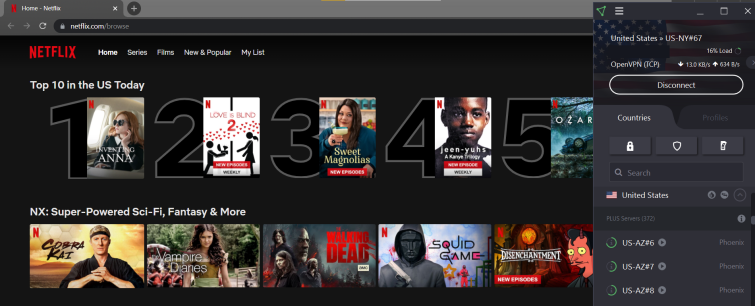
First, I installed the VPN app (and its browser extension, if applicable) and connected to an international server. I then opened Netflix in my Chrome browser. From here, I checked to see if the homepage was displaying location-specific shows, and clicked on content to make sure that it loaded, streamed in HD, and wasn't interrupted by buffering issues. If a VPN ticked all these boxes, I was happy to include it in this top 10 guide.
Want to learn more?
Head over to our review process page for a more in-depth explanation of ProPrivacy's testing process.
What is the fastest VPN for Netflix?
If you're using a VPN to stream Netflix, then it's important the VPN provider has servers fast enough to deliver HD content without buffering interruptions. To that end, we test the server speeds of 27 industry-leading VPNs on a regular basis to find the quickest providers.
| ExpressVPN | NordVPN | Private Internet Access | |
|---|---|---|---|
| ProPrivacy.com SpeedTest (average) | 100 | 85.9 | 62.2 |
| Speed | 100 | 568.0 | 254.93 |
| Performance | 10 | 9 | 8 |
| Reliability | 9 | 8 | 8 |
For more information on VPN speeds, you can check out our speed methodology.
Will a VPN improve my speeds for streaming?
The internet is full of people claiming that a VPN can speed up your internet. However, unless your ISP is actively throttling your bandwidth, this isn't true.
A VPN must constantly encrypt and decrypt your traffic and route it via a VPN server, which will usually have a slight negative impact on your speeds. However, the fastest VPNs can do this without slowing your internet down much at all – so you can still stream HD content on Netflix without issues.
How to access Netflix with a VPN
It's incredibly easy to use a VPN with Netflix. To check out more content, all you need to do is sign up for a compatible service and follow the steps in the video below:
How to use a VPN to Unblock Netflix🇺🇸The best Netflix VPNs Teste...

How to tell your Netflix VPN is working
A few years ago, it was easy to tell whether your VPN was working correctly with Netflix. This was because of the error message Netflix served to VPN users asking them to disconnect. Nowadays, Netflix takes a different tactic, showing subscribers using VPNs only the shows and movies that it has a global license for (primarily just Netflix originals).
This can cause confusion, and make VPN users believe that they've successfully accessed a different Netflix region. In reality, they're just being served a special, restricted Netflix library – without any region-locked content.
Obviously, this defeats the purpose of using a VPN to access international content libraries! We recommend following the steps in this guide to connect to Netflix via your VPN. Then, search for movie or TV titles that you know are unique to the region you're accessing.
To help, we have listed some regionally exclusive titles that you can search for below:
If you can stream the titles mentioned above while connected to your chosen Netflix region – your Netflix VPN is working correctly.
How we pick the best VPNs for Netflix - VPN testing methodology
Netflix works hard to block VPNs. This means there are very few services that work. This makes it difficult for consumers to confidently pick a VPN to stream Netflix on vacation.
In addition, many VPNs lie about the level of protection they provide. They also exaggerate how fast they are, which makes it hard to tell if the VPN is good for tasks like HD streaming on Netflix.
To guarantee that we always provide accurate recommendations, our experts use a dedicated VPN testing methodology. Our review process has been developed over many years and uses precise metrics to ascertain which VPN is better.
To this end, we check a VPN’s apps, test its security features, analyze the privacy policy, and test that the VPN has everything you require to play games, make video calls, or stream in HD.
Below, we have included some of the things we looked for when recommending the best VPNs for Netflix:
- Servers in the US and elsewhere that work to stream Netflix with the proxy error message.
- The ability to access not just Netflix but as many popular streaming platforms as possible. This includes BBC iPlayer, Disney Plus, Hulu, and HBO Max.
- Fast servers and VPN protocols, such as WireGuard, optimized for streaming.
- The ability to quickly bypass the Netflix VPN blocks to keep providing access for their users.
- Strong AES encryption, a kill-switch, DNS leak protection, and other security features needed to gain online privacy at home and on public WiFi.
- Privacy levels you can count on to watch Netflix at work or on another restricted network without being monitored.
- Secure apps for all platforms to let you stream Netflix on any device.
Do all VPNs work with Netflix?
Unfortunately not. Netflix invests a lot of time and money into blocking VPNs, and it does so because some of its content has licensing restrictions, meaning it can only be shown is certain regions.
Each year, Netflix gets better at blocking IP addresses associated with VPN providers. This results in fewer VPNs providing reliable access to the service. As a result, using a VPN that isn't listed on this page will likely result in the following Netflix error message:
Whoops, something went wrong. Streaming error. You seem to be using an unblocker or proxy. Please turn off any of these services and try again.
If you see this message, it means that Netflix knows you're using a VPN, and will prevent you from streaming any content until you disconnect. Our recommended VPNs understand the importance of consistently providing access to Netflix, though, and work ceaselessly to keep maintaining servers that can access all sorts of global libraries.
If your VPN is not working with Netflix, check out our Netflix VPN Troubleshooting guide for some handy tricks to get it working again.
VPNs that DON'T work with Netflix
Many well-known services (Avast Secureline, Kaspersky Secure Connection, Buffered, and TunnelBear – to name a few) don’t even try to bypass Netflix restrictions!
Below you'll find some providers you can write off immediately.
| Provider | Reason |
|---|---|
| Buffered | Stopped working September 2017 |
| Blockless | Stopped working July 2016 |
| CactusVPN | Stopped working July 2016 |
| GetFlix | Despite its name, this provider only worked for a few months |
| HideIPVPN | Stopped working July 2016 |
| Hola | An untrustworthy service altogether |
| IronSocket | Stopped working July 2016 |
| Overplay | Stopped working July 2016 |
| Tunnelbear | Never worked with Netflix |
| Unotelly | Stopped working July 2016 |
Conclusion
Now that we've covered which VPNs work with Netflix and which don't, let's review our top picks:
FAQs









