What is a VPN?
A Virtual Private Network, or VPN, is a piece of software that changes your IP address and encrypts all of your internet traffic. This helps to improve your online privacy and security, as well as allowing you to bypass online censorship imposed by the government, ISPs or any other organization or person trying to restrict access to the internet.
What is a VPN Used For and How Does a VPN Work? ProPrivacy Explains �...

Benefits of using a VPN
Signing up to a VPN service will give you several benefits. These include:
It prevents your internet provider (ISP) from seeing what you get up to online
This also makes it very good at preventing blanket government surveillance of the kind carried out by America's NSA.
In addition to this, websites cannot see your real IP address or who your ISP is. All they can see is the IP address of the VPN server, which is usually shared among many VPN users to further protect each individual user.
Unlike ISPs, reputable VPN services do not keep logs of your information for later retrieval. Indeed, a good deal of privacy-focused VPN services go further, and make of point of deleting all metadata connection logs. This ensures they have nothing that can directly or indirectly link customers to their activity on the internet.
It prevents websites from seeing your IP address
Your Internet Protocol Address or IP Address is how you can be identified online. When you use a VPN, your real IP address is replaced with the IP address of the VPN server you're connected to, making it more difficult for websites to identify you.
This goes a long way towards protecting your privacy when surfing the web. And it also makes it more difficult for advertisers to target you with adverts.
It helps you defeat censorship
A VPN lets you bypass censorship, be it by a repressive regime, or your college or office network admins. Using a VPN allows you to access restricted websites by connecting to a VPN server located somewhere where the content is freely available.
It allows you to access different streaming service libraries
A VPN lets you access foreign streaming services that are blocked or geo-restricted in your country, no matter where you are really located. Just connect to a VPN server in the country, and as far as the internet is concerned, you're there!
For example, by connecting to a VPN server in the United States you can unblock a wide range of US-only Netflix content. The American version of the service has more TV shows and movies than any other country's Netflix catalog. This is why it has become popular for people to use a VPN with Netflix.
As well as streaming Netflix content not available in your location, you can use a VPN to unblock YouTube videos and much more. This works by enabling you to get around regional restrictions by pretending to be in a country where the video you want to watch is not blocked.
Or, if you use a VPN server in the UK, you can watch BBC iPlayer abroad for free.
Protects you from hackers
How do you know the Wi-Fi at your local coffee shop is secure? Answer... you don't. This goes for free public Wi-Fi no matter where you use it. Using insecure Wi-Fi is an open invitation for criminal hackers to try and steal your data.
A VPN will protect you when using all forms of public Wi-Fi because your data is securely encrypted.
Protects you when P2P torrenting
When you use a VPN for torrenting your real IP address is hidden from peers downloading the same torrents, as well as any malicious actors who might want to attack your system or steal your data.
How to use a VPN
The mechanics of using a VPN are simple, and no matter which platform you use should go something like this:
- Sign-up for a VPN plan through the provider's website.
- Download and install the software on your device. VPN software on desktop computers is often referred to as a VPN client, while software for mobile devices is called a VPN app. In reality, they are the same thing and we treat the terms interchangeably.
- Run the app or client and sign in with the login details you used when you purchased the subscription.
- Many VPN apps feature a big friendly "Connect" button. Simply click on or tap it to connect to a nearby VPN server selected by your VPN provider. This will almost certainly provide the fastest VPN connection available.
Need more control?
If you want to use a server in a different country, some VPNs have a map so you can simply click the country to want to connect to on the map. If your VPN doesn't have this, click the menu button and this will show you the list of VPN servers the VPN has.
How does a VPN work?
When you start your VPN client, it connects to a server run by a VPN provider. All data into and out of your device is securely encrypted and routed through this "VPN tunnel".
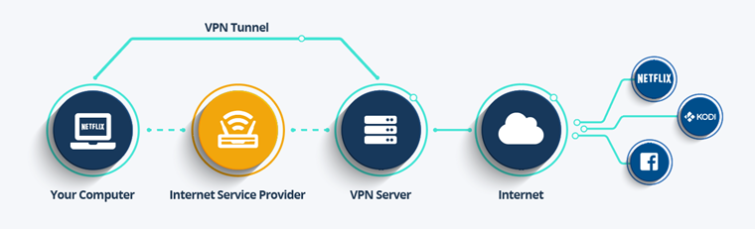
The VPN server acts as a gateway between you and the internet. It prevents entities such as your ISP or government agencies from seeing what you get up to on the internet, and it prevents websites on the internet from seeing who you are or where in the world you are located.
You still need your regular internet connection to get to the VPN server, but because all data passing through the VPN tunnel to the server is encrypted, your ISP cannot see the contents of your data, which is handy if your ISP engages in bandwidth throttling (also known as "traffic shaping"). Now you can stream to your heart's content without worrying about your ISP restricting your connection.
This deceptively simple setup provides lots of advantages.
Does a VPN make me anonymous?
No matter what the adverts claim, VPNs provide privacy, not anonymity. This is mainly because the VPN server can see everything that your ISP normally can.
Unlike your ISP, good VPNs do not log any information and therefore provide much higher levels of privacy than you normally have when surfing the internet. Even these no-log providers, however, will start to log information if subpoenaed or issued a binding court order.
After all, no VPN employee is going to risk going to jail for a stranger on the internet! Does this mean VPNs are useless for privacy? Not at all. Such legal moves are usually targeted specifically towards individuals of interest, so are not a threat to the privacy of most ordinary VPN users.
The Edward Snowden's of this world, however, who require very high levels of true anonymity, should use the Tor Network rather than VPNs to protect their identity.
How to configure your VPN?
VPN software is designed to be easy to use, and should "just work" without the need for any additional configuration. Unfortunately, this is not always the case as there are so many different configurations of hardware and software out there.
This is especially true if you have an IPv6 internet connection as some VPN apps struggle to handle this new internet standard correctly. It is therefore always a good idea to check that your VPN is correctly configured to protect you as it is supposed to.
What is a kill-switch?
Thanks to the vagaries of the internet, VPN connections sometimes fail. In the normal course of events, when this happens, you will remain connected to the internet but without the protection of the VPN.
A kill switch protects you against this by preventing connections into and out of your device unless the VPN connection is active, ensuring that your real IP and location are never accidentally exposed to the world at large.
Will a VPN slow down my internet?
A VPN routes your data through a VPN server, which must then spend processing power encrypting and decrypting the data before it is then routed on to the rest of the internet. It is therefore inevitable that using a VPN will slow down your internet connection at least a little.
The two biggest factors at play are the distance to the VPN server and how loaded the VPN server is with other users. If you connect to a server near to you which is not overloaded, then you can expect to lose around 10 percent of your base internet speed. However, the Fastest VPNs invest heavily in high-speed servers so you don't have to deal with a slow internet connection.
Do I need an ISP if I use a VPN?
Yes.
An ISP, or Internet Service Provider, supplies your internet connection and is required to connect you to the VPN server.
Can I use a VPN on all my devices?
Every VPN provider allows you to install its software on as many devices as you like. Most, however, limit how many devices you can use at the same time with a single account. We refer to the number of devices a VPN allows you to use at once as the number of "simultaneous connections" it permits.
VPNs typically allow up to five simultaneous connections, although this number can vary considerably with some offering a lot more.
The majority of VPN services offer iOS VPN apps as well as VPNs for Android users, however, it may be difficult to find support for less popular mobile operating systems. When it comes to computer clients, most VPN services support Windows and Mac users, but Linux VPN clients can be more difficult to find, with most only offering command-line options rather than full GUI clients.
Can I get a free VPN?
For a long time, it was something of a truism that "if you don't pay for a product then you are the product". At best, you could use a limited free service that was little more than a taster for a paid-for service you might actually want to use.
This situation has changed over the last couple of years, and there are now at least a couple of free VPN services out there which are actually quite good. Even these are limited in various ways, though, compared to more premium services. We have found that cheap VPN services are among the best on the market. VPNs with the most sought-after features can be found for less than $2 a month.
Does a VPN make me safe?
In short, Yes.
A VPN will make you safe from:
- Public Wi-Fi hackers
- Your ISP
- Mass government surveillance
- Commercial Wi-Fi operators who sell your browsing habits for profit
- Advertising and analytics companies who store your data to target you with Ads (if used in combination with anti-tracker browser add-ons).
Looking for the best VPNs?
Here's a quick summary of our top picks for VPN services:
- ExpressVPN - The best VPN overall. Provides top-notch security and geo-spoofing features. A lightning fast service, with a 30-day money-back guarantee.
- NordVPN - The best buy VPN. It offers plenty of servers, premium features, and great speeds. All that at prices that are budget-friendly.
- Surfshark - Highly customizable VPN. Offers fast speeds for streaming, slick apps for all platforms, and unlimited simultaneous connections.
- Private Internet Access - Robust and secure VPN, suitable for VPN beginners and tech-savvy users alike. It's cheap, with impressive server network.
- PrivateVPN - The cheapest private VPN. Offers strong encryption and a strict zero-logs privacy policy. Works with plethora of websites.
VPNs beginner's guide – FAQs
In this section we answer your other most frequently asked questions.
